F
ForgottenSeer 85179
It's a bit tricky. Click on 0$ and then the Download button appeari cannot download it unless i donate
It's a bit tricky. Click on 0$ and then the Download button appeari cannot download it unless i donate
For keyloggers a Firewall is enough.this is done already
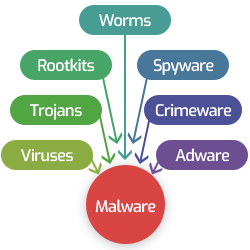
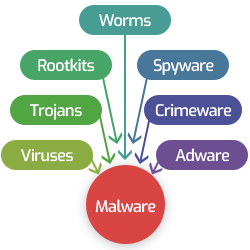
however i am thinking about methods such as this type of malware could infect the PC
This like security overdose and my laptop would be dead and not usable anymoreSyshardener+OSAmor+Bitdefender Total Security
But with bifdefender it would be heavyMaybe a tad overkill but I don't think heavy, OSArmour and Syshardener are very light.
Keylogger may not abuse legit application process to bypass windows firewall rulesFor keyloggers a Firewall is enough.
Keylogger may not abuse legit application process to bypass windows firewall rules??
Of course it can, but there's easier ways like tunneling.Keylogger may not abuse legit application process to bypass windows firewall rules??
So firewall is not optimum solution although it may prevent the data breach but will not detect the infection occuredOf course it can, but there's easier ways like tunneling.
You can detect them through Windows Defender ATP, and AV isn't supposed to let it run in first place.So firewall is not optimum solution although it may prevent the data breach but will not detect the infection occured
Has keyloggers has some symptoms which may trigger certain AV module ?? And if which part??
For you, Kaspersky Anti-Virus Free (or security cloud free) + SpyShelter Free. This will be quite enough for you. If you want syshardener apply. Optional.i am really think to use your combo is it light ?? have you faced any conflict problems ??
You can detect them through Windows Defender ATP, and AV isn't supposed to let it run in first place.
Keylogger needs elevated privileges or a known exploit to remain undetected, unless we talking Linux due to the fact everyone believes they don't need AV, nor they pack firewall by default, you can code one in seconds for it (with no need for elevated privileges), already done this multiple times in the past for science reasons.


Thanks a lot for the links @ichito i will take a look on them to gain more understandingYou can look at some examples of below...a lot of info about malware

Keyloggers: How they work and how to detect them (Part 1)
This report provides an overview of different types of keyloggers, gives examples of losses caused by keyloggers, and provides recommendations on how to protect against them.securelist.com
What is a Keylogger? Definition, Risks, and Prevention | Xcitium
What is a keylogger, how it works, and the risks it poses to your privacy and security? Learn how to detect and remove keyloggers and protect them from viruses.enterprise.comodo.combut about legal apliacation also
Keylogger
A keylogger is a type of spyware that can be used to collect keystrokes that you type. Learn more here and protect yourself.www.malwarebytes.com
Top keyloggers (keystroke loggers) 2025. Comparison and Reviews.
Read detailed independent comparison and reviews about the top of world-famous keyloggers. Choose undetectable hidden keylogger (keystroke logger) and download it for free! With a keylogger, you'll find who is using your PC and what for!www.keyloggers.com