- Content source
- http://net-security.org/secworld.php?id=19340
Security researcher (and Praesido CTO) Sean Cassidy has demonstrated at ShmooCon how easy it can be for hackers to steal LastPass users' email, password, and two-factor authentication code via a simple phishing attack.
With this information in hand, the attackers can access the victim's LastPass vault and all the information in it - passwords, sensitive info, etc. - without the victim's knowledge, and change certain settings so that they continue to have access to it in the future.
The attack - dubbed LostPass by Cassidy - relies on the fact that LastPass effectively trained users to expect notifications in the browser viewport (the area below the tab bar and URL address bar (as seen here):
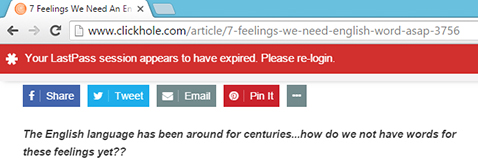
The LastPass login screen and two-factor prompt are shown in the viewport as well.
By luring victims to a malicious website or a real one that is vulnerable to XSS, the attackers are able to show a fake login expired notification. Due to the fact that LastPass is also vulnerable to a logout CSRF flaw, the website can also log any user out of LastPass, so the fake notification is even more convincing.
"Once the victim clicks on the fake banner, direct them to an attacker-controlled login page that looks identical to the LastPass one," Cassidyexplained.
"The victim will enter their password and send the credentials to the attacker's server. The attacker's server will check if the credentials are correct by calling LastPass's API. The API will inform us if two-factor authentication is required."
Read more: LostPass: A worryingly simple phishing attack aimed at LastPass users
With this information in hand, the attackers can access the victim's LastPass vault and all the information in it - passwords, sensitive info, etc. - without the victim's knowledge, and change certain settings so that they continue to have access to it in the future.
The attack - dubbed LostPass by Cassidy - relies on the fact that LastPass effectively trained users to expect notifications in the browser viewport (the area below the tab bar and URL address bar (as seen here):
The LastPass login screen and two-factor prompt are shown in the viewport as well.
By luring victims to a malicious website or a real one that is vulnerable to XSS, the attackers are able to show a fake login expired notification. Due to the fact that LastPass is also vulnerable to a logout CSRF flaw, the website can also log any user out of LastPass, so the fake notification is even more convincing.
"Once the victim clicks on the fake banner, direct them to an attacker-controlled login page that looks identical to the LastPass one," Cassidyexplained.
"The victim will enter their password and send the credentials to the attacker's server. The attacker's server will check if the credentials are correct by calling LastPass's API. The API will inform us if two-factor authentication is required."
Read more: LostPass: A worryingly simple phishing attack aimed at LastPass users