F
ForgottenSeer 89360
Thread author
Hi all,
This is a short guide on how to deploy McAfee Endpoint Security 10.7
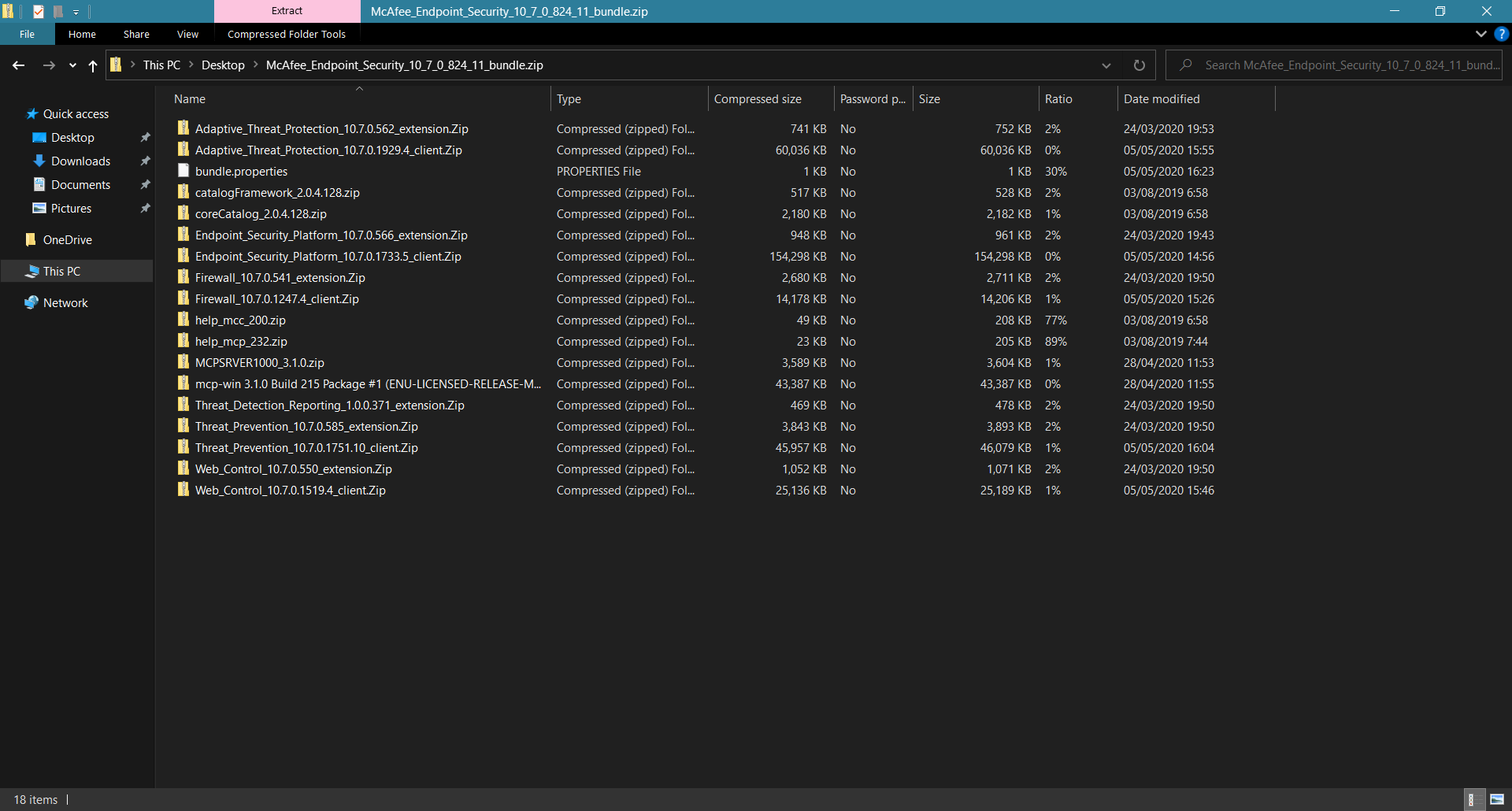
Once the archive is downloaded, just open it.
You'll see the following screen that looks like a hot mess, but it is in fact very VERY easy to get started.
McAfee Endpoint Security consists of 5 components:
Immediately after opening the archive it would be great if you get rid of components you don't need.
These are the MVISION & ePO extensions. MVISION is a paid product and we are looking to use McAfee Endpoint Security as a standalone product.
That's why we can simply type extensions into the windows search bar. We can then use CTRL+A to select all the archives listed bellow and SHIFT+Delete to remove them.
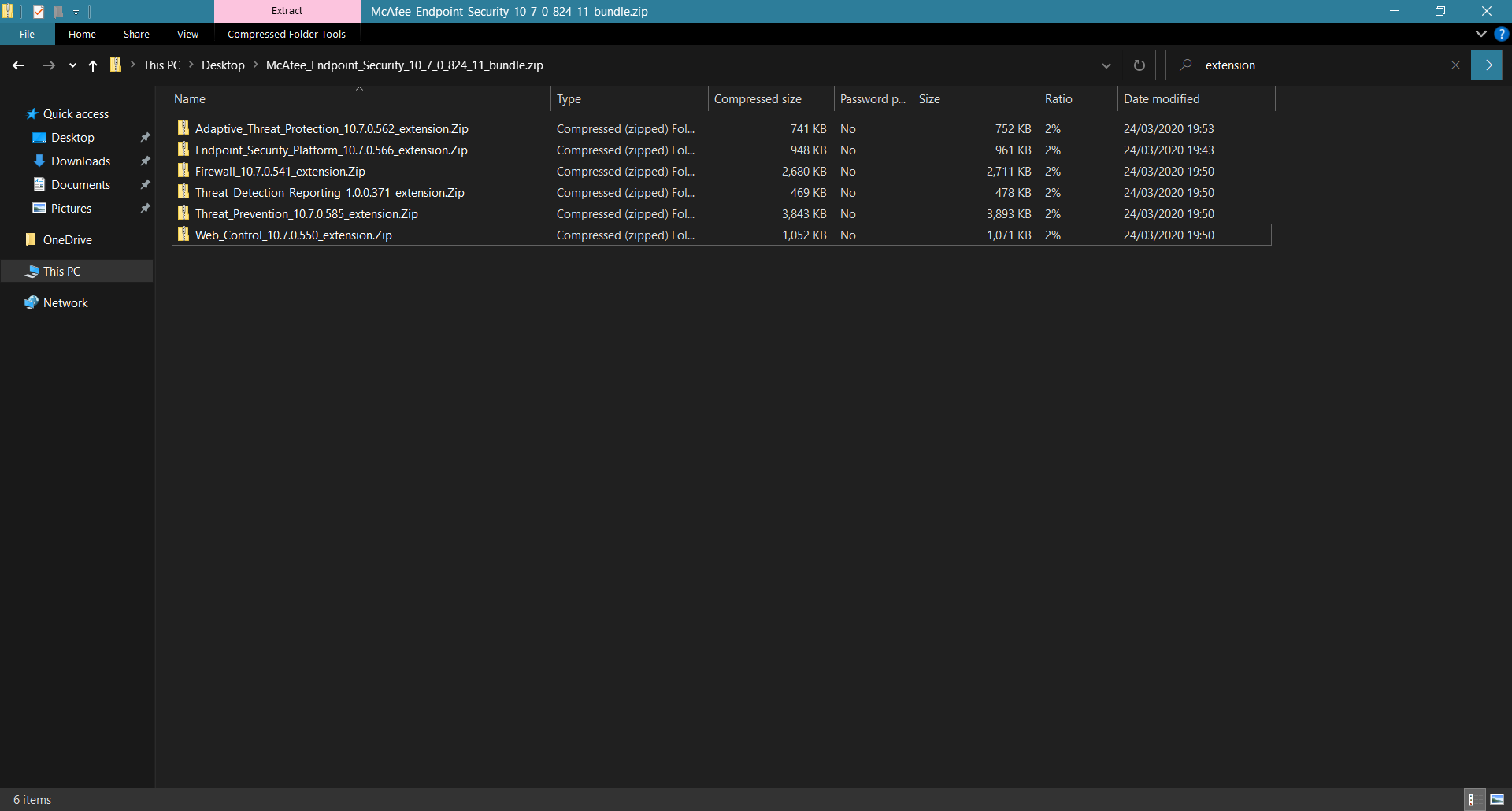
It's also safe to remove the bundle.properties file, the help_mcc and help_mcp, MCPSRVER1000_3.1.0.zip, mcp-win 3.1.0 Build 215 Package #1 (ENU-LICENSED-RELEASE-MAIN).Zip, catalogFramework_2.0.4.128.zip and coreCatalog_2.0.4.128.zip.
We won't need any of those.
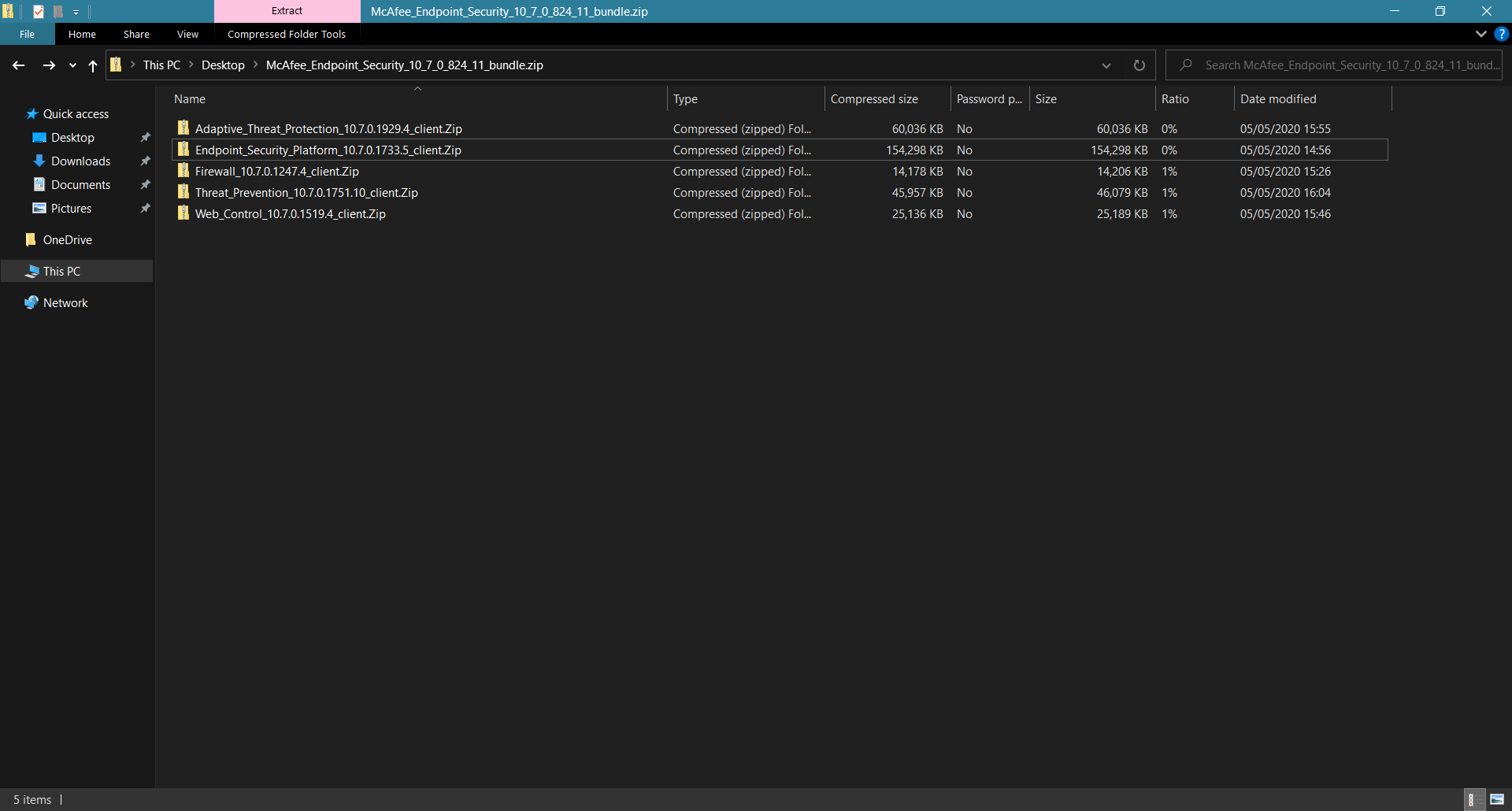
That way we are left with a screen looking like this.
