Last year, it took Avast more than 3 months to finally detect a false negative fake 360, which had been VT 30+ or maybe more for a long time, as malware.
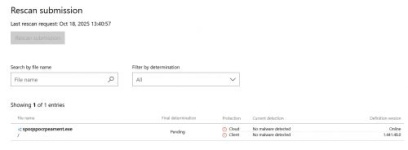
This time we talk about MD. Although not been that long until now. It has been a few weeks since I submitted the following false negative fake APP to Microsoft, and I resubmitted it again this week, but MD just missed it. Is it common, and does it happen often to all vendors?


The sample: VirusTotal
Anyrun report: Analysis https://wormhole.app/E42JRQ#A821lv6tQ3BAfdyFfM30HQ Malicious activity - Interactive analysis ANY.RUN
In case you want to test the file, you can find the download link in the Community comment from the Virustotal page.
Note that although it's just VT 6 for now, with the first submission at 2025-10-18 05:38:05 UTC, a few other (VT negative) vendors can block it with behavioural already.
This time we talk about MD. Although not been that long until now. It has been a few weeks since I submitted the following false negative fake APP to Microsoft, and I resubmitted it again this week, but MD just missed it. Is it common, and does it happen often to all vendors?
The sample: VirusTotal
Anyrun report: Analysis https://wormhole.app/E42JRQ#A821lv6tQ3BAfdyFfM30HQ Malicious activity - Interactive analysis ANY.RUN
In case you want to test the file, you can find the download link in the Community comment from the Virustotal page.
Note that although it's just VT 6 for now, with the first submission at 2025-10-18 05:38:05 UTC, a few other (VT negative) vendors can block it with behavioural already.