I need recommendations (and further explanation) on which to choose:
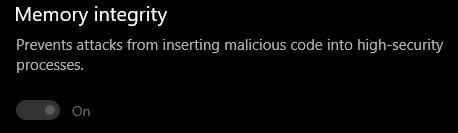
1.) Hypervisor-Protected Code Integrity (HVCI)/Memory Integrity VS Kaspersky with "better" System Watcher & Protected Browser/Safe Money additional functionality.
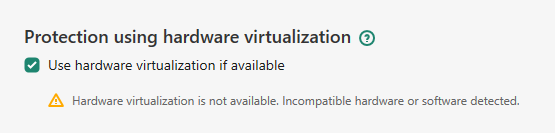
When HVCI (or any VBS) is enabled, Kaspersky protection using hardware virtualization becomes unavailable.
Back then I asked the Kaspersky community. According to Kaspersky Employee, other than Safe Money, virtualization is also used in System Watcher in certain scenarios (I'm not sure which).
Also, he said that "Kaspersky products definitely protect from the injection and execution of malicious or unverified code with the help of File Anti-Virus, System Watcher and Application Control." suggesting that Kaspersky could protect users from threat just like HVCI except it's not by isolated area of system memory but protecting it from malicious code injection.
With all of this information, it seems that both are good with their trade-off, but for me, HVCI is more important especially with isolated secure system memory areas and easy pick.
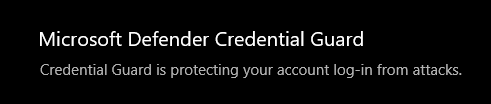
2.) Credential-Guard VS Various Kaspersky Functionalities
(At first, IIRC WD App Ctrl user mode policy set to off, and policy is enforced). Immediately after I managed to fix it, I suddenly got this warning message from Kaspersky (after I close it, there's no warning appears anywhere, not even in reports):

I'm using Windows 10 Pro 21H1 but it still generates this warning, most likely article above forget this version exists.
Which "Learn more" hyperlink leads to limitation details above, even worse for older Windows: limitations against file-encrypting malware and screen lockers (only these two), most likely if System Watcher is the last resort. AFAIK, limitations mean there's still functionality but will not be optimal, except it directly said that certain functionality won't work at all.
I think is both are important but the Kaspersky functionality trade-off is a bit too much variety compared to Credential Guard.
Still, no idea what three kinds of three browser protection mean, also what kind of unauthorized remote access is, RCE?
Any suggestions for my case (latest Windows)?
1.) Hypervisor-Protected Code Integrity (HVCI)/Memory Integrity VS Kaspersky with "better" System Watcher & Protected Browser/Safe Money additional functionality.
When HVCI (or any VBS) is enabled, Kaspersky protection using hardware virtualization becomes unavailable.
Back then I asked the Kaspersky community. According to Kaspersky Employee, other than Safe Money, virtualization is also used in System Watcher in certain scenarios (I'm not sure which).
Also, he said that "Kaspersky products definitely protect from the injection and execution of malicious or unverified code with the help of File Anti-Virus, System Watcher and Application Control." suggesting that Kaspersky could protect users from threat just like HVCI except it's not by isolated area of system memory but protecting it from malicious code injection.
With all of this information, it seems that both are good with their trade-off, but for me, HVCI is more important especially with isolated secure system memory areas and easy pick.
2.) Credential-Guard VS Various Kaspersky Functionalities
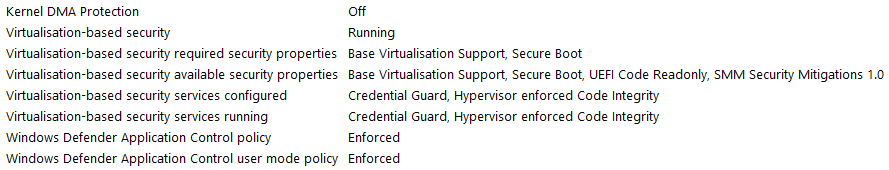
First managed to activate both HVCI and Credential Guard but I have to reinstall my android emulator because it needs to run with Hyper-V if Windows VBS is enabled but after that, I had trouble with credential guard (only HVCI enabled) and have to find ways to fix it. After I fixed it look like this:Kaspersky Total Security will have the following limitations on Windows 10 versions 1803, 1809, 1903, 2004:
- Clipboard protection.
- Browser protection against keyboard and mouse emulation software.
- Protection against unauthorized remote access.
- Browser protection: management through API, protection against attacks through browser windows, protection against message queue management.
- Detection of screen lockers when the UMCI mode is enabled.
(At first, IIRC WD App Ctrl user mode policy set to off, and policy is enforced). Immediately after I managed to fix it, I suddenly got this warning message from Kaspersky (after I close it, there's no warning appears anywhere, not even in reports):
I'm using Windows 10 Pro 21H1 but it still generates this warning, most likely article above forget this version exists.
Which "Learn more" hyperlink leads to limitation details above, even worse for older Windows: limitations against file-encrypting malware and screen lockers (only these two), most likely if System Watcher is the last resort. AFAIK, limitations mean there's still functionality but will not be optimal, except it directly said that certain functionality won't work at all.
I think is both are important but the Kaspersky functionality trade-off is a bit too much variety compared to Credential Guard.
Still, no idea what three kinds of three browser protection mean, also what kind of unauthorized remote access is, RCE?
Any suggestions for my case (latest Windows)?