silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,176
Continue reading below:A phishing attack using a novel technique to steal credentials from American Express customers was recently found in an email inbox protected using Microsoft’s Office 365 Advanced Threat Protection (ATP) by Cofense Phishing Defense Center researchers.
The phishing campaign targeted both corporate and consumer cardholders with phishing emails full of grammatical errors but with a small but deadly twist: instead of using the regular hyperlink to the landing page trick, this one used the HTML element to hide the malicious URL from antispam solutions.
This allows the attackers to specify the base URL that should be used for all relative URLs within the phishing message, effectively splitting up the phishing landing page in two separate pieces. It also helps to hide it from the target since, on hover, the hyperlink will only show the end part of the malicious link, without the domain used to host the landing page.
The malicious mail "asks the would-be victim to verify his or her personal information 'Due to a recent system maintenance' and says that failure to comply would lead to a 'temporary suspension' of the account," says the Cofense report.
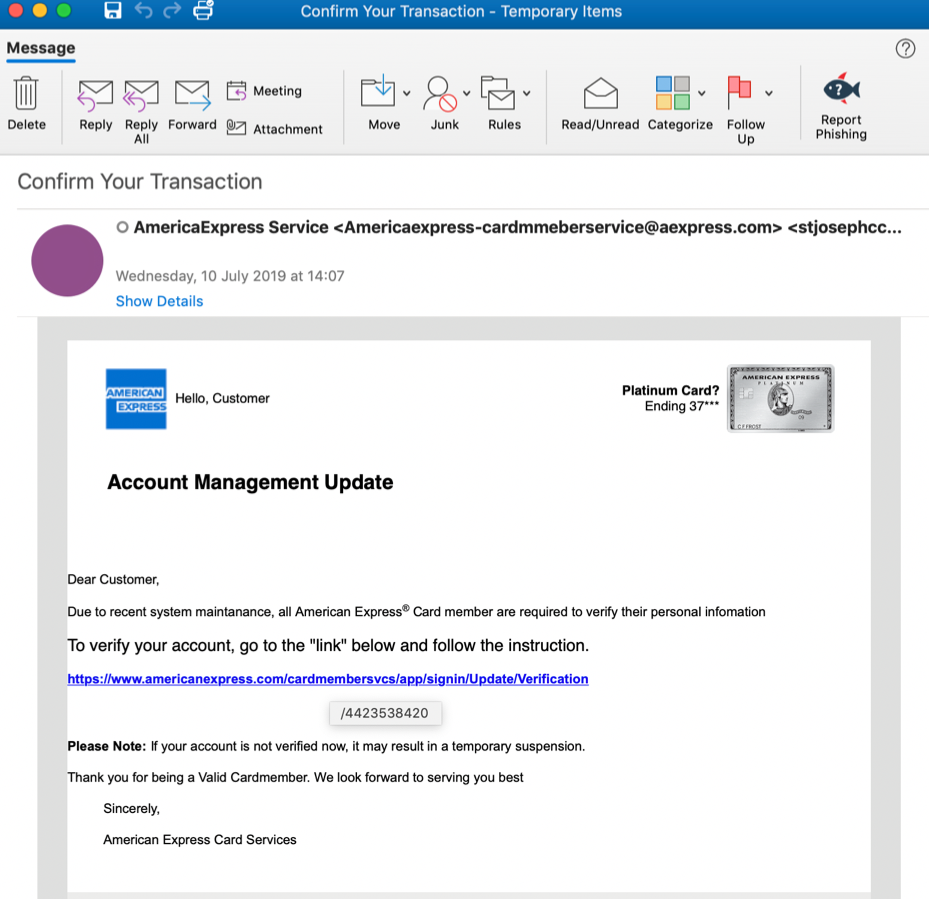
Phishing email
American Express Customers Targeted by Novel Phishing Attack
A phishing attack using a novel technique to steal credentials from American Express customers was recently found in an email inbox protected using Microsoft's Office 365 Advanced Threat Protection (ATP) by Cofense Phishing Defense Center researchers.
