(heads up to @geminis3, @harlan4096, @SeriousHoax )
DISCLAIMER: This is a conceptual proof of concept, and is meant to test your behavior blocker's degree of whitelisting when a trusted binary is abused for evil purposes. This does not translate to whether or not your AV will detect real ransomware, which often has many other red flags. Do not place anything in My Documents\test\ that is valuable.
This is a follow-up to the "TrojanZipperPOC". Similar to @geminis3 's Ransominator, it abused the fact that 7Zip was trusted and whitelisted by many behavior blockers and therefore its actions were ignored.
But 7zip is kind of boring -- it can only manipulate files and is not a full blown programming language. That got me thinking: Can you get away with an entire Python runtime? It turns out that the official distribution of Python's "python.exe" is both digitally signed as well as marked as trusted by many cloud services -- Norton Insight, KSN, Emsisoft, etc.
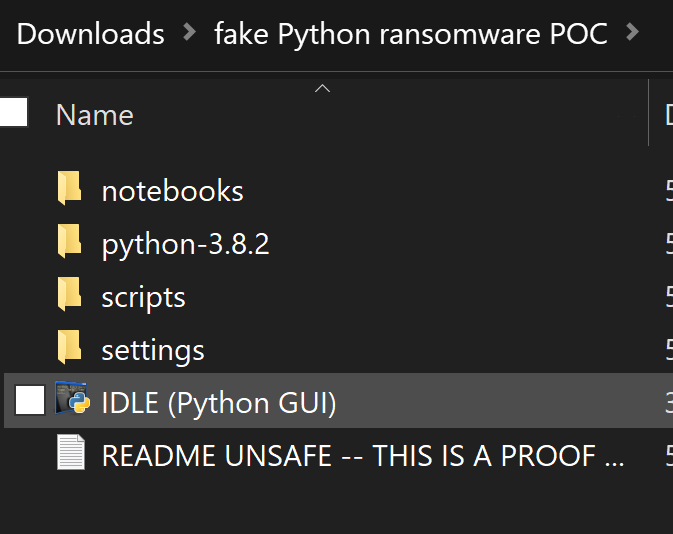
This new exploit, "pyrate" as I call it, bundles a copy of Python 3.8 (official Windows zip distribution), a "pyrate.py" ransom core, and an "aes.py" pure Python implementation of AES. It, like my other samples, ONLY encrypts "My Documents\test\", so it is safe to execute on your host machine (but please don't take my word for it). There are two ways to run it:
For my testing results, I will separate the results between starting the exploit as the EXE vs starting it via "start.bat". If you are a tester, feel free to PM me for the exploit POC to test on your own!
Other Commentary: I think this is an especially dangerous exploit. This is a full blown Python runtime with wintypes. It has the complete ability to call arbitrary Win32 APIs, snoop around network shares, etc etc etc. It goes to show that a major weakness of AMSI for script defense is that it requires your scripting engine to be AMSI-aware. This Python binary is not compiled with AMSI.
The "bonus" attack of sticking a ransomware script into the startup file for the Python IDE is basically a new form of macro viruses. The behavior blocker logic of "User started Python IDE, Python IDE is trusted and sometimes saves to My Documents, therefore, ignore what the Python IDE is doing" is fundamentally flawed when an application is a full blown scripting environment. It doesn't matter if an executable is common, signed, and generally good reputation if that executable is a scripting language interpreter!
DISCLAIMER: This is a conceptual proof of concept, and is meant to test your behavior blocker's degree of whitelisting when a trusted binary is abused for evil purposes. This does not translate to whether or not your AV will detect real ransomware, which often has many other red flags. Do not place anything in My Documents\test\ that is valuable.
This is a follow-up to the "TrojanZipperPOC". Similar to @geminis3 's Ransominator, it abused the fact that 7Zip was trusted and whitelisted by many behavior blockers and therefore its actions were ignored.