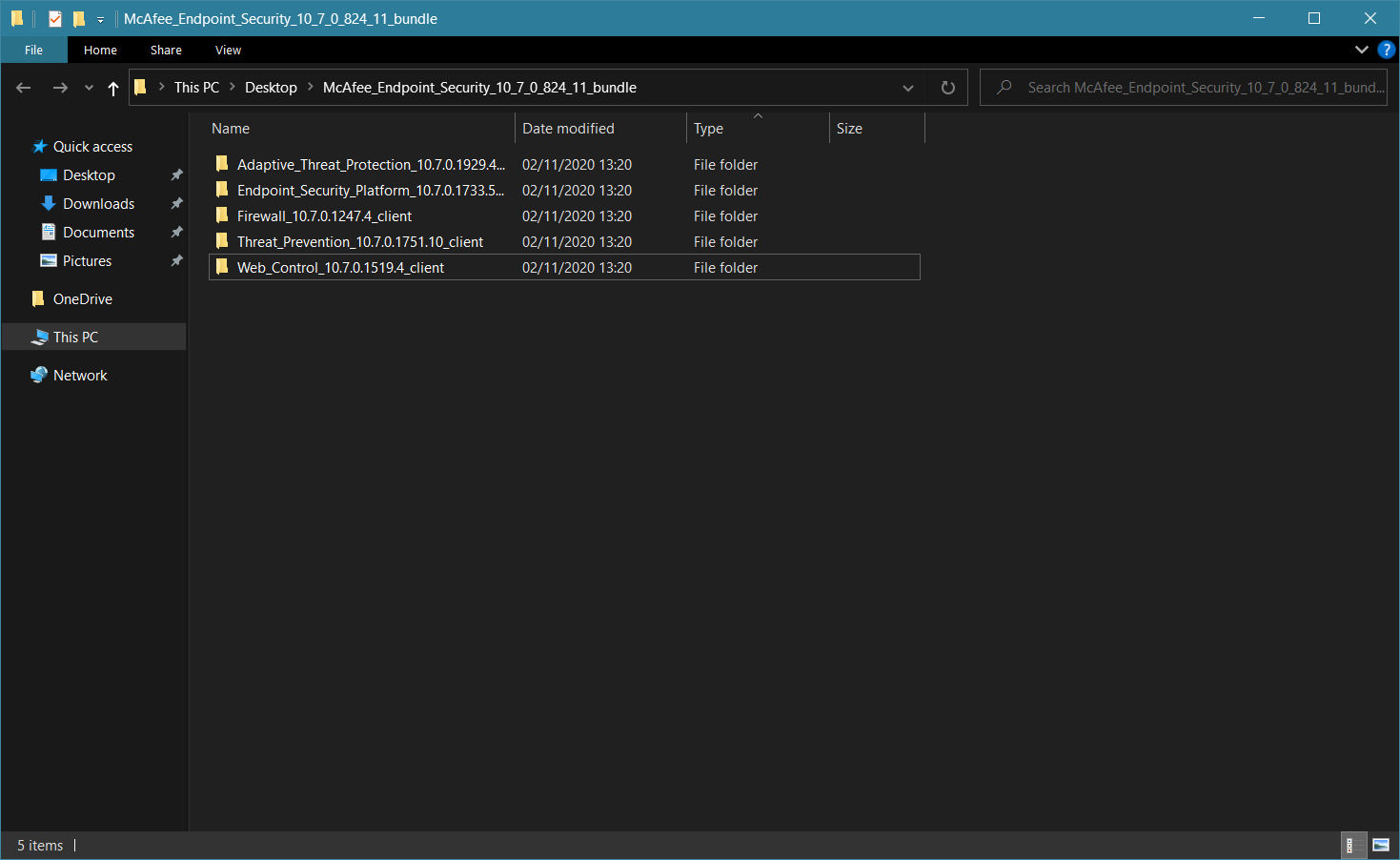
Now it's time to extract the archive and unpack all components to a new folder. After we have successfully unpacked everything to a new folder we have a screen looking like this:
It's time to start installing. Bear in mind none of the installer brings up a UI.
