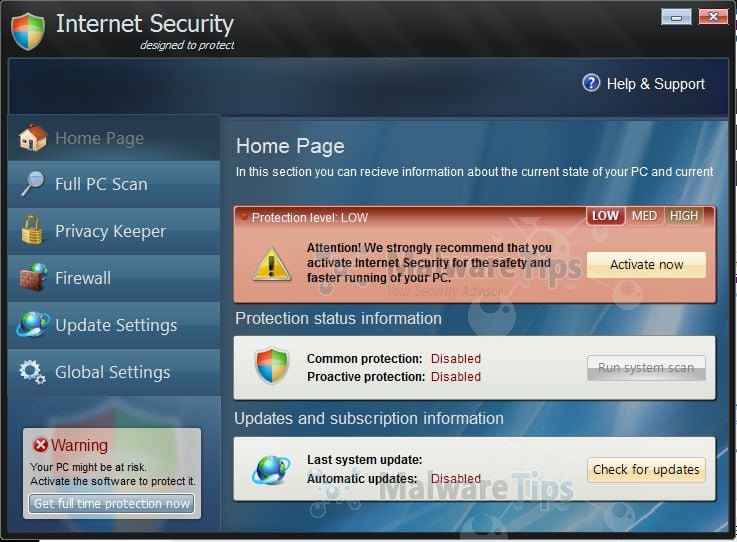
Internet Security 2014 “designed to protect” is a computer virus, which pretends to be a legitimate security program and claims that malware has been detected on your computer. If you try to remove these infections, Internet Security 2014 will state that you need to buy its full version before being able to do so.
Internet Security 2014 trojan targets users browsing Internet websites, and rely on social engineering to deliver its payload.
On infected or hacked websites users are prompted by a pop-up window that has been carefully crafted to resemble a legitimate security warning. These pop-up windows typically alert a user of a computer infection, and then prompt the user to download and install Internet Security 2014 to resolve the apparent issue.
Some of the infections may have come from users downloading an infected codec file when they were trying to watch a video online, or users who receive a spam email and open an infected email attachment.
Once installed, Internet Security 2014 will display fake security alerts that are designed to think that your data is at risk or that your computer is severely infected.These messages include:
Security Warning
Malicious program has been detected. Click here to protect your computer.Firewall Warning
Hidden file transfers to remote host has been detected.
has detected a leak of your files through the Internet. We strongly recommend that you block the attack immediately.
In reality, none of the reported issues are real, and are only used to scare you into buying Internet Security 2014 and stealing your personal financial information.
As part of its self-defense mechanism, Internet Security 2014 virus has disabled the Windows system utilities, including the Windows Task Manager and Registry Editor, and will block you from running certain programs that could lead to its removal.
This rogue antivirus has also modified your Windows files associations, and now whenever you are trying to open a program, Internet Security 2014 virus will block this operation and display a bogus notification in which will report that the file is infected.
notepad.exe can not start
File notepad.exe is infected by W32/Blaster.worm. Please activate Internet Security 2014 to protect your computer.
If your computer is infected with Internet Security 2014 virus, then you are seeing the following screens:
Internet Security 2014 is a scam, and you should ignore any alerts that this malicious software might generate.
Under no circumstance should you buy Internet Security 2014 as this could lead to identity theft, and if you have, you should contact your bank and dispute the charge stating that the program is a scam and a computer virus.
Registration key for Internet Security 2014 “designed to protect”
As an optional step,you can use any of the following license keys to register Internet Security “designed to protect” and stop the fake alerts.
Internet Security 2014 “designed to protect” Activation Key: Y68REW-T76FD1-U3VCF5A
Please keep in mind that entering the above registration code will NOT remove Internet Security 2014 “designed to protect” from your computer, instead this activation code will just stop the fake alerts so that you’ll be able to complete our removal guide more easily.
Internet Security 2014 – Virus Removal Guide
STEP 1: Remove Internet Security 2014 malicious files with Malwarebytes Anti-Malware
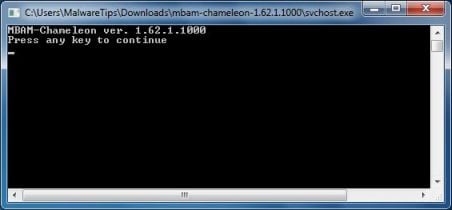
Malwarebytes Chameleon technologies will allow us to install and run a Malwarebytes Anti-Malware scan without being blocked by Internet Security 2014.
