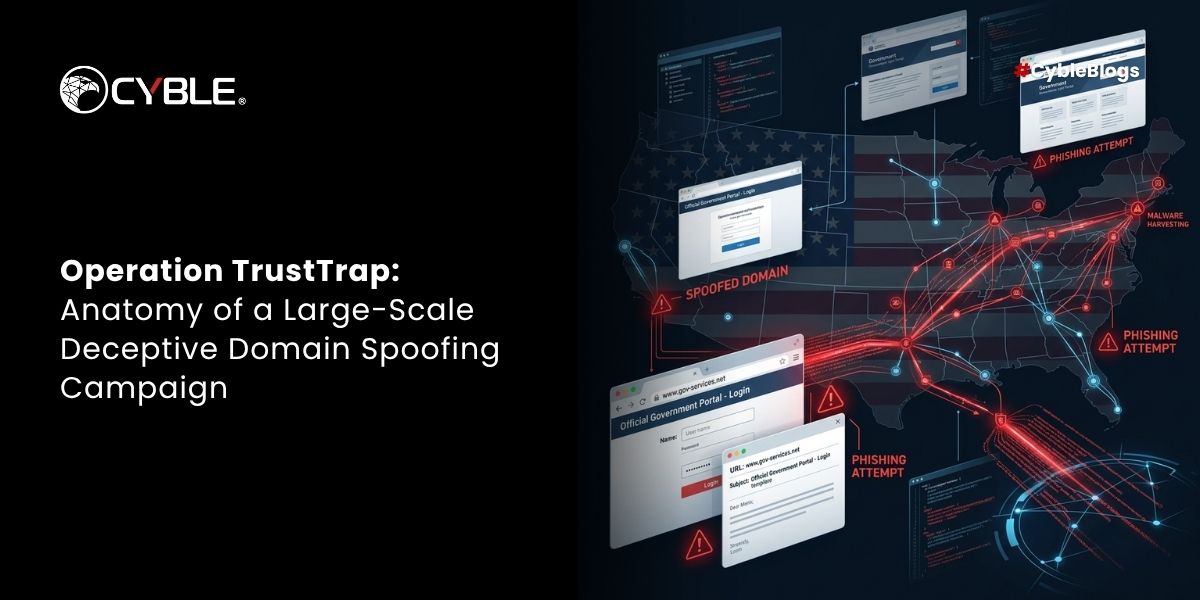
Operation TrustTrap: 16,800 malicious domains embed .gov tokens in subdomains to spoof US

state agencies, with APT36

cluster targeting India

. Campaign exploits cognitive trust rather than technical vulnerabilities.
CRIL uncovered 16,800+ spoofed domains by analyzing URL trust abuse, cloud infra clustering, and human‑centric deception in Operation TrustTrap

cyble.com
Key findings:
• Domains use subdomain injection (wa.gov-[id].bond) to bypass detection while appearing legitimate to users
• 70% registered via
GNAME | Buy Domain Names, Websites, Hosting, Cloud Products, hosted on Tencent/Alibaba Cloud

APAC infrastructure
• Targets DMV, toll systems across all US states plus India

, Vietnam

, UK

extensions
• APT36-linked cluster uses nia[.]gov[.]in[.]in3ymonaq[.]casa pattern for Indian government spoofing
• Active campaigns show double query string (?var1=xxxxx?var2=xxxxx) for victim tracking
Detection gaps:
• 62% had minimal VirusTotal detections due to structural vs string-based evasion
• Rapid 2-week operational windows before domain abandonment
• Path structures mirror real agencies: /dmv, /mvd, /dol, /dot for targeted impersonation
state agencies, with APT36
cluster targeting India
. Campaign exploits cognitive trust rather than technical vulnerabilities.
cyble.com
APAC infrastructure
, Vietnam
, UK
extensions