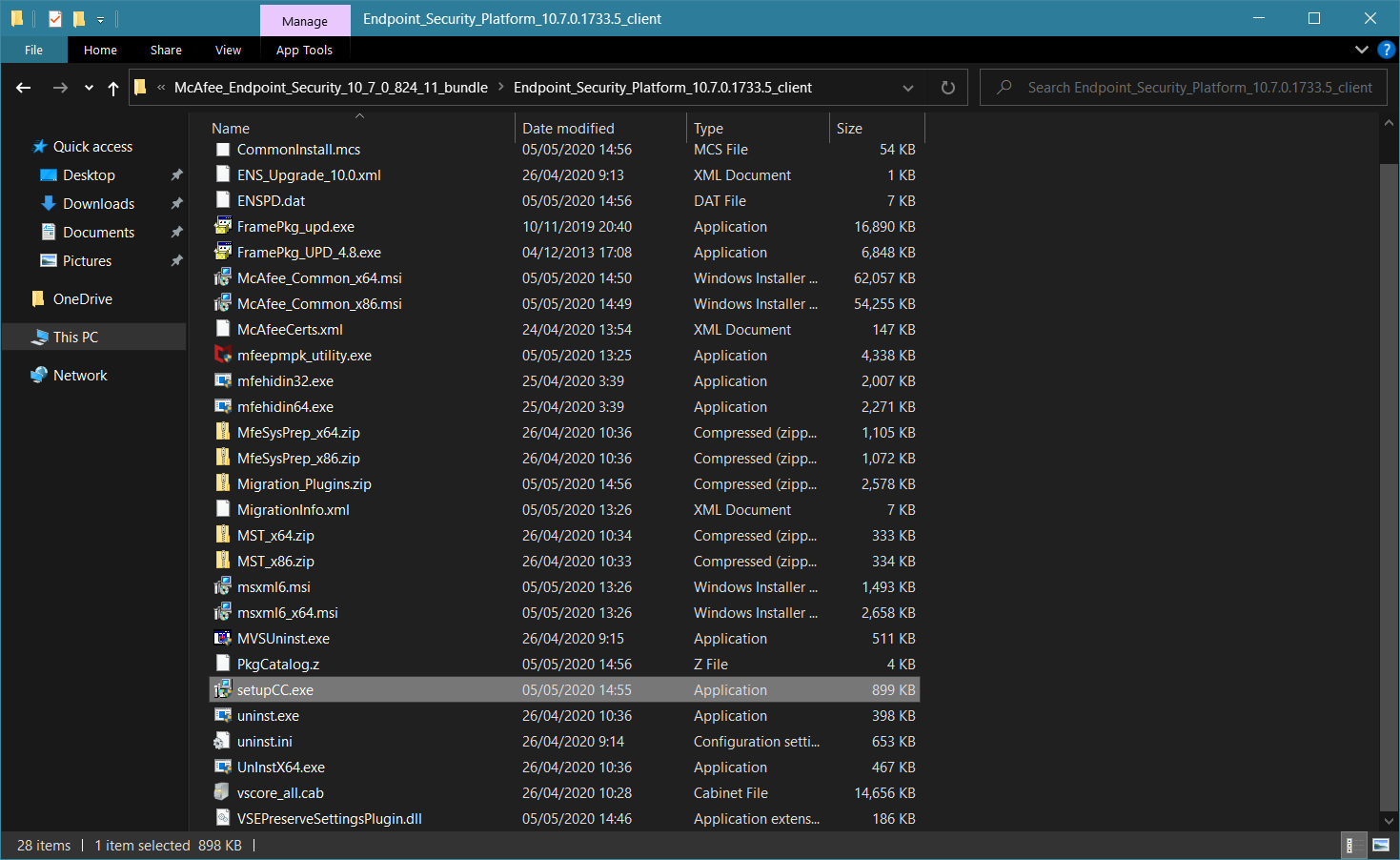
We have to begin with the Endpoint Security Platform. Navigate to Endpoint_Security_Platform_10.7.0.1733.5_client and launch setupCC.exe.
In less than a minute, the platform will be ready.
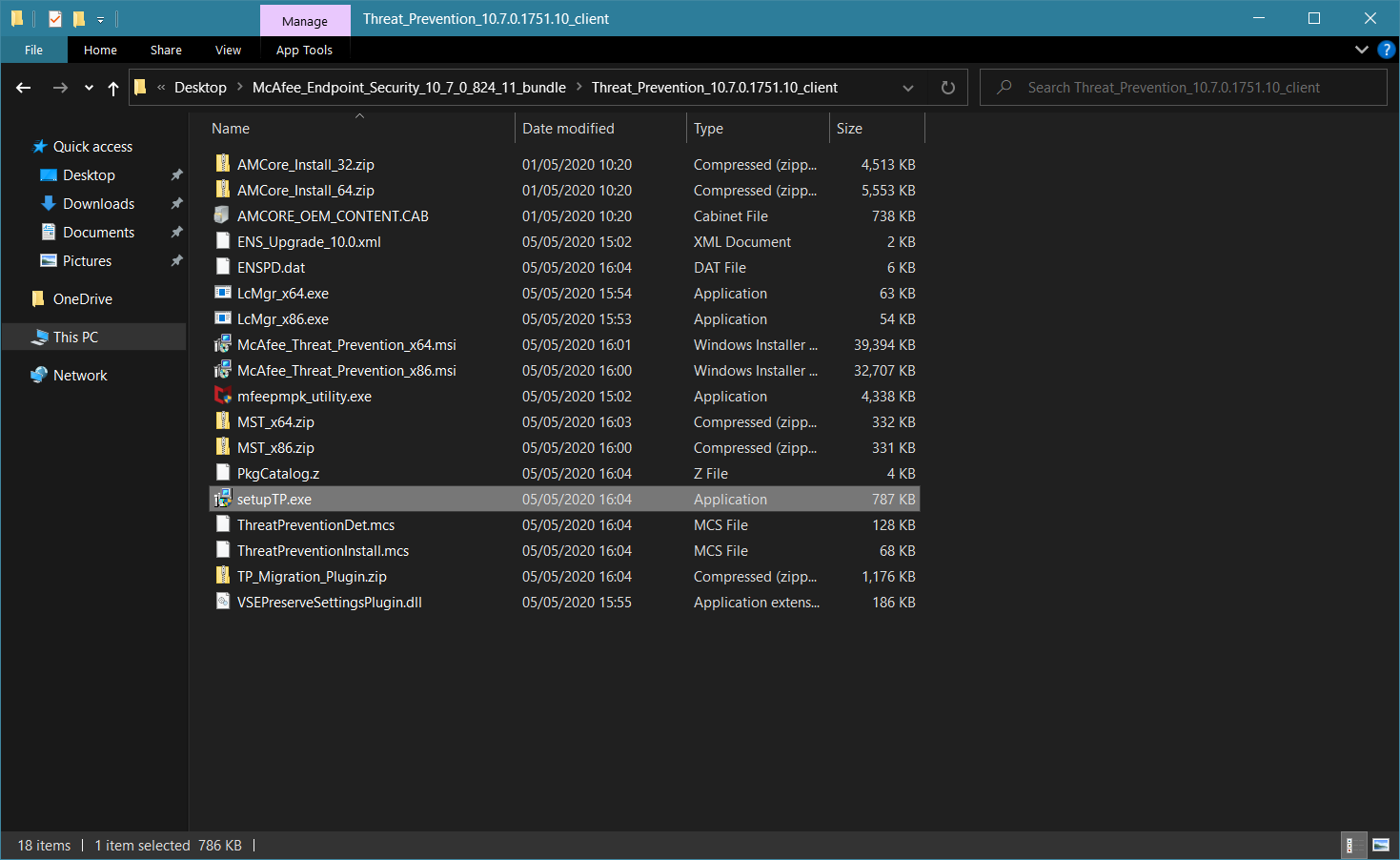
Now it's time for the standard antivirus component, which is called Threat Prevention. This component will install antivirus with minimal definitions set, so it's recommended that you launch an update right after the installation.
Navigate to Threat_Prevention_10.7.0.1751.10_client and launch setupTP.exe.
In less than a minute, the antivirus will be installed as well.
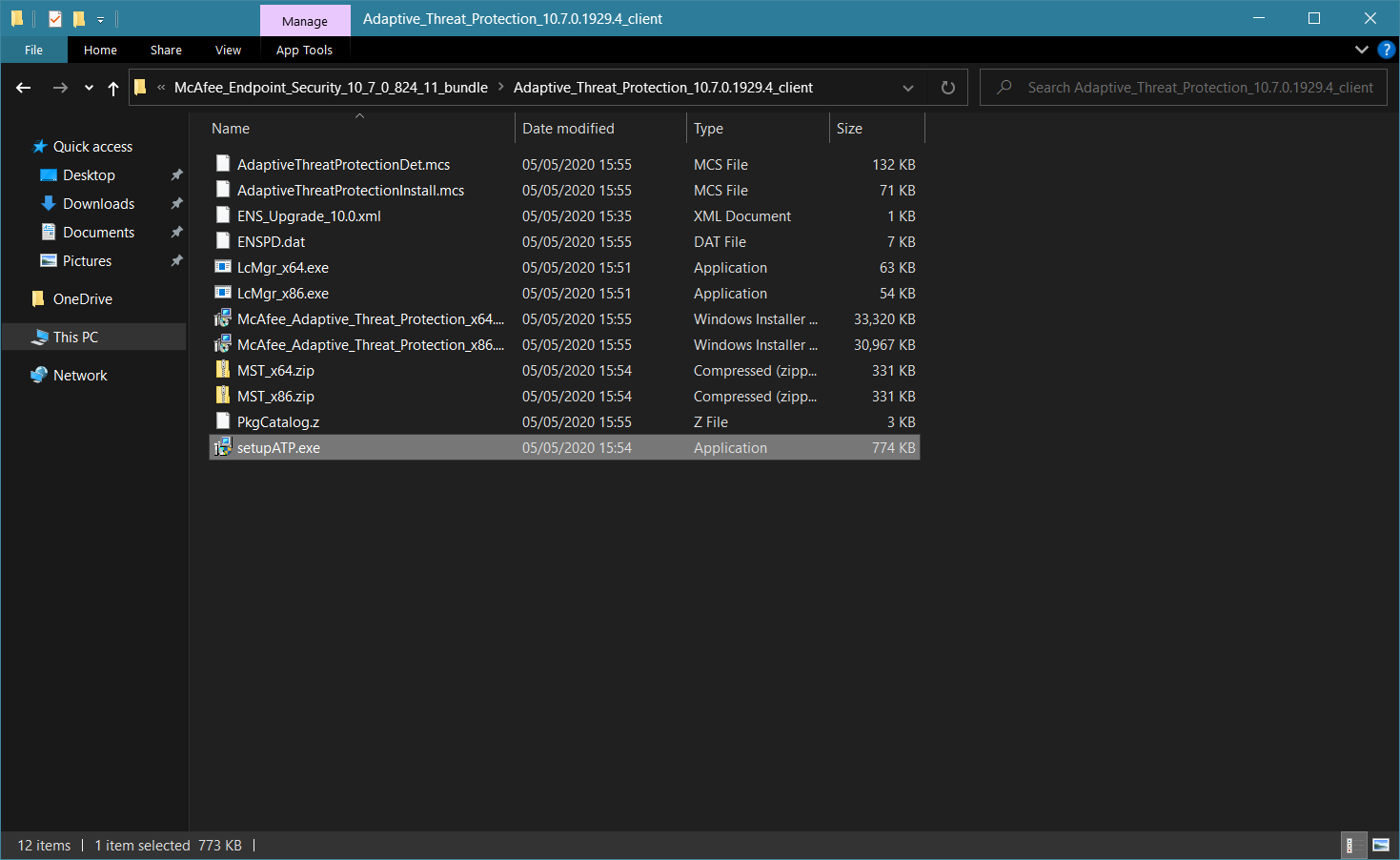
Now it's time to install Adaptive Threat Protection.
Navigate to Adaptive_Threat_Protection_10.7.0.1929.4_client ands launch setupATP.exe.
In less than a minute this component will be installed as well. There is a McAfee tray icon (M-Shield icon) in the system tray. You can launch the main UI and all installed components should already be listed there.
Now we can install Firewall and Web Control by navigating to their respective folders and launching setupFW.exe and setupWC.exe.
