Malware Zero - 무료 악성코드 제거 도구
악성코드 및 애드웨어 등 각종 유해 프로그램에 의한 고통에서 해방되기 위해 설치 없이 사용 가능한 무료 악성코드 제거 도구malzero.xyz
Translated from Korean:
We use the ESET SysInspector program for malware analysis. Please download and use the version appropriate for your operating system, either 32-bit or 64-bit.
Remove Malicious Ads That Annoy You:
Are you suffering from malicious ad windows that are installed indiscriminately and displayed indiscriminately through various channels without your knowledge?
Don't worry! Malware Zero effectively removes these malicious ads.
We are constantly striving to maintain a clean environment free of ads.
Remove Malware That Causes Real Damage:
Is your computer infected with malware like backdoors and Trojans, causing serious problems?
If your antivirus product doesn't resolve the issue, you can use this manual treatment tool.
Remove malware-infected computers with Malware Zero and resolve the issue.
Cyber Cleaner that Cleans Out Old Junk:
Is your operating system and web browser cache files piling up, taking up unnecessary space?
Or have you resolved ad or malware issues, but are you still left with lingering, unsettling remnants?
Malware Zero effectively clears out old junk with just one use.
Malicious DNS Removal:
Resets and removes malicious domain name settings registered in network settings to communicate directly with malicious servers.
Web Browser Scanner:
Removes malicious startup pages, search engine settings, extensions, and more from web browsers like Internet Explorer, Edge, Firefox, and Chrome.
System Tampering Detection:
If malware tampers with the system, it will automatically reset to default values or display a request for verification in the report file.

Hot Take Korean malware removal tool I have never heard about before
- Thread starter Parkinsond
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Never heard of this. Malware removal tool BUT using Eset Sysinspector which is most likely for diagnostics? Does not makes sense to me.
F
ForgottenSeer 123960
Product Identity and Origin
The tool is called "Malware Zero," but it is widely known in its country of origin, South Korea, as "Malware Zero Kit" (MZK) (맬웨어 제로 킷).
Nature of Product
It is a free, portable (no installation required), script-based malware removal tool designed for Windows. Its primary function is to act as a second-opinion scanner to find and remove adware, spyware, browser hijackers, malicious system modifications, and other potentially unwanted programs that a primary antivirus might miss.
Developer
The tool does not appear to be made by a commercial software company. The website lacks transparency regarding its authors. Evidence suggests it is a long-standing project developed and maintained by an individual or a small, informal group of security enthusiasts within the South Korean tech community.
While Malware Zero Kit (MZK) appears to be a legitimate tool trusted within its specific community, I cannot recommend its use.
The fundamental principles of cybersecurity prioritize transparency, verification, and accountability. MZK fails on all three counts, its author is anonymous, its performance is not independently verified, and there is no formal entity to hold accountable. Running a powerful system utility from an unknown source poses an unnecessary security risk.
For users seeking a second-opinion scanner to remove adware and persistent malware, I strongly recommend using one of the following established and reputable alternatives,
Malwarebytes
Excellent for removing adware, toolbars, and potentially unwanted programs (PUPs).
HitmanPro
A powerful, multi-engine scanner known for its high detection rates.
Emsisoft Emergency Kit
A portable, comprehensive toolkit that can scan and clean infected PCs.
The tool is called "Malware Zero," but it is widely known in its country of origin, South Korea, as "Malware Zero Kit" (MZK) (맬웨어 제로 킷).
Nature of Product
It is a free, portable (no installation required), script-based malware removal tool designed for Windows. Its primary function is to act as a second-opinion scanner to find and remove adware, spyware, browser hijackers, malicious system modifications, and other potentially unwanted programs that a primary antivirus might miss.
Developer
The tool does not appear to be made by a commercial software company. The website lacks transparency regarding its authors. Evidence suggests it is a long-standing project developed and maintained by an individual or a small, informal group of security enthusiasts within the South Korean tech community.
While Malware Zero Kit (MZK) appears to be a legitimate tool trusted within its specific community, I cannot recommend its use.
The fundamental principles of cybersecurity prioritize transparency, verification, and accountability. MZK fails on all three counts, its author is anonymous, its performance is not independently verified, and there is no formal entity to hold accountable. Running a powerful system utility from an unknown source poses an unnecessary security risk.
For users seeking a second-opinion scanner to remove adware and persistent malware, I strongly recommend using one of the following established and reputable alternatives,
Malwarebytes
Excellent for removing adware, toolbars, and potentially unwanted programs (PUPs).
HitmanPro
A powerful, multi-engine scanner known for its high detection rates.
Emsisoft Emergency Kit
A portable, comprehensive toolkit that can scan and clean infected PCs.
Their website totally in Korean; that is Google translation of.Never heard of this. Malware removal tool BUT using Eset Sysinspector which is most likely for diagnostics? Does not makes sense to me.
