Intel® Management Engine (Intel® ME 6.x/7.x/8.x/9.x/10.x/11.x), Intel® Trusted Execution Engine (Intel® TXE 3.0), and Intel® Server Platform Services (Intel® SPS 4.0) vulnerability (Intel-SA-00086)
In response to issues identified by external researchers, Intel has performed an in-depth comprehensive security review of the following with the objective of enhancing firmware resilience:
Systems using Intel ME Firmware versions 6.x-11.x, servers using SPS Firmware version 4.0, and systems using TXE version 3.0 are impacted. You may find these firmware versions on certain processors from the:
Available resources
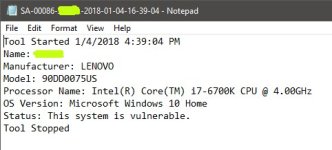
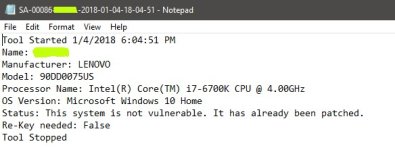
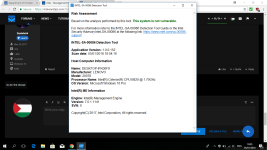
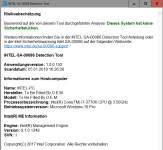
Note Versions of the INTEL-SA-00086 Detection Tool earlier than 1.0.0.146 did not check for CVE-2017-5711 and CVE-2017-5712. These CVEs only affect systems with Intel® Active Management Technology (Intel® AMT) version 8.x-10.x. Users of systems with Intel AMT 8.x-10.x are encouraged to install version 1.0.0.146, or later. Installing this version helps to verify the status of their system with regard to the INTEL-SA-00086 Security Advisory. You can check the version of the INTEL-SA-00086 Detection Tool by running the tool and looking for the version information in the output window.
Resources from system/motherboard manufacturers
Note Links for other system/motherboard manufacturers will be provided when available. If your manufacturer is not listed, contact them for information on the availability of the necessary software update.
In response to issues identified by external researchers, Intel has performed an in-depth comprehensive security review of the following with the objective of enhancing firmware resilience:
- Intel® Management Engine (Intel® ME)
- Intel® Trusted Execution Engine (Intel® TXE)
- Intel® Server Platform Services (SPS)
Systems using Intel ME Firmware versions 6.x-11.x, servers using SPS Firmware version 4.0, and systems using TXE version 3.0 are impacted. You may find these firmware versions on certain processors from the:
- 1st, 2nd, 3rd, 4th, 5th, 6th, 7th, and 8th generation Intel® Core™ Processor Families
- Intel® Xeon® Processor E3-1200 v5 and v6 Product Family
- Intel® Xeon® Processor Scalable Family
- Intel® Xeon® Processor W Family
- Intel Atom® C3000 Processor Family
- Apollo Lake Intel Atom® Processor E3900 series
- Apollo Lake Intel® Pentium® Processors
- Intel® Pentium® Processor G Series
- Intel® Celeron® G, N, and J series Processors
Available resources
- Intel official security advisory: Technical details on the vulnerability
Note Versions of the INTEL-SA-00086 Detection Tool earlier than 1.0.0.146 did not check for CVE-2017-5711 and CVE-2017-5712. These CVEs only affect systems with Intel® Active Management Technology (Intel® AMT) version 8.x-10.x. Users of systems with Intel AMT 8.x-10.x are encouraged to install version 1.0.0.146, or later. Installing this version helps to verify the status of their system with regard to the INTEL-SA-00086 Security Advisory. You can check the version of the INTEL-SA-00086 Detection Tool by running the tool and looking for the version information in the output window.
Resources from system/motherboard manufacturers
Note Links for other system/motherboard manufacturers will be provided when available. If your manufacturer is not listed, contact them for information on the availability of the necessary software update.
- Acer: Support Information
- ASRock: Support Information
- ASUS: Support Information
- Compulab: Support Information
- Dell Client: Support Information
- Dell Server: Support Information
- Fujitsu: Support Information
- Getac: Support Information
- GIGABYTE: Support Information
- HP Inc.: Support Information
- HPE Servers: Support Information
- Intel® NUC, Intel® Compute Stick, and Intel® Compute Card: Support Information
- Intel® Servers: Support Information
- Lenovo: Support Information
- Microsoft Surface*: Support Information
- MSI: Support Information
- NEC: Support Information
- Oracle: Support Information
- Panasonic: Support Information
- Quanta/QCT: Support Information
- Supermicro: Support Information
- Toshiba: Support Information
- Vaio: Support Information
- Wiwynn: Support Information