I'm confident the first two points I made are correct but I've emailed Comodo about them for confirmation purposes. I'll post the response when they get back to me.1. I don't think so, everything in the TVL or trusted by the user can run freely
2. If the file is on TVL or trusted by the user, it won't be checked on cloud
3. Only if you set Viruscope to check files outside the sandbox too
Edit: Trusted Vendors, PC Firewall, Internet Protection | Internet Security Help
If the vendor is on the 'Trusted Software Vendor List 'AND the user has enabled 'Trust Applications signed by Trusted Vendors' in the 'File Rating Settings' panel, THEN the application will be trusted and allowed to run.
As for Viruscope, it depends what product you use. Both Comodo Internet Security and Comodo Firewall have Viruscope monitoring applications outside the sandbox by default. If you use Comodo Cloud Antivirus then you have to change a setting to allow it to monitor outside the sandbox.
Edit: Looked around and found one of Cruelsister's previous posts that states revoked certificates don't bypass the TVL:
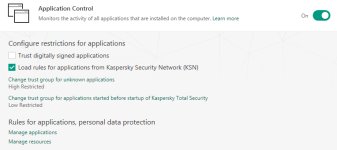
Compare Protection - Trusted Application Module vs Application Control vs CIS
I'll wait for Comodo's response for definitive confirmation though.
Last edited: