Did you know that Windows 10 has a ransomware protection feature? If you answered no, you’re not alone. Most people are not aware that on Windows 10, users have the option of activating “Controlled folder access”, a feature available with the Microsoft Defender Exploit Guard (part of Microsoft Defender Antivirus).
When turned on it prevents ransomware from encrypting your data and protects files from malicious apps trying to make unwanted changes. Considering this type of cyberthreat is on the rise – and increasingly for Windows PC users – now is a good time to familiarize yourself with this optional feature and decide if it makes sense for you to activate it.
How does a Windows PC get infected with ransomware?
A ransomware attack starts with a cybercriminal infecting a victim’s computer with malware that encrypts files. This can be achieved by exploiting vulnerabilities in outdated software, but often a user is tricked into installing malware via clicking on a malicious link or email attachment.
Once the target device has been infected, the attackers will demand a ransom for the release of the files and threaten to destroy or leak the documents if they don’t get paid. If you want to learn more, read this blog article with five helpful tips on how to prevent ransomware attacks.
How to enable Windows ransomware protection
First, make sure you are running the latest version of Windows 10. To find the ransomware protection, type “Windows Security” in the lower-left search bar to open the Windows Security Center app. Once there, you’ll see the Virus & threat protection, and under that “Virus & threat protection settings” where you can click on Manage settings. You get to these settings faster by clicking on Manage ransomware protection at the bottom of the page.
In either case, find the Controlled folder access, then click on Manage Controlled folder access and switch the toggle on. By activating this feature, Windows 10 will monitor changes made by an app to files in protected folders. If an unknown or suspicious program tries to access a protected file, access will be blocked, and you will receive an alert of the activity.
If you click underneath on Block history, you can access the “Protection history” page to view which folders have blocked access. Clicking on Protected folders displays what folders are protected and allows you to add or remove folders from the list. Documents, Pictures, Videos, Music, Desktop, Favorites are protected by default, to include more click on + Add a protected folder, select the relevant folder in the Explorer window that appears and choose Select Folder.
You also have the option to let apps you trust make changes on the protected folders when you click Allow an app by Controlled folder access. However, this is only necessary in special cases. For example, when the protection blocks a trusted program from working properly, like when a photo is saved in a protected storage folder by an image editor. If the folder access has already blocked a trusted program, you’ll see that after clicking Recently blocked apps.
Why is Windows ransomware protection not on by default?
Now that you know about this feature you might be asking: if it’s so great why is it not turned on by default? Well for starters, the feature often detects false positives, which can lead to another set of problems. For example, if a program you do trust is targeted as being suspicious, the warning might come at an inconvenient moment. It might crash the program or leave you with no way to save your work.
It’s not possible to know which programs Microsoft finds dubious in advance so it’s hard to predict if your typical apps or games will work with the ransomware protection activated. A potential solution to avoid trusted programs being targeted as suspicious is to add them to the Controlled folder access whitelist. But that’s not exactly a simple solution either – especially for those who are not so technically inclined as it requires finding the executable file that runs the program. Another potential drawback is that any files in a shared network or on an external hard drive must be manually added to the list of protected folders, which again, is not necessarily quick or easy for everyone.
So, while there are some advantages to opting-in to the Windows ransomware protection, you might want to think twice. Especially if you are not in the mood to make many manual adjustments if things don’t work as per normal. In the end, it might be easier to toggle Controlled Access folder back to off and get yourself a powerful antivirus for Windows that blocks threats like ransomware in real-time.
Windows 10 offers ransomware protection – but should you use it?
- Thread starter CyberPanther
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
There is also another anti-ransomware feature in WD eg. ASR rules.
One ASR rule "Use advanced protection against ransomware" is directly related to ransomware. But also other ASR rules can prevent many ransomware attacks by blocking the delivery methods commonly used in such attacks.
One ASR rule "Use advanced protection against ransomware" is directly related to ransomware. But also other ASR rules can prevent many ransomware attacks by blocking the delivery methods commonly used in such attacks.
Good to see they're not being biased and saying Avira is better than Windows Defender against ransomware unlike some other AVs do (Also the founder of a particular AV that I won't name  ).
).
But tbh, from my experience I would say, overall Windows Defender has better signatures than Avira. Avira's signature is pretty bad when it comes to scripts.
But tbh, from my experience I would say, overall Windows Defender has better signatures than Avira. Avira's signature is pretty bad when it comes to scripts.
