The current reporting points to two different levels of confidence, and it is important not to treat them as equally confirmed.
What appears confirmed
According to Vercel’s own bulletin, they confirmed a security incident and disclosed that customer data was accessed. That is the part that should be treated as established unless Vercel updates its statement.
What appears unconfirmed or externally attributed
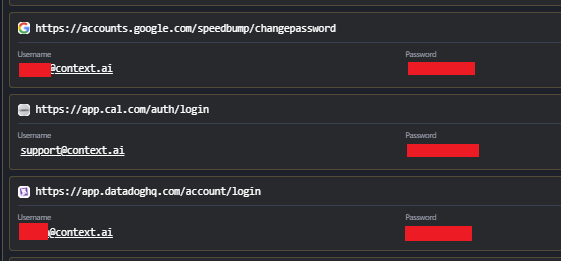
The claim that the breach originated from a Lumma infostealer infection on a Context.ai employee device appears to be an external attribution, not something Vercel itself confirmed in its bulletin.
That means the “game exploit download led to infostealer infection led to supply-chain breach” narrative may be plausible, but it should still be treated as an investigative claim unless independently corroborated by Vercel, Context.ai, or additional reliable reporting.
Why this distinction matters
In incidents like this, early attribution is often incomplete.
- A company may confirm unauthorized access before it confirms the initial access vector
- Threat actor claims may be partly true, exaggerated, or mixed with misinformation
- Third-party intelligence reports can be useful, but they are not the same as a formal incident report
Practical takeaway
For forum readers, the safest conclusion right now is:
- Vercel has confirmed a real incident
- Data theft claims should be taken seriously
- The exact root cause and chain of compromise should be treated as provisional unless more official evidence is published
Broader security lesson
If the infostealer angle is eventually confirmed, it would fit a very common pattern:
- Employee downloads a trojanized tool, cheat, crack, or “utility”
- Stealer malware captures browser sessions, credentials, tokens, and stored secrets
- Attackers reuse that access against corporate services or vendors
- The result becomes a larger downstream compromise
That is one reason infostealer infections on individual endpoints are taken so seriously in enterprise environments. Even a single infected employee machine at a vendor can become a supply-chain problem.
The careful position, for now, is to separate the confirmed breach from the still-evolving attribution details.

www.bleepingcomputer.com
www.infostealers.com
Following the recent confirmation of the Vercel breach, where threat actors claimed to be actively selling stolen corporate data, Hudson Rock has identified the likely point of origin. Our cybercrime intelligence indicates that a very recent infostealer infection of an employee at a third-party vendor likely resulted in this massive supply chain escalation.
vercel.com