- Right click on your browser icon, and select Run As or Run as Administrator. This should allow your browser to open so that we can then download Malwarebytes Chameleon.
If you’ll see a “Warning! The site you are trying visit may harm your computer!” message in your web browser window, you can safely click on the Ignore warnings and visit that site in the current state (not recommended) link, because this a bogus alert from Internet Security 2014. - Download Malwarebytes Chameleon from the below link, and extract it to a folder in a convenient location.
MALWAREBYTES CHAMELEON DOWNLOAD LINK (This link will open a new web page from where you can download Malwarebytes Chameleon)
- Make certain that your infected computer is connected to the internet and then open the Malwarebytes Chameleon folder, and double-click on the svchost.exe file.
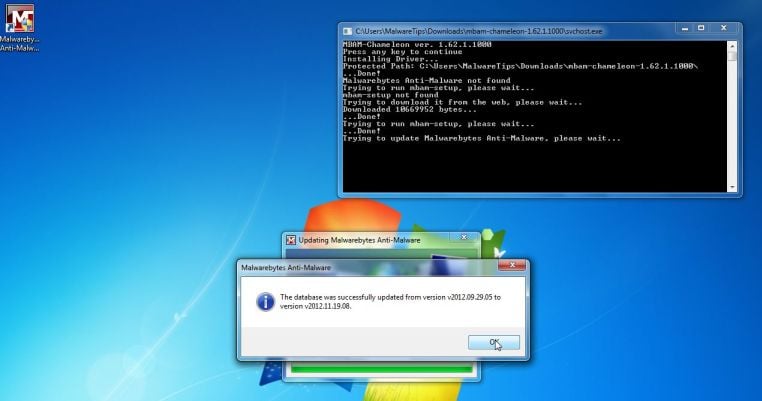
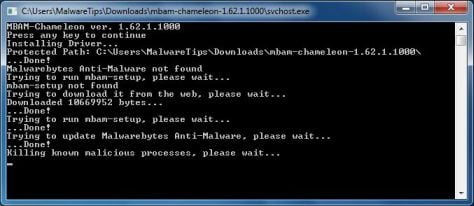
IF Malwarebytes Anti-Malware will not start, double-click on the other renamed files until you find one will work, which will be indicated by a black DOS/command prompt window. - Follow the onscreen instructions to press a key to continue and Chameleon will proceed to download and install Malwarebytes Anti-Malware for you.
- Once it has done this, it will update Malwarebytes Anti-Malware, and you’ll need to click OK when it says that the database was updated successfully.
- Malwarebytes Anti-Malware will now attempt to kill all the malicious process associated with Internet Security 2014.Please keep in mind that this process can take up to 10 minutes, so please be patient.
- Next, Malwarebytes Anti-Malware will automatically open and perform a Quick scan for Internet Security 2014 malicious files as shown below.
- Upon completion of the scan, click on Show Result
- You will now be presented with a screen showing you the malware infections that Malwarebytes Anti-Malware has detected.
Make sure that everything is Checked (ticked),then click on the Remove Selected button.
- After your computer restarts, open Malwarebytes Anti-Malware and perform a Full System scan to verify that there are no remaining threats
STEP 2: Remove Internet Security 2014 malicious registry keys with RogueKiller
- You can download the latest official version of RogueKiller from the below link.
ROGUEKILLER DOWNLOAD LINK (This link will automatically download RogueKiller on your computer) - Double click on RogueKiller.exe to start this utility and then wait for the Prescan to complete.This should take only a few seconds, then click on the Scan button to perform a system scan.
- After the scan has completed, press the Delete button to remove Internet Security 2014 malicious registry keys or files.
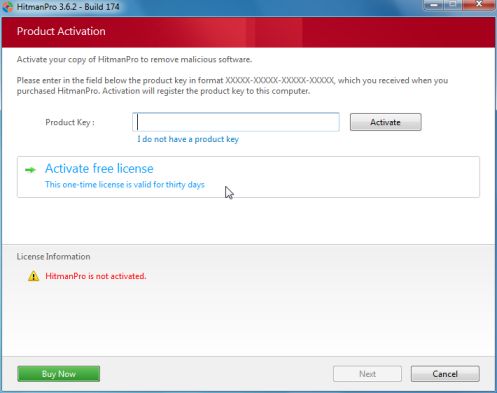
STEP 3: Remove Internet Security 2014 rootkit with HitmanPro
In some cases, Internet Security 2014 will also install a rootkit on victims computer.To remove this rootkit we will use HitmanPro.
- You can download HitmanPro from the below link, then double click on it to start this program.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro)
IF you are experiencing problems while trying to start HitmanPro, you can use the Force Breach mode.To start HitmanPro in Force Breach mode, hold down the left CTRL-key when you start HitmanPro and all non-essential processes are terminated, including the malware process. (How to start HitmanPro in Force Breach mode – Video) - HitmanPro will start and you’ll need to follow the prompts (by clicking on the Next button) to start a system scan with this program.
- HitmanPro will start scanning your computer for Internet Security 2014 malicious files as seen in the image below.
- Once the scan is complete,you’ll see a screen which will display all the infected files that this utility has detected, and you’ll need to click on Next to remove this malicious files.
- Click Activate free license to start the free 30 days trial and remove all the malicious files from your computer.
![Internet Security 2014 malware [Image: Internet Security 2014 infection]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/Internet-Security-2014-malware.jpg)
![Internet Security 2014 Warning [Image: Internet Security 2014 Warning]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/Internet-Security-2014-Warning.jpg)
![Internet Security 2014 Firewall Warning [Image: Internet Security 2014 Firewall Warning]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/Internet-Security-2014-Firewall-Warning.jpg)
![Internet Security 2014 Activation code [Image: Internet Security 2014 Activation Key]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/Internet-Security-2014-activation-code.jpg)
![Right click on your Web Browser icon and click on Run As Administrator [Image: Starting web browse on infected computer]](http://malwaretips.com/blogs/wp-content/uploads/2013/03/open-web-browser.jpg)
![Extract Malwarebytes Chameleon utility [Image: Extract Malwarebytes Chameleon utility]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/malwarebytes-chameleon-zip.jpg)
![Double click on svchost.exe [Image: Double click on svchost.exe]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/malwarebytes-chameleon-svchost.jpg)
![Malwarebytes Anti-Malware scanning for Internet Security 2014 [Image: Malwarebytes Anti-Malware scanning for Internet Security 2014]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Click on Remove Selected to get rid of Internet Security 2014 [Image:Malwarebytes removing virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)
![Click on the Start button to perform a system scan [Image: RogueKiller scaning for Internet Security 2014 virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/roguekiller-scan.jpg)
![Press Delete to remove Ib.Adnxs malicious registry keys [Image: RogueKiller Detele button]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/roguekiller-delete.jpg)












Hello,
This are most likely just some left over files, however for your peace of mind, you can run a scan with these tools:
STEP 1: Run a scan with ESET Online Scanner
1.Download ESET Online Scanner utility.
ESET Online Scanner Download Link : http://download.eset.com/special/eos/esetsmartinstaller_enu.exe
2. Double click on the Eset installer program (esetsmartinstaller_enu.exe).
3.Check Yes, I accept the Terms of Use, then click the Start button.
4.Check Scan archives and push the Start button.
5. ESET will then download updates for itself, install itself, and begin scanning your computer. Please be patient as this can take some time.
6. When the scan completes, click on the Finish button.
STEP 2: Run a scan with Kaspersky Virus Removal Tool:
1. You can download from Kaspersky Virus Removal Tool from here : http://www.kaspersky.com/antivirus-removal-tool?form=1
2. Double click the setup file to run it, then follow the onscreen prompts until it is installed
Click the Options button (the ‘Gear’ icon), then make sure only the following are ticked:
System Memory
Hidden startup objects
Disk boot sectors
Local Disk (C:)
Also any other drives (Removable that you may have)
3. Then click on Actions on the left hand side
4. Click Select Action, then make sure both Disinfect and Delete if disinfection fails are ticked
5. Click on Automatic Scan, then click the Start Scanning button, to run the scan.
Stay safe!
Hello,
Lets run the below scans:
Run a scan with RogueKiller
1. Please download the latest official version of RogueKiller.
RogueKiller Download Link : http://www.sur-la-toile.com/RogueKiller/RogueKiller.exe
2. Double click on RogueKiller.exe to start this utility and then wait for the Prescan to complete.This should take only a few seconds and then you can click the Scan button to perform a system scan.
3. After the scan has completed, press the Delete button to remove any malicious registry keys.
Run a scan with ESET Online Scanner
1.Download ESET Online Scanner utility.
ESET Online Scanner Download Link : http://download.eset.com/special/eos/esetsmartinstaller_enu.exe
2. Double click on the Eset installer program (esetsmartinstaller_enu.exe).
3.Check Yes, I accept the Terms of Use, then click the Start button.
4.Check Scan archives and push the Start button.
5. ESET will then download updates for itself, install itself, and begin scanning your computer. Please be patient as this can take some time.
6. When the scan completes, click on the Finish button.
Next, can you please run a scan with Combofix and post the logs here so that I can get an idea on what’s going on:
You can download ComboFix from here: http://download.bleepingcomputer.com/sUBs/ComboFix.exe
VERY IMPORTANT !!! Save as Combo-Fix.exe during the download.ComboFix must be renamed before you download to your Desktop
Close any open browsers.
Very Important!!!> Temporarily disable your anti-virus, script blocking and any anti-malware real-time protection before performing a scan. They can interfere with ComboFix or remove some of its embedded files which may cause “unpredictable results”.
WARNING: Combofix will disconnect your machine from the Internet as soon as it starts
Please do not attempt to re-connect your machine back to the Internet until Combofix has completely finished.
If there is no internet connection after running Combofix, then restart your computer to restore back your connection.
1. Double click on ComboFix.exe & follow the prompts.
2. Accept the disclaimer and allow to update if it asks
3. When finished, it shall produce a log for you.
Notes:
Do not mouse-click Combofix’s window while it is running. That may cause it to stall.
Do not “re-run” Combofix. If you have a problem, reply back for further instructions.
If after the reboot you get errors about programs being marked for deletion then reboot, that will cure it.
Please post all the logs here, so that I can get an idea on what’s going on. Also let me know how is your computer running.
Thanks you for your help! I used this method once successfully but the virus came back after about two months and my hitman pro has expired. I once again followed all steps hi up to that point. Any suggestions?
Hello,
Lets run the below scans:
Run a scan with RogueKiller
1. Please download the latest official version of RogueKiller.
RogueKiller Download Link : http://www.sur-la-toile.com/RogueKiller/RogueKiller.exe
2. Double click on RogueKiller.exe to start this utility and then wait for the Prescan to complete.This should take only a few seconds and then you can click the Scan button to perform a system scan.
3. After the scan has completed, press the Delete button to remove any malicious registry keys.
Run a scan with ESET Online Scanner
1.Download ESET Online Scanner utility.
ESET Online Scanner Download Link : http://download.eset.com/special/eos/esetsmartinstaller_enu.exe
2. Double click on the Eset installer program (esetsmartinstaller_enu.exe).
3.Check Yes, I accept the Terms of Use, then click the Start button.
4.Check Scan archives and push the Start button.
5. ESET will then download updates for itself, install itself, and begin scanning your computer. Please be patient as this can take some time.
6. When the scan completes, click on the Finish button.
Next, can you please run a scan with Combofix and post the logs here so that I can get an idea on what’s going on:
You can download ComboFix from here: http://download.bleepingcomputer.com/sUBs/ComboFix.exe
VERY IMPORTANT !!! Save as Combo-Fix.exe during the download.ComboFix must be renamed before you download to your Desktop
Close any open browsers.
Very Important!!!> Temporarily disable your anti-virus, script blocking and any anti-malware real-time protection before performing a scan. They can interfere with ComboFix or remove some of its embedded files which may cause “unpredictable results”.
WARNING: Combofix will disconnect your machine from the Internet as soon as it starts
Please do not attempt to re-connect your machine back to the Internet until Combofix has completely finished.
If there is no internet connection after running Combofix, then restart your computer to restore back your connection.
1. Double click on ComboFix.exe & follow the prompts.
2. Accept the disclaimer and allow to update if it asks
3. When finished, it shall produce a log for you.
Notes:
Do not mouse-click Combofix’s window while it is running. That may cause it to stall.
Do not “re-run” Combofix. If you have a problem, reply back for further instructions.
If after the reboot you get errors about programs being marked for deletion then reboot, that will cure it.
Please post all the logs here, so that I can get an idea on what’s going on. Also let me know how is your computer running.
wow man u just saved my day, i was about to pay someone to reboot my notebook, cause i have no mood and hability for that.
I recommend everyone to use ur services.
So ppl, go to his shop!