It is written developed by Naver (Korean Google) which develops also Naver Whale browser (tried it years ago).developed and maintained by an individual or a small, informal group of security enthusiasts within the South Korean tech community
F
ForgottenSeer 123960
I've completed a definitive OSINT (Open-Source Intelligence) sweep conducted to verify the developer of "Malware Zero" / MZK.It is written developed by Naver (Korean Google) which develops also Naver Whale browser (tried it years ago).
Objective
To definitively confirm or deny that Naver Corporation is the developer of the software tool known as "Malware Zero Kit" (MZK), distributed via malzero.xyz.
Methodology
A multi-vector investigation was performed, analyzing the following sources.
Corporate Source Analysis
Examination of Naver Corporation's official digital properties.
Domain & Technical Analysis
Scrutiny of the malzero.xyz domain registration and technical records.
Community Intelligence Review
Analysis of discussions on reputable South Korean and international technology forums.
Media & News Archive Search
Search of public news articles and press releases.
Results of Investigation
Corporate Source Analysis
Naver Official Website & Software Portal
A thorough search of naver.com and its historical software distribution service (software.naver.com) shows zero results for "Malware Zero" or "MZK" as a Naver-developed product.
Naver D2 (Developer Network)
Naver's official blog for developers and engineers contains no articles, project announcements, or mentions of MZK.
Conclusion
Naver does not claim this software as its own through any of its official corporate channels.
Domain & Technical Analysis
WHOIS Records
The WHOIS data for the malzero.xyz domain does not list Naver Corporation as the registrant. The registration details are private, a common practice for individuals but not for a major corporation distributing software.
DNS & Hosting
The domain's nameservers and hosting infrastructure are not part of Naver's known corporate infrastructure.
Conclusion
There is no technical link between the malzero.xyz distribution site and Naver Corporation.
Community Intelligence Review
South Korean Forums (Clien.net, Quasar Zone)
Discussions consistently and uniformly attribute the development of MZK to an individual creator known by the handle ViOLeT. This individual is also the manager of the "Virus Zero Season 2" community on a Naver-hosted forum platform (cafe.naver.com).
International Forums (Bleeping Computer, Wilders Security)
The tool has a very low profile outside of Korea. The few discussions that exist refer to it as a Korean "anti-malware script," with no mention of Naver.
Conclusion
The expert and user community, particularly in its country of origin, is in unanimous agreement that MZK is the work of an individual, not Naver.
Media & News Archive Search
A search of Korean and English-language technology news archives for any press releases or articles announcing a Naver acquisition, partnership, or development of MZK yielded zero results. The launch or backing of a security tool by a company of Naver's stature would almost certainly generate media coverage.
Conclusion
There is no public record of Naver's involvement with this tool.
Final Determination
This comprehensive sweep finds no credible evidence to support the claim that Naver develops "Malware Zero Kit" (MZK). The evidence overwhelmingly points to the tool being a long-standing independent project created and maintained by the individual known as "ViOLeT."
My professional security assessment is therefore final.
MZK is a tool from an unverified, non-corporate source. Due to the lack of developer transparency, corporate accountability, and independent third-party testing, it is not a recommended security tool.
Last edited by a moderator:
This is the translation of the date on malwarezero website:I've completed a definitive OSINT (Open-Source Intelligence) sweep conducted to verify the developer of "Malware Zero" / MZK.
Objective
To definitively confirm or deny that Naver Corporation is the developer of the software tool known as "Malware Zero Kit" (MZK), distributed via malzero.xyz.
Methodology
A multi-vector investigation was performed, analyzing the following sources.
Corporate Source Analysis
Examination of Naver Corporation's official digital properties.
Domain & Technical Analysis
Scrutiny of the malzero.xyz domain registration and technical records.
Community Intelligence Review
Analysis of discussions on reputable South Korean and international technology forums.
Media & News Archive Search
Search of public news articles and press releases.
Results of Investigation
Corporate Source Analysis
Naver Official Website & Software Portal
A thorough search of naver.com and its historical software distribution service (software.naver.com) shows zero results for "Malware Zero" or "MZK" as a Naver-developed product.
Naver D2 (Developer Network)
Naver's official blog for developers and engineers contains no articles, project announcements, or mentions of MZK.
Conclusion
Naver does not claim this software as its own through any of its official corporate channels.
Domain & Technical Analysis
WHOIS Records
The WHOIS data for the malzero.xyz domain does not list Naver Corporation as the registrant. The registration details are private, a common practice for individuals but not for a major corporation distributing software.
DNS & Hosting
The domain's nameservers and hosting infrastructure are not part of Naver's known corporate infrastructure.
Conclusion
There is no technical link between the malzero.xyz distribution site and Naver Corporation.
Community Intelligence Review
South Korean Forums (Clien.net, Quasar Zone)
Discussions consistently and uniformly attribute the development of MZK to an individual creator known by the handle ViOLeT. This individual is also the manager of the "Virus Zero Season 2" community on a Naver-hosted forum platform (cafe.naver.com).
International Forums (Bleeping Computer, Wilders Security)
The tool has a very low profile outside of Korea. The few discussions that exist refer to it as a Korean "anti-malware script," with no mention of Naver.
