silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,176
Newsletter sign-up forms from the websites of international companies have been used by malicious actors to camouflage phishing e-mails as official newsletter subscription messages.
This innovative new approach to run a phishing campaign observed by Doctor Web's researchers also has the advantage of circumventing the spam filters built into email servers and clients, besides tricking the receivers into thinking they're receiving official newsletter subscription messages.
Email-based phishing is used by bad actors to trick their targets into going to websites designed to collect various confidential information, downloading attachments containing malware, or clicking links redirecting to malware-laden attachments.
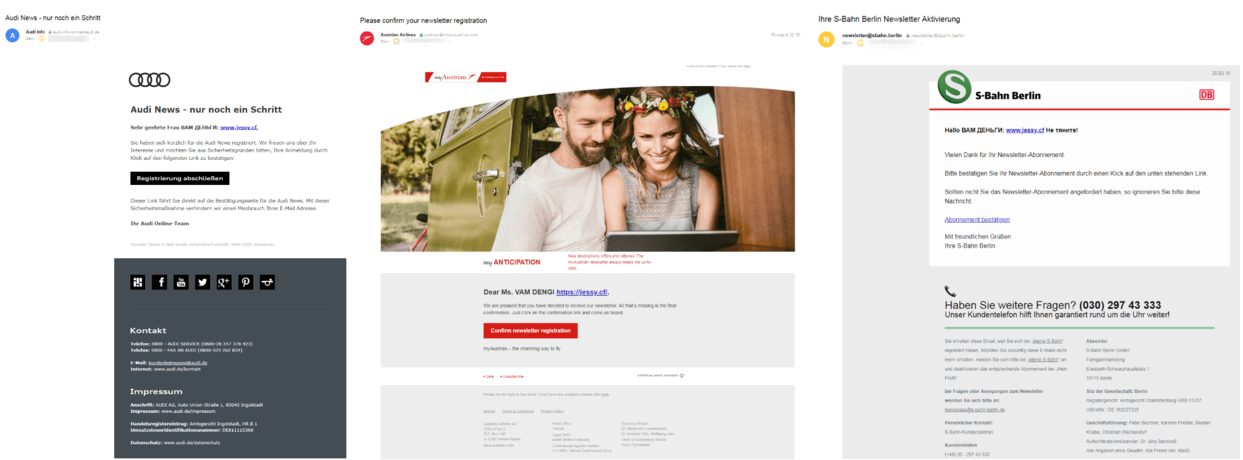
Example phishing emails
As detailed by the Dr.Web report the crooks behind this novel phishing campaign are sending emails that come from official addresses from companies with a worldwide presence such as Audi, Austrian Airlines, and S-Bahn Berlin, with a 'money for you' header in Russian.
"At the beginning of the email, a link leads users to the hacked page of a dating website. Then due to malicious code embedded into the website’s stub page users are redirected through several other websites to a phishing one," says Dr.Web.