The product is now deployed in full and the main UI should be looking like this:

This guide shows you how to install all components, but you can choose to install for example only Firewall, to complement solutions like Avira, F-Secure or TrendMicro that don't have firewall built-in or you can install just Threat Prevention + Adaptive Threat Protection if you already have a firewall and URL filtering extension. You can't install Adaptive Threat Protection on its own however.
It would make no sense to install Web Control as a standalone component, as McAfee Web Advisor as well as various other web blockers are available as a browser extension, but you can also do that if you feel like it.
I advise you to read McAfee documentation as there is a lot going on in the product settings.
This can be found here:
You can also have a look at my configuration or view additional resources here:

 malwaretips.com
malwaretips.com
Thanks for reading.
This is a short guide on how to deploy McAfee Endpoint Security 10.7
Once the archive is downloaded, just open it.
You'll see the following screen that looks like a hot mess, but it is in fact very VERY easy to get started.
McAfee Endpoint Security consists of 5 components:
- Adaptive Threat Protection (extensive behavioural blocking working against 0-days).
- Firewall (stops risky connections, such as intrusions or communication to C&C servers).
- Threat Prevention (standard antivirus protection against known and not so known threats).
- Web Control (protection against malicious, phishing and unverified websites).
- Endpoint Security Platform (provides the UI and link between all components).
Immediately after opening the archive it would be great if you get rid of components you don't need.
These are the MVISION & ePO extensions. MVISION is a paid product and we are looking to use McAfee Endpoint Security as a standalone product.
That's why we can simply type extensions into the windows search bar. We can then use CTRL+A to select all the archives listed bellow and SHIFT+Delete to remove them.
It's also safe to remove the bundle.properties file, the help_mcc and help_mcp, MCPSRVER1000_3.1.0.zip, mcp-win 3.1.0 Build 215 Package #1 (ENU-LICENSED-RELEASE-MAIN).Zip, catalogFramework_2.0.4.128.zip and coreCatalog_2.0.4.128.zip.
We won't need any of those.
That way we are left with a screen looking like this.
Now it's time to extract the archive and unpack all components to a new folder. After we have successfully unpacked everything to a new folder we have a screen looking like this:
It's time to start installing. Bear in mind none of the installer brings up a UI.
We have to begin with the Endpoint Security Platform. Navigate to Endpoint_Security_Platform_10.7.0.1733.5_client and launch setupCC.exe.
In less than a minute, the platform will be ready.
Now it's time for the standard antivirus component, which is called Threat Prevention. This component will install antivirus with minimal definitions set, so it's recommended that you launch an update right after the installation.
Navigate to Threat_Prevention_10.7.0.1751.10_client and launch setupTP.exe.
In less than a minute, the antivirus will be installed as well.
Now it's time to install Adaptive Threat Protection.
Navigate to Adaptive_Threat_Protection_10.7.0.1929.4_client ands launch setupATP.exe.
In less than a minute this component will be installed as well. There is a McAfee tray icon (M-Shield icon) in the system tray. You can launch the main UI and all installed components should already be listed there.
Now we can install Firewall and Web Control by navigating to their respective folders and launching setupFW.exe and setupWC.exe.
The product is now deployed in full and the main UI should be looking like this:
This guide shows you how to install all components, but you can choose to install for example only Firewall, to complement solutions like Avira, F-Secure or TrendMicro that don't have firewall built-in or you can install just Threat Prevention + Adaptive Threat Protection if you already have a firewall and URL filtering extension. You can't install Adaptive Threat Protection on its own however.
It would make no sense to install Web Control as a standalone component, as McAfee Web Advisor as well as various other web blockers are available as a browser extension, but you can also do that if you feel like it.
I advise you to read McAfee documentation as there is a lot going on in the product settings.
This can be found here:
Overview of Endpoint Security - McAfee Endpoint Security 10.7.x
McAfee Endpoint Security protects servers, computer systems, laptops, and tablets against known and unknown threats. These threats include malware, suspicious communications, unsafe websites, and downloaded files.
docs.mcafee.com
You can also have a look at my configuration or view additional resources here:

How to configure McAfee Endpoint Security 10.7 for decent protection?
Hi everyone, This is a short guide on how to configure McAfee Endpoint Security for maximum security. [/SPOILER] [/SPOILER]
 malwaretips.com
malwaretips.com
Thanks for reading.
Last edited by a moderator: