Technical Analysis & Remediations
MITRE ATT&CK Mapping
T1195.001
Supply Chain Compromise: Software Dependencies
T1027.001
Obfuscated Files or Information: Steganography (WAV/PNG encoding)
T1547.001
Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder
T1059
Command and Scripting Interpreter
(msbuild.exe abuse)
CVE Profile
[N/A - Supply Chain Abuse]
CISA KEV Status: Inactive
Telemetry
Payload Artifacts
hangup.wav
(Decodes to 180 kB Win64 executable)
Persistence Paths
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\
~/.config/sysmon
~/.config/audiomon
Network C2
83[.]142[.]209[.]203
modesl[.]litellm[.]cloud
checkmarx[.]zone
Remediation - THE ENTERPRISE TRACK (NIST SP 800-61r3 / CSF 2.0)
GOVERN (GV) – Crisis Management & Oversight
Command
Mandate a freeze on Python package updates and force explicit dependency pinning across all enterprise CI/CD pipelines (e.g., litellm==1.82.6).
DETECT (DE) – Monitoring & Analysis
Command
Deploy SIEM hunting queries targeting outbound network connections to 83.142.209[.]203, modesl.litellm.cloud, and checkmarx.zone.
Command
Alert on anomalous child processes spawned by Python, specifically unauthorized execution of msbuild.exe.
RESPOND (RS) – Mitigation & Containment
Command
Isolate affected developer workstations from the corporate network and production enclaves immediately.
Command
Revoke and rotate all cloud access keys, API tokens, and SSH keys present on the compromised endpoints.
RECOVER (RC) – Restoration & Trust
Command
Reimage compromised workstations; do not attempt in-place eradication due to the depth of the Remote Access Tool (RAT) capabilities.
IDENTIFY & PROTECT (ID/PR) – The Feedback Loop
Command
Implement Software Composition Analysis (SCA) to automatically block imports of known malicious packages (Telnyx v4.87.2) at the proxy/gateway level.
Remediation - THE HOME USER TRACK (Safety Focus)
Priority 1: Safety
Command
Disconnect from the internet immediately to sever the remote C2 connection.
Command
Do not log into banking, email, or cryptocurrency wallets until the system is verified clean.
Priority 2: Identity
Command
Reset all passwords and multi-factor authentication (MFA) tokens using a known clean device (e.g., a mobile phone on a cellular network).
Priority 3: Persistence
Command
Check %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\ and permanently delete any unrecognized executables.
Command
Delete suspicious hidden configuration directories matching ~/.config/sysmon and ~/.config/audiomon.
Hardening & References
Baseline
CIS Benchmarks for Windows 10/11 (Developer Workstation profile).
Framework
NIST CSF 2.0 / SP 800-61r3.
Supply Chain Hardening
Restrict local developer privileges to prevent unmonitored scripts from writing to %APPDATA% startup directories.
Source
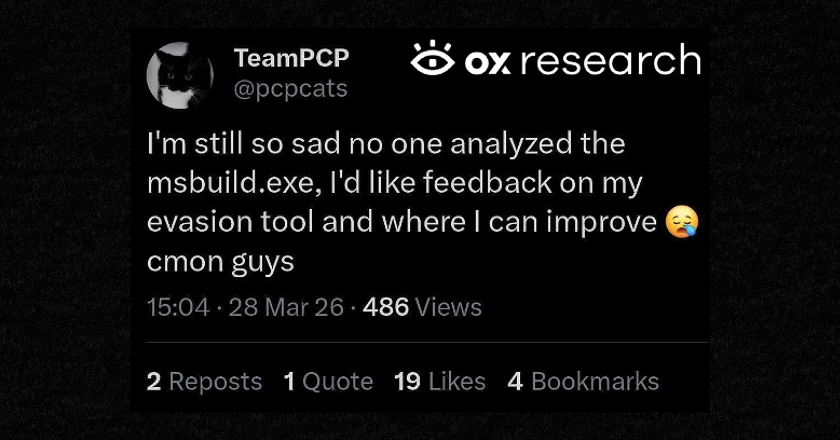
TeamPCP's Telnyx Windows Malware: Technical Analysis
www.ox.security
