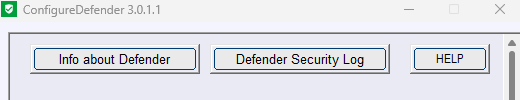
Configuredefender ver. 3.1.1.1
Installer:
Help (updated):
No need to update the installer (only a new certificate added, no functional changes).
Installer:
Help (updated):
No need to update the installer (only a new certificate added, no functional changes).