silversurfer
Super Moderator
Thread author
Verified
Top Poster
Staff Member
Malware Hunter
Forum Veteran
- Aug 17, 2014
- 13,090
- 125,689
- 8,399
A newly identified Android trojan can steal user information and provide attackers with the ability to take control of infected devices, threat detection company ThreatFabric reports.
Dubbed Brokewell, the trojan includes all the capabilities of mobile banking malware, while also providing attackers with remote access to devices.
Brokewell is being distributed via fake application updates, such as newer Chrome browser iterations and updates for an Austrian digital authentication application.
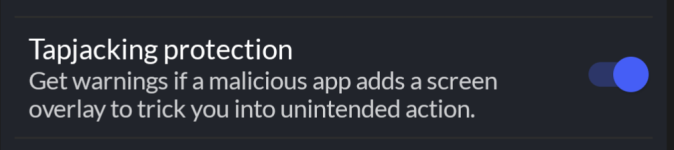
To harvest the victim’s credentials, the malware overlays fake windows over the targeted mobile applications. Furthermore, it can steal browser cookies by launching its own WebView, loading the legitimate site, and dumping session cookies after the user completes the login process.
Additionally, ThreatFabric discovered that Brokewell has an accessibility logging capability, which allows it to capture device events such as touches, swipes, text input, opened applications, and information being displayed on the screen.