- Apr 25, 2013
- 5,355
Used to be that ransomware only looked at hard drive C:, and then any other mapped drives like D:, E:, F: etc., but now a newly discovered strain called CryptoFortress was discovered yesterday by security researcher Kafeine that has stolen the look & feel of TorrentLocker but is a whole new malicious strain. It would be a bit much to call this a new generation, but it certainly is a powerful new feature.
CryptoFortress includes the new and nasty feature of being able to encrypt files over network shares even if they are not mapped to a drive letter. Normally when ransomware encrypts your data it does so by retrieving a list of drive letters on a computer and then encrypting any data on them.
Therefore any network shares on the same network would be safe as long as they were not mapped to a drive letter. Unfortunately this all changes with CryptoFortress as this ransomware will also attempt to enumerate all open network Server Message Block (SMB) shares and encrypt any that are found.
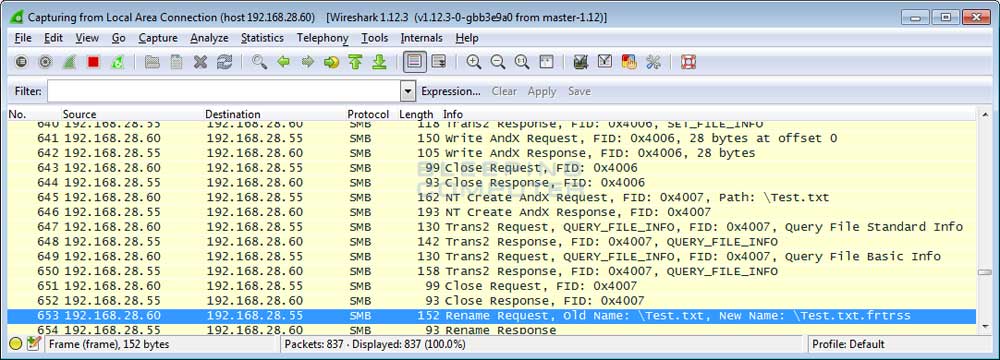
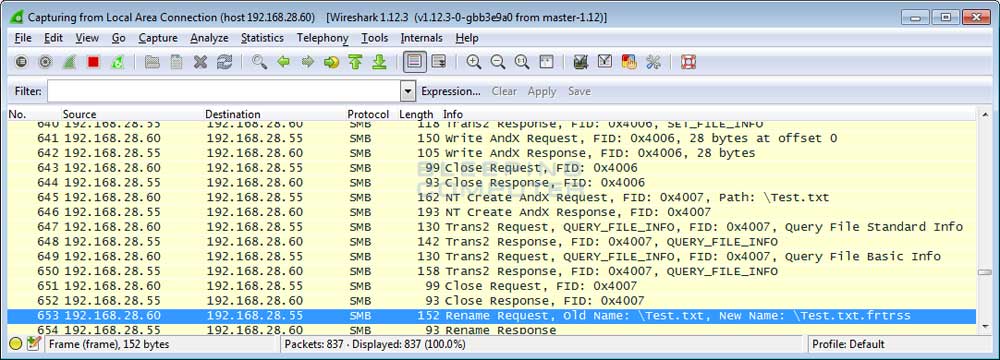
As you can see from the image below, CryptoFortress is successfully able to encrypt the file test.txt in an open share over SMB on a test network. This new ability changes the threat landscape for all server and network administrators and it is even more important than ever to properly secure your shared folders with strong permissions.
At the moment, it looks like the infection vector is Exploit Kits sitting on compromised websites, so that means patch workstations religiously, tighten up proxy and/or firewall rules, and possibly tell people to be careful out there (Maybe only Facebook?) if they surf the web on company workstations.
The full post with more detail is over at the BleepingComputer forum. More news to follow about this later I'm sure.
CryptoFortress includes the new and nasty feature of being able to encrypt files over network shares even if they are not mapped to a drive letter. Normally when ransomware encrypts your data it does so by retrieving a list of drive letters on a computer and then encrypting any data on them.
Therefore any network shares on the same network would be safe as long as they were not mapped to a drive letter. Unfortunately this all changes with CryptoFortress as this ransomware will also attempt to enumerate all open network Server Message Block (SMB) shares and encrypt any that are found.
As you can see from the image below, CryptoFortress is successfully able to encrypt the file test.txt in an open share over SMB on a test network. This new ability changes the threat landscape for all server and network administrators and it is even more important than ever to properly secure your shared folders with strong permissions.
At the moment, it looks like the infection vector is Exploit Kits sitting on compromised websites, so that means patch workstations religiously, tighten up proxy and/or firewall rules, and possibly tell people to be careful out there (Maybe only Facebook?) if they surf the web on company workstations.
The full post with more detail is over at the BleepingComputer forum. More news to follow about this later I'm sure.