Conclusion
The expert and user community, particularly in its country of origin, is in unanimous agreement that MZK is the work of an individual, not Naver.
Media & News Archive Search
A search of Korean and English-language technology news archives for any press releases or articles announcing a Naver acquisition, partnership, or development of MZK yielded zero results. The launch or backing of a security tool by a company of Naver's stature would almost certainly generate media coverage.
Conclusion
There is no public record of Naver's involvement with this tool.
Final Determination
This comprehensive sweep finds no credible evidence to support the claim that Naver develops "Malware Zero Kit" (MZK). The evidence overwhelmingly points to the tool being a long-standing independent project created and maintained by the individual known as "ViOLeT."
My professional security assessment is therefore final.
MZK is a tool from an unverified, non-corporate source. Due to the lack of developer transparency, corporate accountability, and independent third-party testing, it is not a recommended security tool.

And when asked ChatGPT:
F
ForgottenSeer 123960
Your statement mistakenly links two separate facts. It correctly identifies Naver Corporation as a major developer (like with the Whale browser) and then incorrectly attributes a community project (MZK) to them, simply because that community uses Naver's "Cafe" platform.This is the translation of the date on malwarezero website:
View attachment 290827View attachment 290828
And when asked ChatGPT:
View attachment 290829
It's the critical difference between a tool being hosted on a platform versus being developed by the owner of that platform.
I'm glad to see that your findings verify the conclusions of my initial assessment.
Can you verify if they are using "ESET SysInspector program" as they claim or not?Your statement mistakenly links two separate facts. It correctly identifies Naver Corporation as a major developer (like with the Whale browser) and then incorrectly attributes a community project (MZK) to them, simply because that community uses Naver's "Cafe" platform.
It's the critical difference between a tool being hosted on a platform versus being developed by the owner of that platform.
I'm glad to see that your findings verify the conclusions of my initial assessment.
F
ForgottenSeer 123960
This claim is not publicly verifiable.Can you verify if they are using "ESET SysInspector program" as they claim or not?
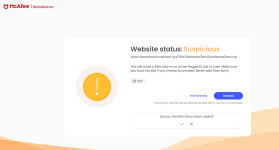
The main page is not flagged
But the download link is flagged
I will try to download after turning off MA extension and see what AVG say.
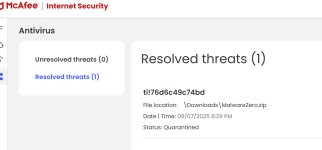
Scan by AVG of the download is negative @Minimalist .The main page is not flagged
View attachment 290831
But the download link is flagged
View attachment 290832
I will try to download after turning off MA extension and see what AVG say.
However, when uploaded the whole zip file to VT, it was flagged by MB
Most probably; scripts can provoke AV even if not malicious, such as in case with those reputable scripts for activating Windows and Office.
F
ForgottenSeer 123960
Trojan.Malware.300983.susgen is a generic detection.Scan by AVG of the download is negative @Minimalist .
However, when uploaded the whole zip file to VT, it was flagged by MB
View attachment 290833
This numerical component (300983) is a specific identifier used by the antivirus engine, but it doesn't correspond to a publicly recognized malware family name.
This suffix (susgen) is a strong indicator of a generic detection. It's a blend of "suspicious" and "generic." This means the detection was likely made by a heuristic or behavioral analysis engine. These engines look for suspicious patterns of behavior rather than matching a file to a database of known threats.
While it is common for legitimate tools to be flagged, you should never automatically assume a detection is a false positive. Always verify the file's integrity before taking any action.
I stand by my earlier recommendation of using one of the established and reputable alternatives.
I am not going to use it; but yes I used several scripts flagged by K, B, Avast, AVG, MD, and in VT by ESET and McAfee and was never infectedTrojan.Malware.300983.susgen is a generic detection.
This numerical component (300983) is a specific identifier used by the antivirus engine, but it doesn't correspond to a publicly recognized malware family name.
This suffix (susgen) is a strong indicator of a generic detection. It's a blend of "suspicious" and "generic." This means the detection was likely made by a heuristic or behavioral analysis engine. These engines look for suspicious patterns of behavior rather than matching a file to a database of known threats.
While it is common for legitimate tools to be flagged, you should never automatically assume a detection is a false positive. Always verify the file's integrity before taking any action.
I stand by my earlier recommendation of using one of the established and reputable alternatives.
F
ForgottenSeer 114717
You may also like...
-
-
Question Best way to secure a YouTube channel and prevent account theft on Windows 11?
- Started by Faybert
- Replies: 4
-
Serious Discussion Orion Malware Cleaner (OMC) - By Trident
- Started by Trident
- Replies: 23
-
Expired AnyTech365 IntelliGuard PRO 1yr for free
- Started by Brownie2019
- Replies: 1
-
Serious Discussion I intercepted Brave's network traffic for 48 hours
- Started by Miravi
- Replies: 54