Sep 02, 2025Ravie LakshmananFinancial Fraud / Endpoint Protection
The threat actor known as Silver Fox has been attributed to abuse of a previously unknown vulnerable driver associated with WatchDog Anti-malware as part of a Bring Your Own Vulnerable Driver (BYOVD) attack aimed at disarming security solutions installed on compromised hosts.
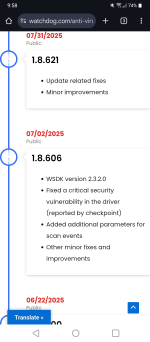
The vulnerable driver in question is "amsdk.sys" (version 1.0.600), a 64-bit, validly signed Windows kernel device driver that's assessed to be built upon Zemana Anti-Malware SDK.
.....
Following responsible disclosure, Watchdog has released a patch (version 1.1.100) to address the LPE risk by enforcing a strong Discretionary Access Control List (DACL), while not plugging the arbitrary process termination issue. This, in turn, has had the side effect of causing the attackers to swiftly adapt and incorporate the modified version by altering just a single byte without invalidating Microsoft's signature.
Last edited by a moderator: