RoboMan
Level 38
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
High Reputation
Forum Veteran
One common misconception about security usually is that "more is always better"… Not only it's not true, but in reality, stronger protection usually comes at a cost, and that cost is often privacy.
Modern security solutions rely heavily on cloud intelligence, telemetry, behavioral monitoring, and even AI-driven analysis. This means that, in many cases, your system is constantly sharing data: files, metadata, browsing activity, and sometimes even unknown samples uploaded for analysis.
So here’s the question:
Where do you personally draw the line between privacy and security?
Some points to consider:
Some users prefer maximum lockdown with minimal data sharing. Others are fine with extensive cloud integration if it means better real-time protection.
So… where do you stand?
Modern security solutions rely heavily on cloud intelligence, telemetry, behavioral monitoring, and even AI-driven analysis. This means that, in many cases, your system is constantly sharing data: files, metadata, browsing activity, and sometimes even unknown samples uploaded for analysis.
So here’s the question:
Where do you personally draw the line between privacy and security?
Some points to consider:
- Are you comfortable with your antivirus uploading suspicious files to the cloud automatically?
- Do you trust cloud-based protection systems more than offline, signature-based approaches?
- Would you sacrifice some privacy if it meant significantly better protection against zero-day threats?
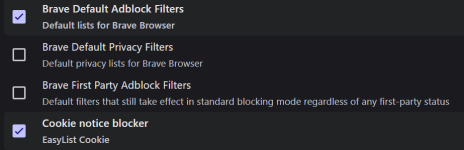
- Do you disable certain features (like web protection or telemetry) to maintain more control over your data?
- How much do you trust big security vendors with your information?
Some users prefer maximum lockdown with minimal data sharing. Others are fine with extensive cloud integration if it means better real-time protection.
So… where do you stand?