One of the biggest challenges in threat intelligence is separating the hype from the hazard. We focus too much on complex, scary threats and too little on the dangerous ones - the simple, scalable techniques that work day in and day out.
The most sophisticated threat actors are actually focused on the simplicity of execution, rather than the complexity of their tools. By adhering to the old engineering KISS principle (Keep It Simple, Stupid), criminals maximize their return on investment. This is why tactics like Living-Off-The-Land and malware-free attacks are growing: they are simple, they scale, and they bypass defenses looking for complicated threats.
 businessinsights.bitdefender.com
businessinsights.bitdefender.com

The most sophisticated threat actors are actually focused on the simplicity of execution, rather than the complexity of their tools. By adhering to the old engineering KISS principle (Keep It Simple, Stupid), criminals maximize their return on investment. This is why tactics like Living-Off-The-Land and malware-free attacks are growing: they are simple, they scale, and they bypass defenses looking for complicated threats.
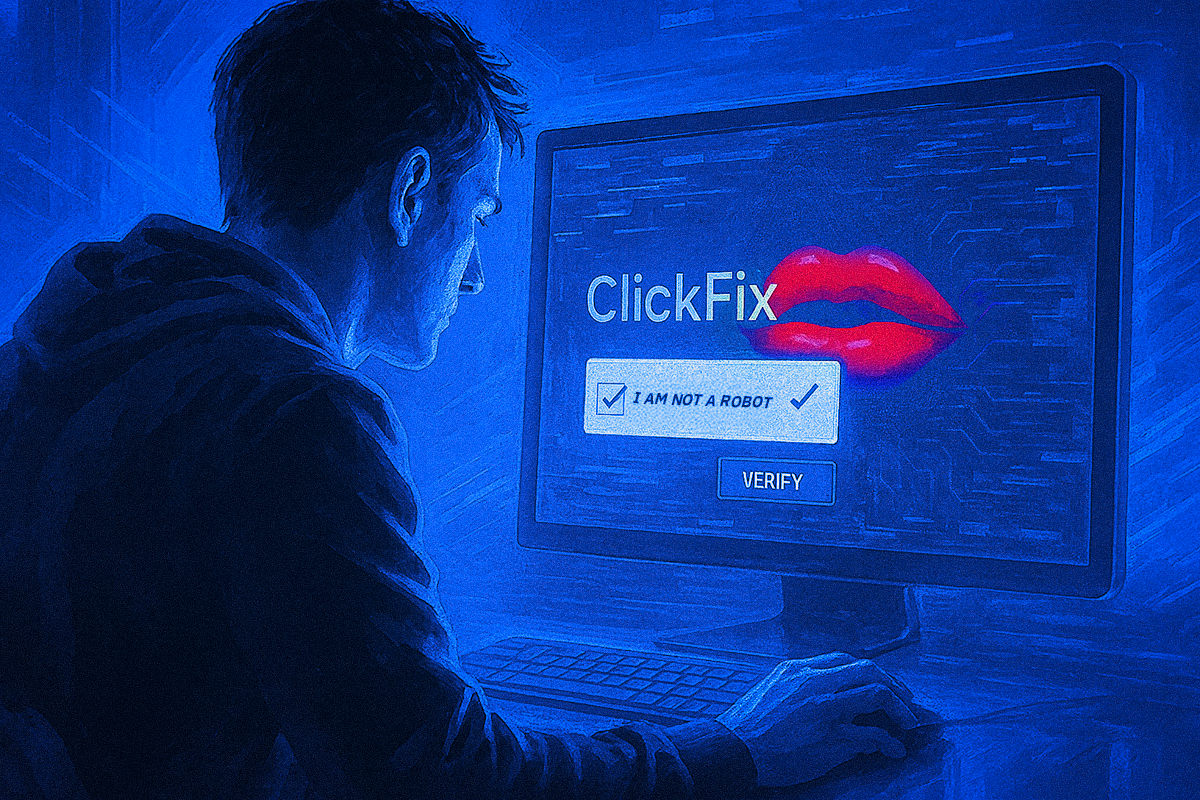
ClickFix: A KISS from Cybercriminals
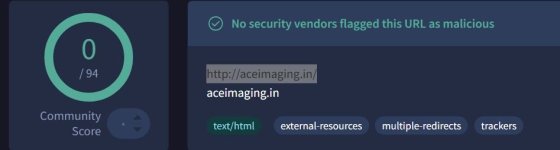
ClickFix is a social engineering technique that tricks users into running malicious commands by exploiting their impulse to solve minor technical issues.
Last edited: