How to tell if you are affected
The CVE-2020-0951 vulnerability affects both PowerShell 7 and PowerShell 7.1 versions, while CVE-2021-41355 only impacts users of PowerShell 7.1.
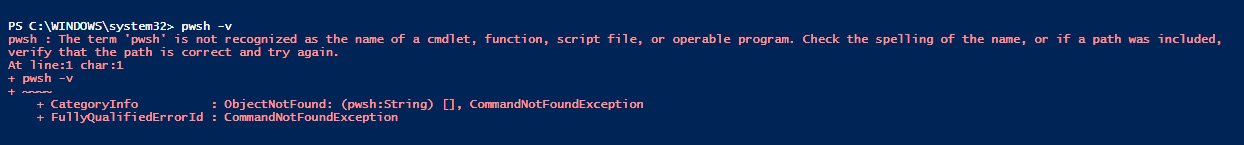
To check the PowerShell version you are running and determine if you are vulnerable to attacks exploiting these two bugs, you can execute the pwsh -v command from a Command Prompt.
Microsoft says no mitigation measures are currently available to block the exploitation of these security flaws.
Admins are advised to install the updated PowerShell
7.0.8 and
7.1.5 versions as soon as possible to protect systems from potential attacks.