But 7zip is kind of boring -- it can only manipulate files and is not a full blown programming language. That got me thinking: Can you get away with an entire Python runtime? It turns out that the official distribution of Python's "python.exe" is both digitally signed as well as marked as trusted by many cloud services -- Norton Insight, KSN, Emsisoft, etc.
This new exploit, "pyrate" as I call it, bundles a copy of Python 3.8 (official Windows zip distribution), a "pyrate.py" ransom core, and an "aes.py" pure Python implementation of AES. It, like my other samples, ONLY encrypts "My Documents\test\", so it is safe to execute on your host machine (but please don't take my word for it). There are two ways to run it:
- 7zip SFX: The default package is a 7zip self extracting EXE that automatically executes pyrate.py after unzipping. This in theory should trigger more behavior blockers because it starts out as an untrusted, unsigned EXE.
- "start.bat": You can use 7zip to extract the .exe and then directly launch "Start.bat". As we've seen many times, AVs currently are pretty bad at understanding that batch files started by the user are untrustable.
- "bonus" backdoored IDE: There is a much more dangerous version of this exploit possible. When the Python interpreter starts, it actually executes many .py/.pyc scripts that are part of the Python built-in libraries. Even if you use a host hardening system that blocks batch files, you can still booby trap the fully signed Python.exe executable and cause it to run the ransomware on launch. This is the "bonus" test column:
For my testing results, I will separate the results between starting the exploit as the EXE vs starting it via "start.bat". If you are a tester, feel free to PM me for the exploit POC to test on your own!
| Software | Result for click on EXE | Result for Start.bat | Result for bonus "IDLE Python IDE backdoor" | Tested by | Comments |
| Kaspersky Total Security 2020 (default settings) | PROTECTED. KSW triggered after 3rd encrypted file, deleted the Pyrate.EXE file, correctly identified that as the cause. Rollback succeeded and restored encrypted files. | ENCRYPTED. No detection at all. | ENCRYPTED | @MacDefender | Kudos to KSW -- it is one of the only BB's I've tested that looks at full execution trees and understands that Pyrate.exe started Python.exe and therefore Python.exe is not trustworthy. |
| F-Secure FS Protection 17.8 Beta Default Ransomware Protection covering My Documents and other default locations. | ENCRYPTED | ENCRYPTED | ENCRYPTED | @MacDefender | |
| Emsisoft AM Default Settings | ENCRYPTED | ENCRYPTED | ENCRYPTED | @MacDefender | In the "Application Rules" view, the exploit is labeled as "Python.exe" and shows up as trusted and Not Monitored |
| Norton 360 with Data Protector, default settings | PROTECTED. Data Protector blocked and identified the offending EXE correctly | ENCRYPTED | ENCRYPTED | @MacDefender | |
| WD with ConfigureDefender, no CFA | PROTECTED (rule "Use advanced protection against ransomware" ) | ENCRYPTED | ENCRYPTED | @SeriousHoax | |
| WD with CFA | PROTECTED | PROTECTED | PROTECTED | @SeriousHoax | CFA alerted to Python attempting to access My Documents |
| ESET (without HIPS protected folder simulation) | ENCRYPTED | ENCRYPTED | ENCRYPTED | @SeriousHoax, @MacDefender confirmed the third column |
Other Commentary: I think this is an especially dangerous exploit. This is a full blown Python runtime with wintypes. It has the complete ability to call arbitrary Win32 APIs, snoop around network shares, etc etc etc. It goes to show that a major weakness of AMSI for script defense is that it requires your scripting engine to be AMSI-aware. This Python binary is not compiled with AMSI.
The "bonus" attack of sticking a ransomware script into the startup file for the Python IDE is basically a new form of macro viruses. The behavior blocker logic of "User started Python IDE, Python IDE is trusted and sometimes saves to My Documents, therefore, ignore what the Python IDE is doing" is fundamentally flawed when an application is a full blown scripting environment. It doesn't matter if an executable is common, signed, and generally good reputation if that executable is a scripting language interpreter!
Last edited:



