- Jul 27, 2015
- 5,458

Quote : " A vulnerability could allow attackers to track in real-time the movements of all 50 million Waze users.
Waze is a "community-based traffic and navigation app" available for Android, iPhone, and Windows Phone. It enables drivers to share traffic and road information with one another, including alerts on police stops, accidents, constructions, hazards, and traffic jams. Waze then analyzes that data for local users and plots out an optimal path for their daily commutes that will consume the least amount of time and gas. Sounds nifty, right? It is... but only to an extent.
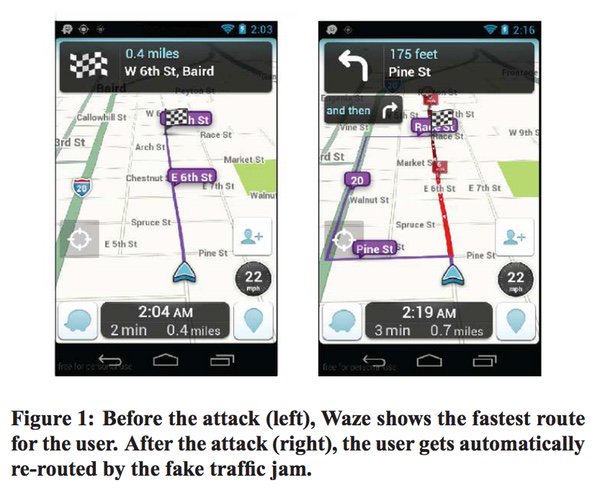
Researchers at the University of California-Santa Barbara have discovered a vulnerability that would effectively allow a hacker to track the movements of any of Waze's 50 million users. Specifically, they found they could set up an HTTPS proxy man-in-the-middle (MitM) to intercept all communication between a user's phone and Waze's servers, which talk with each Waze client via SSL. With that setup in place, the researchers found they could reverse engineer the app's communication protocols and use that knowledge to issue commands directly to Waze's servers. Here's where it gets interesting. The team discovered a way to populate the system with thousands of "ghost cars" - which are not the same as Uber's "phantom riders" - to create fake traffic jams that would reroute users unnecessarily or to monitor their every move. "