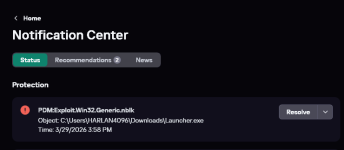
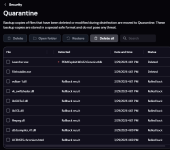
this should be a reminder to everybody on this planet that the best antivirus is common sense.
Obviously this isn't just a Malwarebytes hate post but also condemning every antivirus that people pay for.
I just happen to be a paying member of Malwarebytes and if my money can't detect obvious script kiddie virus I wonder if it's even worth paying for continuously
Source:
Code:
https://www.reddit.com/r/antivirus/comments/1s6o3ip/malwarebytes_proving_to_be_a_disappointment/
Last edited by a moderator: