- Jan 24, 2011
- 9,378
A malicious email campaign that began over a week ago continues to distribute messages luring recipients into downloading a variant of the third version of CryptoWall ransomware.
Reported last week by experts from Cisco’s TALOS security intelligence and research group, the operation stands out through its multiple layers of obfuscation, in an attempt to evade detection.
Multiple redirections lead to Google Drive storage
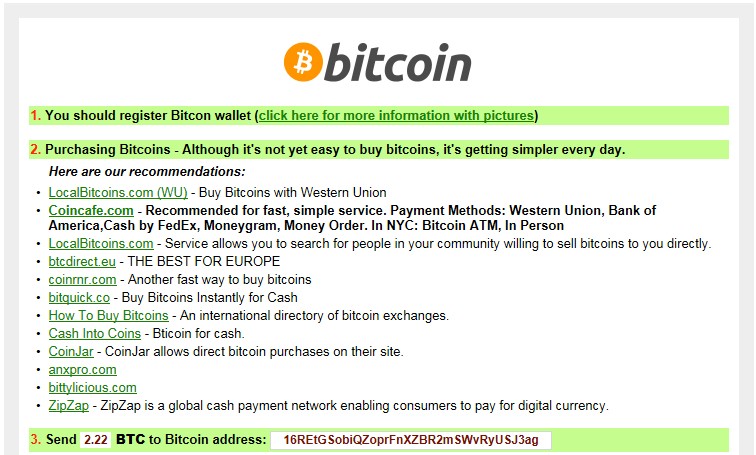
Brad Duncan from RackSpace also analyzed the nefarious emails last Thursday and found that they were sent from Yahoo addresses and tracked down the bitcoin address the cybercriminals set up to receive the ransom money from victims.
Analysis of new emails leading to the same crypto-malware shows that the operation is still active, as the same bitcoin address was identified and the modus operandi is the same.
The malicious message claims to be a reply to previous communication about possible employment. In the attachment, it has an archived HTML file, which contains an iFrame that redirects to a compromised WordPress site. The redirect chain continues to a Google Drive account, where another ZIP file is hosted, with CryptoWall inside.
Bitcoin balance remains unchanged
Despite this complicated process, the return on investment does not seem to fit the effort of the operator. The bitcoin address identified by Duncan shows that it was involved only in two transactions, the funds received being a little over 3 bitcoins (currently approximately $700 / €623), the same balance as last week.
Read more: http://news.softpedia.com/news/Cryp...ign-Started-More-Than-A-Week-Ago-484046.shtml