silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,235
Hacked corporate sites and news blogs running using the WordPress CMS are being used by attackers to deliver backdoor malware that allows them to drop several second-stage payloads such as keyloggers, info stealers, and Trojans.
After gaining admin access to the compromised WordPress websites, the hackers inject malicious JavaScript code that will automatically redirect visitors to phishing sites.
These landing pages are designed to look like a legitimate Google Chrome update page and are used by the attackers to instruct potential victims to download an update for their browser.
However, instead of a Chrome update, the targets will download malware installers that will infect their devices and will allow the operators behind this campaign to take control of their computers remotely.
Once executed, the malware installer drops a TeamViewer installation and unarchives two password-protected SFX archives containing the files needed to open the fake update page and to allow remote connections, as well as a script used by the malware to bypass the Windows built-in antivirus.
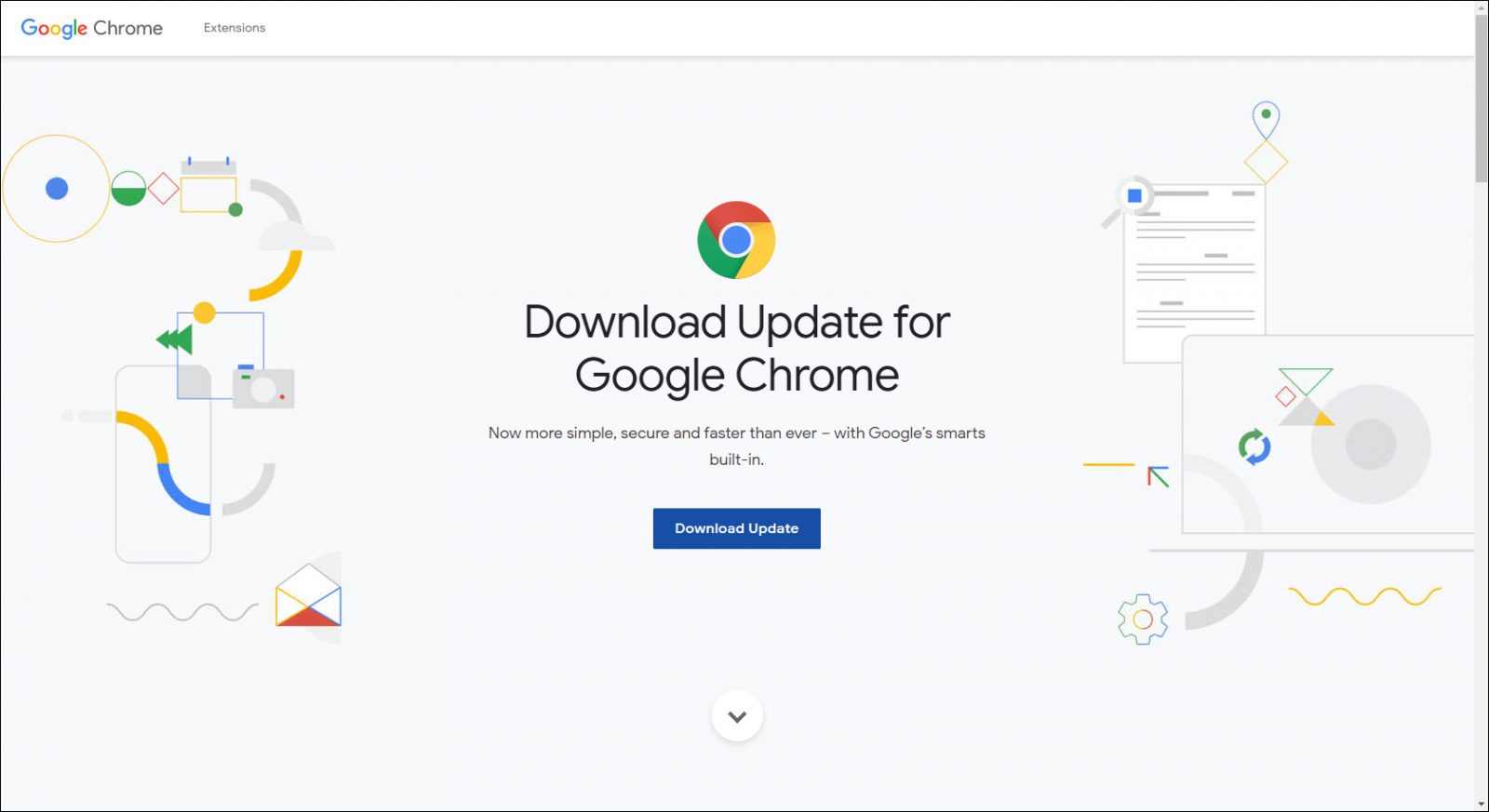
Fake Chrome update page (Doctor Web)
Cybercriminals spread dangerous backdoor as Google Chrome update
Doctor Web virus analysts report that certain websites, from online news blogs to corporate pages created using WordPress CMS, have been compromised. The JavaScript script embedded in the hacked pages code redirects visitors to a phishing site where they are prompted to install an important...
