This program uses a bootloader by Thinstall. When I search on Virustotal for applications with the same bootloader they all have 12+ detections. So the bootloader is likely the detected component.
Although Thinstall is a legitimate program, it seems to have been abused for malware and cracking which often leads to automatic detection of the bootloader and injection component (I exclude manual signature creation here because a human would know this to be legitimate and would more likely use concrete detection names). The major vendors either have better FP protection in place or are more likely to be contacted by the Thinstall company if false positives occur, which would explain why they don't have a detection on the Thinstall bootloader.
I find it noteworthy that there is a Yara match on
Heaven's Gate code which is normally not used by legitimate applications.
The original setup of this application is signed:
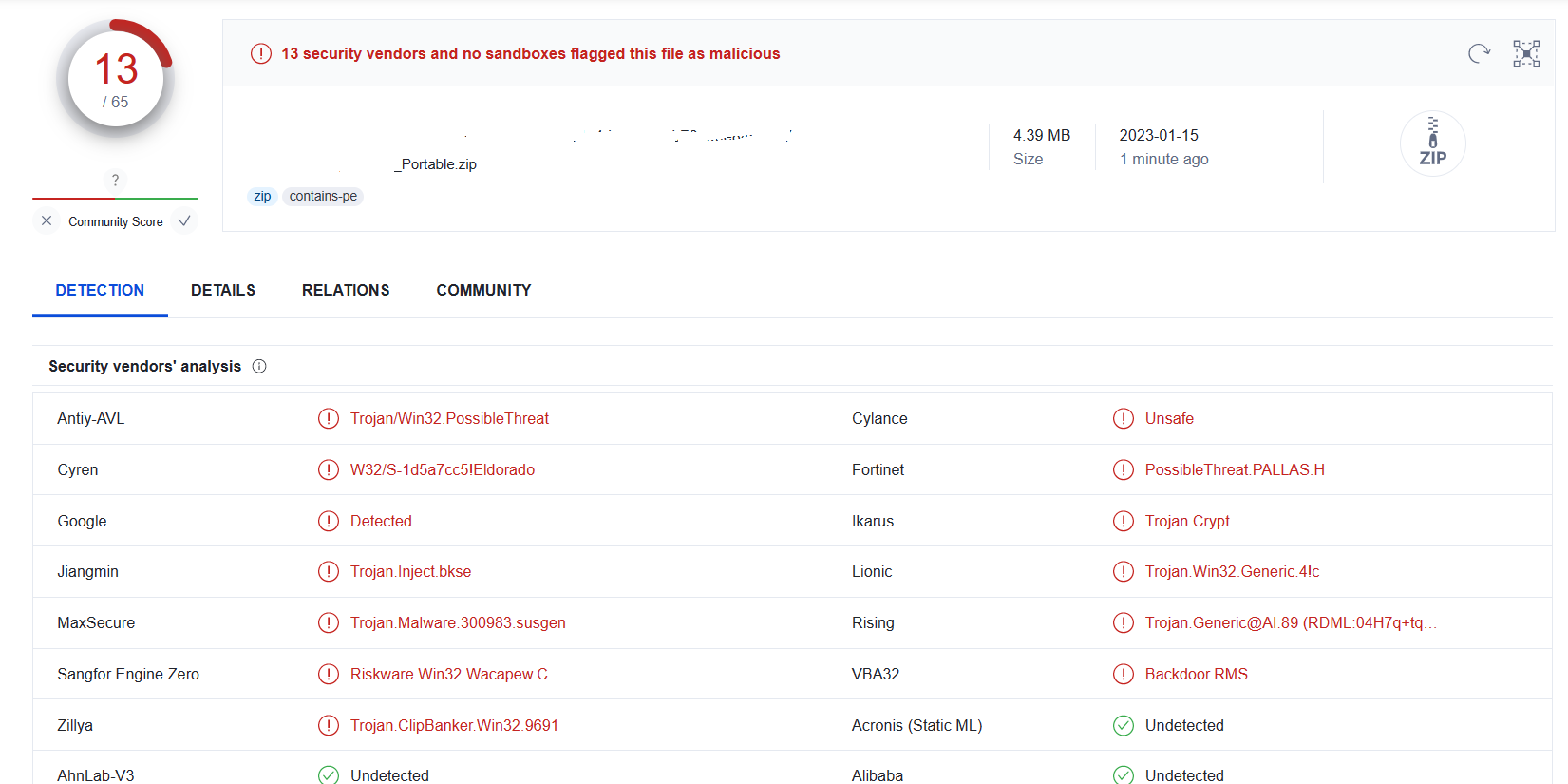
VirusTotal
Whereas the files contained in this archive are not signed. That is unusual. If the vendor of the program already have a signing process in place, they would use it on detected files to prevent the detections. Might be because this is an older version or because it was modified. However, the version numbers are not far apart: Newest version is 5.1.1. and the one you have there is 5.1.0.233
I see two possibilities here (you don't need to tell me which one it is):
- The actual vendor used Thinstall to create a portable application and this is an old version that was not signed yet. They do not fix detections by contacting vendors because it is an old version.
- This is a cracked version of the program that uses the bootloader to circumvent the protection and licensing system. Such programs are treated as "don't care" by antivirus vendors. A discussion about legitimacy of cracked programs is not allowed here on MalwareTips.
In case 1 you need to use the updated version. In case 2 you better not use it.
So actually in both cases you better don't use the exact program you linked here.