Hmm. If all this stuff is hard coded, it might not be that useful to me. Have to think about it.
Need your input for NEW zero config application sandbox
- Thread starter Windows_Security
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Windows_Security
Level 24
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Libraries are an existing windows mechanism which the user can change. You can add folders to the libraries, even drives, so what is the problem?
Not as much a problem as just use of them is useless for me. Maybe I do need to explain my setup.
I have 3 internal drives. C: is my system and has all my critical data. The other two drives contain image backups and other data like video files. I system is protected EIS,Appguard, Hmpa and I use SBIE for browsing. I also use MZwritescanner For further protection on my c: drive I image hourly, so I can restore easily. For the other two drives I protect the two drives data with Pumpernickel(Fides)
So basically a solution that requires total reorganization of my systems isn't worth the bother. This is MY problem with the solution you are proposing.
I have 3 internal drives. C: is my system and has all my critical data. The other two drives contain image backups and other data like video files. I system is protected EIS,Appguard, Hmpa and I use SBIE for browsing. I also use MZwritescanner For further protection on my c: drive I image hourly, so I can restore easily. For the other two drives I protect the two drives data with Pumpernickel(Fides)
So basically a solution that requires total reorganization of my systems isn't worth the bother. This is MY problem with the solution you are proposing.
Windows_Security
Level 24
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
I did not expect you in the target market for a zero config program directed to PC users which are better of, having no options to fiddle with.
In future when you might find some time to test it in a VM, I would be more than happy.
In future when you might find some time to test it in a VM, I would be more than happy.
Oh heck you know me to well. I will be glad to test it in my vm at the get gowhere I can see how it's working and also let it have some malware.
Windows_Security
Level 24
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Expect at least three months before Florian has developed release 1. He is eager to keep this driver below 1 KLOC* so the average change of having 1 vulnerability in it is near zero. Being members of a security forum we can only applaud Florian's pickiness on clean code. 
* On average software has one error/vulnerability in every 1000 lines of code. iSix-sigma or Six-Sigma-SLDC (Software Development Life Cycle) quality management tries to reduce that to 1 error on every million. On languages with no memory integrity restraints (like C++) all this mumbo-jumbo talk comes down to "just" peer-reviews at coding stage. Fault tracking remains at the end of the Software Development Life Cycle. So iSix-sigma it is just marketing talk (believe me a marketeer recognizes marketing mumbo jumbo well). That is why Mozilla Firefox choosing another programming language captures this problem at the root. Rust has build-in memory integrity enforcement of a high-level programming language while maintaining the speed and command efficiency of C++. Rust simply prevents programmers to make such mistakes.
* On average software has one error/vulnerability in every 1000 lines of code. iSix-sigma or Six-Sigma-SLDC (Software Development Life Cycle) quality management tries to reduce that to 1 error on every million. On languages with no memory integrity restraints (like C++) all this mumbo-jumbo talk comes down to "just" peer-reviews at coding stage. Fault tracking remains at the end of the Software Development Life Cycle. So iSix-sigma it is just marketing talk (believe me a marketeer recognizes marketing mumbo jumbo well). That is why Mozilla Firefox choosing another programming language captures this problem at the root. Rust has build-in memory integrity enforcement of a high-level programming language while maintaining the speed and command efficiency of C++. Rust simply prevents programmers to make such mistakes.
Last edited:
9.jail for registry limit registry acess manageable
10.limit internet for every location except just for white-listed item
11.kill process feature- mode that kill any process not listed in white list lockdown or something like it
10.limit internet for every location except just for white-listed item
11.kill process feature- mode that kill any process not listed in white list lockdown or something like it
Windows_Security
Level 24
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Hi all,
Florian is currently testing the new driver which combines Bouncer, CommandlineScanner and MZWriteScanner.. While discussing the functionality of the program we decided for V1 to focus on making Malware Mitigator (that is the working name) a real companion program. While defining the concept the focus moved from generic anti executable and command-line sanitation to blocking software dropped onto your harddisk in an unusual way. The rational behind this change of focus is that 99% of the software you did not ask for is either malware or a potential unwanted program. Because the V2 will also have MemProtect (which protects against fileless malware/creditial kidnap/hollow process also), we are pretty sure Malware Mitigator will have added value for home users while offering the ease of zero configration.
-----------------------------------------------------------------------------------------------------------------------------------------------------------------------
Delay the zero day with Excubits Malware Mitigator.
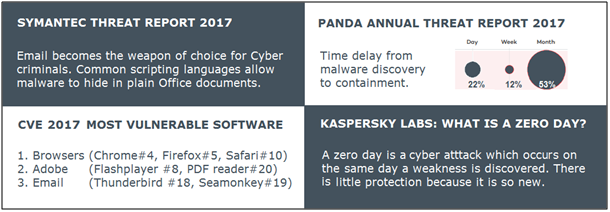
Give your (free) antivirus the time to find a cure for new malware infections. Malware Mitigator blocks strange and unwanted software dropped on your PC by vulnerable and script processing software up to 30 days (user configurable). Malware Mitigator also has build in block rules to prevent scripts in poisoned documents to bypass this 'dropper defense'. This to make sure that programs you did not ask for don't execute in a sneaky way from ordinary documents.
