- Nov 10, 2017
- 3,250
Why it matters: Researchers from the Technische Universität Berlin have demonstrated that AMD's Secure Encrypted Virtualisation (SEV) technology can be defeated by manipulating input voltages, compromising the technology in a similar way to previous attacks against its Intel counterpart.
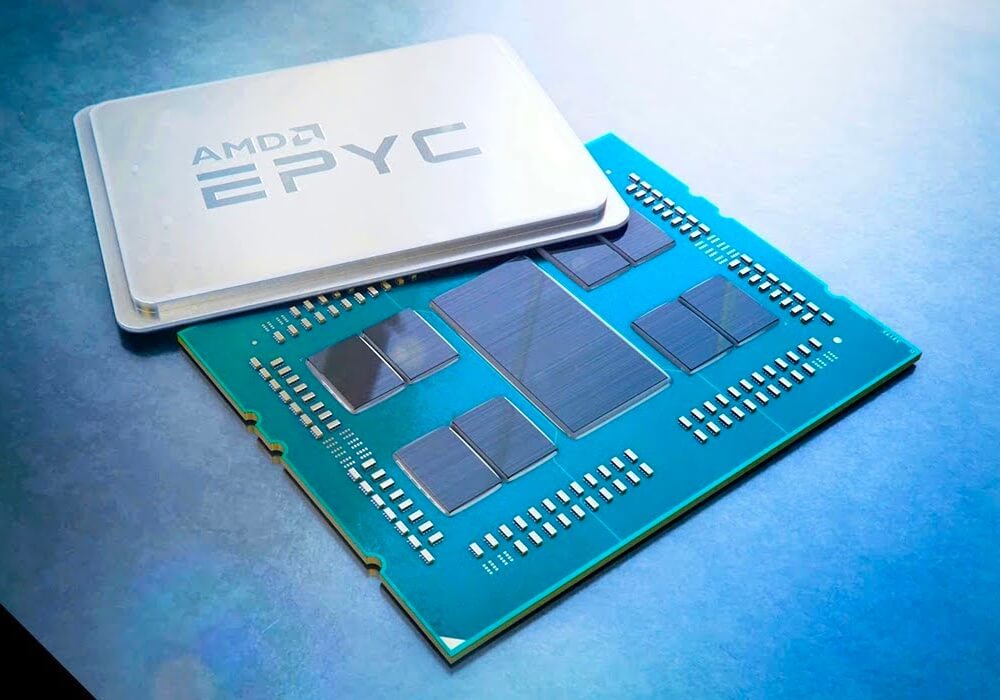
SEV relies on the Secure Processor (SP), a humble Arm Cortex-A5, to provide a root of trust in AMD EPYC CPUs (Naples, Rome and Milan -- Zen 1 through 3).
The research paper -- toting the amusing-yet-wordy title of "One Glitch to Rule Them All: Fault Injection Attacks Against AMD’s Secure Encrypted Virtualization" -- describes how an attacker could compromise the SP to retrieve encryption keys or execute arbitrary code.
"By manipulating the input voltage to AMD systems on a chip (SoCs), we induce an error in the read-only memory (ROM) bootloader of the AMD-SP, allowing us to gain full control over this root-of-trust."
The rest
Voltage manipulation can bypass hardware security on AMD's server CPUs
SEV relies on the Secure Processor (SP), a humble Arm Cortex-A5, to provide a root of trust in AMD EPYC CPUs (Naples, Rome and Milan – Zen 1 through 3).
 www.techspot.com
www.techspot.com