I think you have in mind the WD cloud-delivered protection and "Block at first sight". From the tests, it follows that WD standard signatures (offline and in the cloud) are not the best. But, the fast signatures (related to "Block at first sight" feature), are very good.Good to see they're not being biased and saying Avira is better than Windows Defender against ransomware unlike some other AVs do (Also the founder of a particular AV that I won't name).
But tbh, from my experience I would say, overall Windows Defender has better signatures than Avira. Avira's signature is pretty bad when it comes to scripts.
I also have enabled the protected folders feature. It produces many false positives of which 99% is related to blocking memory access and data access to users folder (80% blocking access to AppData).
During the past 6 months I have ignored memory access blocks and whitelisted most of the programs which were not allowed to access my AppData folder.
Protected folders seems to use a different whitelist than Smart Screen (I downloaded a program which I could run by Smartscreen, but that same program was blocked by Protected Folders).
During the past 6 months I have ignored memory access blocks and whitelisted most of the programs which were not allowed to access my AppData folder.
Protected folders seems to use a different whitelist than Smart Screen (I downloaded a program which I could run by Smartscreen, but that same program was blocked by Protected Folders).
Default-Deny software are unable to determine between a non-threat and a threat. Similar to HIPS/IDS or even a Sandbox, it's either 100% Blocked or 100% Allowed.
Controlled Folder Access is only beneficial for users who know how it works, otherwise you're in a world of trouble.
More may be familiar with their other services, such as OneDrive with Microsoft 365 (Office) subscription - this is more recovery, than prevention.
 support.microsoft.com
support.microsoft.com
Controlled Folder Access is only beneficial for users who know how it works, otherwise you're in a world of trouble.
More may be familiar with their other services, such as OneDrive with Microsoft 365 (Office) subscription - this is more recovery, than prevention.
How to detect ransomware and recover files using OneDrive - Microsoft Support
Learn about the automatic ransomware detection built in to OneDrive and how you can restore your OneDrive if something goes wrong.
I had cloud protection in mind but not block at first sight which requires MOTM, right?. Avira has excellent signatures for exe based samples which also applies for WD but Avira's signature for both offline and cloud based detection for malicious scripts are pretty bad in my experience. 3-4 months ago I was testing Avira on my own from 33 script samples dating from latest to 3 months old at that time. Avira detected 4 of those by signature and 4 more after execution through cloud. So only 8 out of 33 while WD detected all of them by offline signatures. My point is, Avira and WD both have good signatures against exe samples but WD is much better for script based malware offline and online combined.I think you have in mind the WD cloud-delivered protection and "Block at first sight". From the tests, it follows that WD standard signatures (offline and in the cloud) are not the best. But, the fast signatures (related to "Block at first sight" feature), are very good.
Anyway, this is a bit off topic.
For ransomware WD has this control folder access feature which is great but can be problematic due to its block all if not whitelisted approach while Avira don't have such feature I think.
An interesting test - also in relation to ransomware. Some WD offline detections could be due to AMSI too. Anyway, such a big difference is not good for Avira....
3-4 months ago I was testing Avira on my own from 33 script samples dating from latest to 3 months old at that time. Avira detected 4 of those by signature and 4 more after execution through cloud. So only 8 out of 33 while WD detected all of them by offline signatures.
...
Being that WD Ransomware protection can be problematic, what is the alternate choice for Ransomware protection that is free?
Maybe Malwarebytes Anti-Ransomware Free?
Maybe Malwarebytes Anti-Ransomware Free?
or you could use Kaspersky security cloud free system watcher will pretty much detect any ransomware under the sun.Being that WD Ransomware protection can be problematic, what is the alternate choice for Ransomware protection that is free?
Maybe Malwarebytes Anti-Ransomware Free?
Most top AVs use anti-ransomware protection similar to the below (taken from Kaspersky):
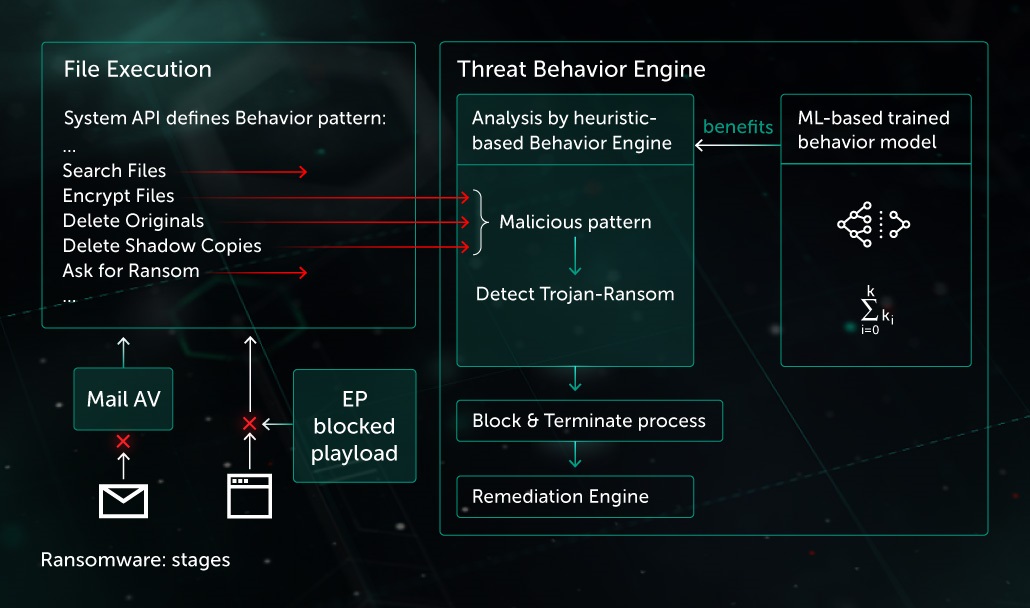
It can be very efficient for known ransomware techniques and also for many unknown (but not so efficient). There are two valuable additions to this protection model:
I do not think that dedicated anti-ransomware protection is required in the home environment on Windows 10 with Kaspersky Security Cloud. I would rather add some restrictions for scripting (SysHardener, SWH, etc).
If you like Kaspersky Security Cloud free (many people do) then it will be a good choice. If you like WD, then you can get similar protection by applying the ConfigureDefender High Protection Level.
It can be very efficient for known ransomware techniques and also for many unknown (but not so efficient). There are two valuable additions to this protection model:
- Malware prevention via whitelisting or applying the software that can effectively reduce the attack surface area.
- Protection of some folders and disk areas (Shadow copies, MBR, etc.) even when the ransomware is already running in the system.
I do not think that dedicated anti-ransomware protection is required in the home environment on Windows 10 with Kaspersky Security Cloud. I would rather add some restrictions for scripting (SysHardener, SWH, etc).
If you like Kaspersky Security Cloud free (many people do) then it will be a good choice. If you like WD, then you can get similar protection by applying the ConfigureDefender High Protection Level.
If you run WD i would say comodo firewall is the most easy setup, either block all not regonized things or just reject them as cruelsister doesBeing that WD Ransomware protection can be problematic, what is the alternate choice for Ransomware protection that is free?
Maybe Malwarebytes Anti-Ransomware Free?
Kaspersky antiransomware tool is more effective than MBAE probably, but its more like 50/50 what get past...so just backup anything worthy and go with default deny solution against zerodays like comodo firewall, voodooshield isnt bad either
this message is written by comodo fan boy
But doubt you run into any ransomware, just go with overall security not just against ransomware but against everything
Ha, ha ... and walking high mountains is the best way to be healthy.If you run WD i would say comodo firewall is the most easy setup, ...
...
Anyway, CF in CS settings is strong protection (close to default-deny setup). The protection idea is simple and efficient (but not necessarily easy to use).
Last edited:
For me to cover my bases, I am using WD+ConfigDefHIGH+SWH. Being that WD Anti-Ransomware is off, I have VS Pro to cover everything else on Windows 10.
I have VS Pro to cover everything else on Windows 10.
What mode do you run VoodooShield in?
I like this setup, seems strong and lean.
What mode do you run VoodooShield in?
I like this setup, seems strong and lean.
Autopilot in Smart Mode/Moderate Profile. Automatically Allow Safe Programs in Whitelisting.
You may also like...
-
Expired iObit Advanced SystemCare 19 PRO - 6 months license
- Started by Brownie2019
- Replies: 0
-
DefenderWrite Tool Let Attackers Inject Malicious DLLs into AV Executable Folders
- Started by Khushal
- Replies: 7
-
On Sale! AVG Internet Security 1PC, 1Yr, $ 6.89
- Started by Brownie2019
- Replies: 0
-
-
On Sale! Avast Premium Security 1 Device 1 Year 9.99€
- Started by Brownie2019
- Replies: 0