We are looking for members who have any of the following software installed (see guarded programs below listed in blue). We would like to roll out in stages. First stage would be to fine tune the internal rules as much as possible. The first closed beta version will have an Intrusion Detection function only. The driver will only log and the tray-app will only show a warning. This reduces the risk of false positives (first beta blocking legitimate software) to an absolute minimum. German products have a good reputation when it comes to build quality. Florian is no exception, quality comes first.
Guarded products will be typical script processing programs like
The closed beta will probably start in the second half of February. On MalwareTips and the other security forum we will ask some experienced members to actively help develop rules and act as a sort of community coach for that security forum. This is only a pre-announcement to give MalwareTips a scoop.
When there are more people willing to participate than the community coaches can handle (for timely response to questions and requests et cetera) we will give priority/precedence to members with higher forum levels. Florian asked for a fair and transparant judging system which left no room for favoritism (and MT forum level is the most straightforward mechanism I can think of ).
Participating in the closed beta means that you post (part) of the log (which only contains flagged programs) on the forum (when you want to contribute incognito) or by email to Excubits (details on how and what will follow within two weeks). The reward of contributing new (alse positives will be a free license of the final version. The final version will prevent unwanted programs from executing for a user specified number of days. You will be notified when we have validated your FP-report and you are rewarded a free license.
When you are interested in participating, you already can send me a PM, please specify which of the above software you have installed (or make a plead to add one I have not listed) and your current forum level. As mentioned earlier the closed beta acts as an intrusion detection (by logging) and not a intrusion prevention (by blocking). Only flagging software in the closed beta minimizes the risk of false positives/blocking legitimate software.
Florian is currently testing the new driver which combines Bouncer, CommandlineScanner and MZWriteScanner.. While discussing the functionality of the program we decided for V1 to focus on making Malware Mitigator (that is the working name) a real companion program. While defining the concept the focus moved from generic anti executable and command-line sanitation to blocking software dropped onto your harddisk in an unusual way. The rational behind this change of focus is that 99% of the software you did not ask for is either malware or a potential unwanted program. Because the V2 will also have MemProtect (which protects against fileless malware/creditial kidnap/hollow process also), we are pretty sure Malware Mitigator will have added value for home users while offering the ease of zero configration.
-----------------------------------------------------------------------------------------------------------------------------------------------------------------------
Delay the zero day with Excubits Malware Mitigator.
Give your (free) antivirus the time to find a cure for new malware infections. Malware Mitigator blocks strange and unwanted software dropped on your PC by vulnerable and script processing software up to 30 days (user configurable). Malware Mitigator also has build in block rules to prevent scripts in poisoned documents to bypass this 'dropper defense'. This to make sure that programs you did not ask for don't execute in a sneaky way from ordinary documents.
We are looking for members who have any of the following software installed (see guarded programs below listed in blue). We would like to roll out in stages. First stage would be to fine tune the internal rules as much as possible. The first closed beta version will have an Intrusion Detection function only. The driver will only log and the tray-app will only show a warning. This reduces the risk of false positives (first beta blocking legitimate software) to an absolute minimum. German products have a good reputation when it comes to build quality. Florian is no exception, quality comes first.
Guarded products will be typical script processing programs like
- Browsers (searching for members who use Chrome, Firefox, Internet Explorer, Opera, Yandex and ?)
- Office products (asking users of Microsoft Office, Open Office, Libre Office, WPS Office and Free Office to participate).
- PDF-Readers (Adobe, Foxit, Perfect PDF Reader, PDF X-change, Sumatra PDF and ?)
- Media players (Windows Media Player, VLC media player, Foobar2000, Clementine, Winamp, Potplayer, ITunes, SMplayer and ?)
- Mail programs (Outlook, Thunderbird, Opera mail, Mailbird and ?)
The closed beta will probably start in the second half of February. On MalwareTips and the other security forum we will ask some experienced members to actively help develop rules and act as a sort of community coach for that security forum. This is only a pre-announcement to give MalwareTips a scoop.
When there are more people willing to participate than the community coaches can handle (for timely response to questions and requests et cetera) we will give priority/precedence to members with higher forum levels. Florian asked for a fair and transparant judging system which left no room for favoritism (and MT forum level is the most straightforward mechanism I can think of ).
Participating in the closed beta means that you post (part) of the log (which only contains flagged programs) on the forum (when you want to contribute incognito) or by email to Excubits (details on how and what will follow within two weeks). The reward of contributing new (alse positives will be a free license of the final version. The final version will prevent unwanted programs from executing for a user specified number of days. You will be notified when we have validated your FP-report and you are rewarded a free license.
When you are interested in participating, you already can send me a PM, please specify which of the above software you have installed (or make a plead to add one I have not listed) and your current forum level. As mentioned earlier the closed beta acts as an intrusion detection (by logging) and not a intrusion prevention (by blocking). Only flagging software in the closed beta minimizes the risk of false positives/blocking legitimate software.
Last edited:
Windows_Security
Level 24
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
No it is alive and kicking, I just don;t have the time to communicate it, so when someone wants to be the intermediate between Florian and this forum just send me a PM.
I tested the beta and it is working well, just don;t have the time until Q3.
I tested the beta and it is working well, just don;t have the time until Q3.
Windows_Security
Level 24
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Good to know it's still alive. Something like that would be nice to have for my not so tech savy parents.
You may also like...
-
-
-
Expired SwifDoo Christmas 2025: PDF 18 Software Programs for free
- Started by Brownie2019
- Replies: 1
-
App Review Testing Orion Malware Cleaner Designed by Me
- Started by Trident
- Replies: 8
-