Gandalf_The_Grey
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Forum Veteran
The LockBit ransomware gang is one of the most notorious organized cybercrime syndicates that exists today. The gang is behind attacks targeting private-sector corporations and other high-profile industries worldwide. News and media outlets have documented many LockBit attacks, while security vendors offer technical assessments explaining how each occurred. Although these provide insight into the attacks, I wanted to know more about the human side of the operation to learn about the insights, motivations, and behaviors of the individuals on the other side of the keyboard. To prepare for this project, I spent months developing several online personas and established their credibility over time to gain access to the gang’s operation.
Over the months, I spent my time on criminal forums and private chat groups used by ransomware criminals and gained inside knowledge about the LockBit gang itself. I identified the accounts and infrastructure used by the gang and the criminals they interacted with. I could see the tools and resources used to manage and conduct attacks from the adversary’s perspective. More importantly, I learned about the opinions, personal habits, motivations, and insecurities of the human criminals behind the operation. Then, I took many of the public events and high-profile attacks to include theories previously made about the LockBit gang and tried to capture the side of this very interesting story.
Next, I will walk through the entire lifecycle of LockBit activity from September 2019 until January 2022. I will detail the gang’s criminal operation and add LockBit’s version of events to tell the story, as it has not been detailed before. In conducting this research and analysis, I found several mistakes made in attributing the early activities of the LockBit gang, which I will discuss. Finally, I will provide a complete intelligence assessment focused on my findings, open-source information, technical data, and human intelligence gained while profiling LockBit itself.
If you are not interested in the larger story, you may want to skip to the “Unmasking Lockbit” section near the end of this report for a summary of unique findings derived from the human intelligence I gained from my interactions with Lockbit. However, the screenshots and details surrounding each conversation are included throughout the body of the report itself in the order in which they took place.
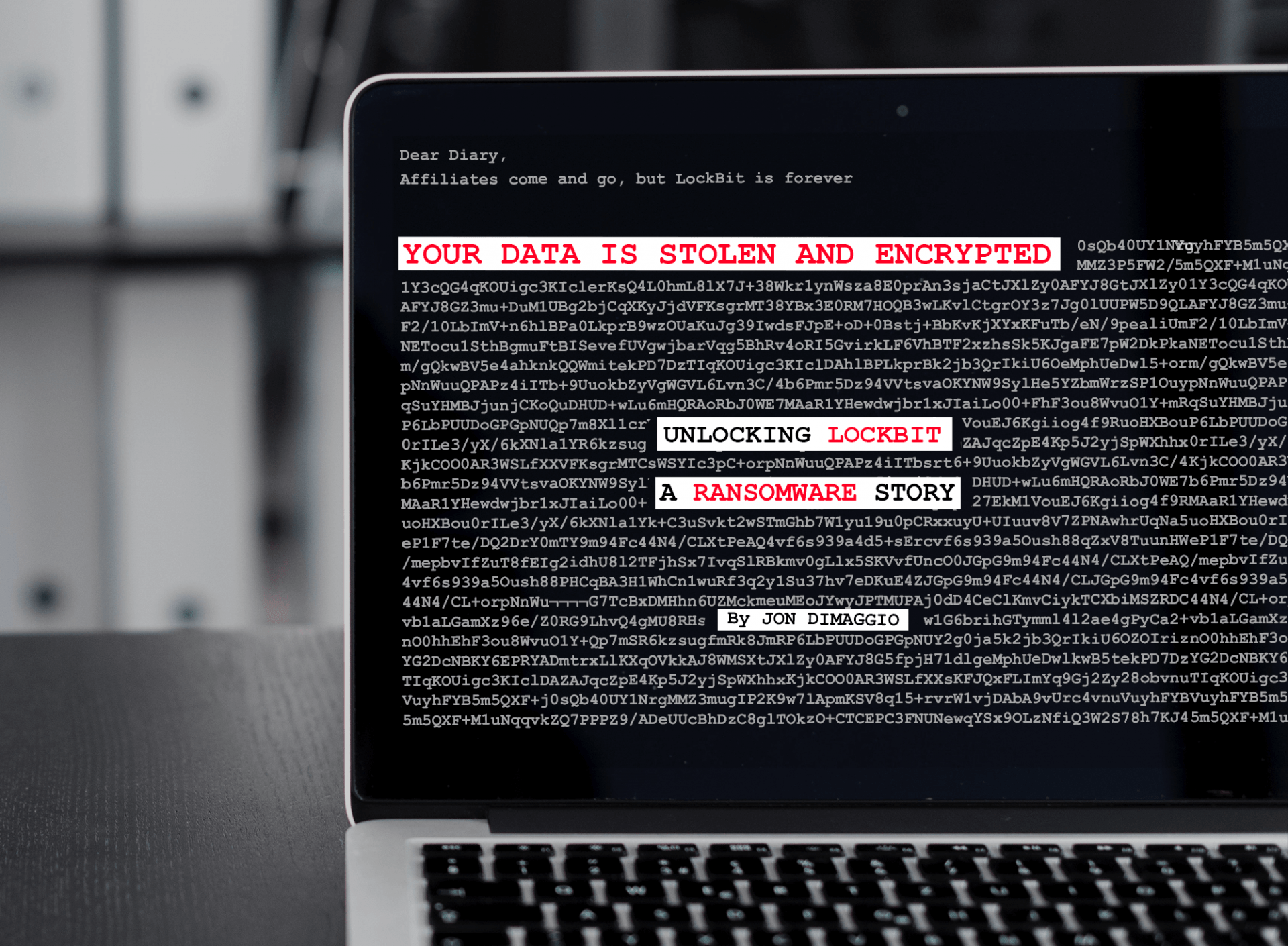
Ransomware Diaries: Volume 1 | Analyst1
Conducting a behavioral profile of ransomware attackers will give you a better understanding of who is behind the attacks threatening your organization. Behavioral profiling adds value to defenders who can use it to identify an attacker and negotiators who will know the motivations and beliefs...
