silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,176
A new phishing campaign is distributing a double-punch of a LokiBot information-stealing malware along with a second payload in the form of the Jigsaw Ransomware.
By using this malware combo, the attackers first steal saved user names and passwords stored in a variety of applications and then deploy the Jigsaw Ransomware to try and get a small ransom to sweeten the attack.
The exact emails sent as part of this campaign have not been found, but the attachments impersonate invoices, bank transfers, orders, and business inquiries.
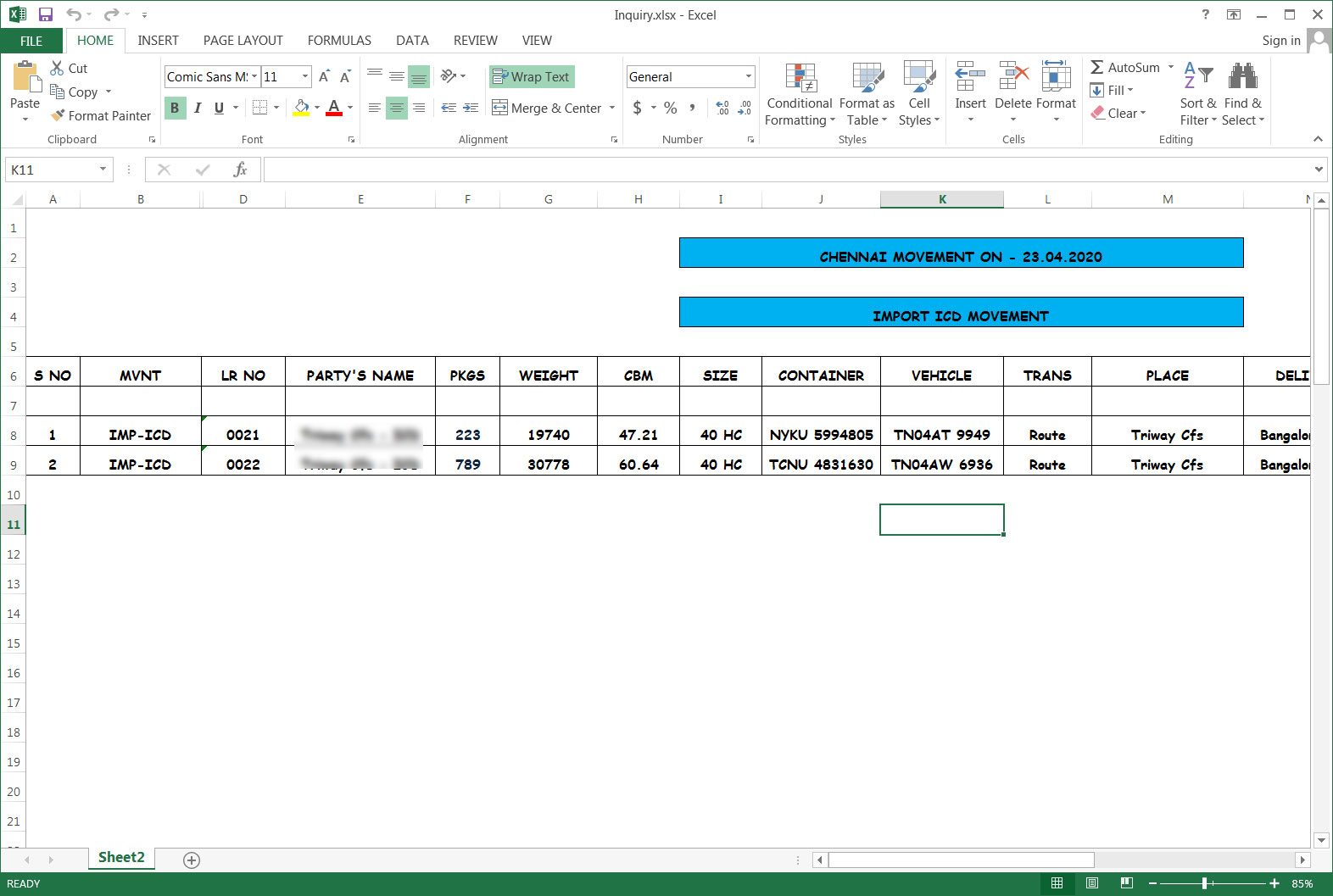
This campaign is using Excel attachments with names such as Swift.xlsx, orders.xlsx, Invoice For Payment.xlsx, Inquiry.xlsx.
Unlike many phishing attachments, the actors appear to be utilizing legitimate or carefully crafted spreadsheets that have been weaponized to seem believable, as shown below.