Further to the interest to Trend Micro after @Shadowra review, this post will be a deep dive into the TM components and protection model which may not be very well understood by everyone.
The components - these are updated on when-needed basis, independent of the programme version
Note: not all components are listed there, some components such as wrappers around the engine that should prevent Trend Micro from being exploited by malware writers, are not mentioned.
The model:
It uses minimalistic pattern file (40 MB) and is more similar to the signature-less products.
The local pattern determines files which are confirmed safe and suspicious (which will be subjected to check using the full malware pattern available on TM servers).
My guess is that these pattern files contain hashes/fuzzy hashes and heuristics, similarly to what Panda Cloud Antivirus uses for local protection.
According to the modules description above and what I will post below, Trend Micro reserves patterns (definitions) only for malware that actively causes damage. Once it no longer causes damage, it will be removed from the local pattern file as it has to stay small. This is one of the reasons that may be causing the high number of undetected samples on the AVC malware protection test, yet TM nails the real world protection. Files no longer causing damage will only be detected by Predictive Machine Learning once it’s been retained with these samples, behavioural blocking (eventually) and not by anything else (they will be a miss). Such files will most probably be bots, RATs and infostealers with dead C&Cs (ransomware can always cause damage).
Trend Micro frequently drops a lot of detections, for example the latest update drops 285.
Trend Micro uses Advanced Threat Scan Engine which is fully cloud-based to scan files without a good reputation.
ATSE can block malware and identify the malware family (which can make it look like it’s definitions-based).
Predictive Machine Learning uses the Advanced Threat Scan Engine (ATSE) to extract file features and sends the report to the Predictive Machine Learning engine on the Trend Micro Smart Protection Network. To enable Predictive Machine Learning, perform the following:
As with all detected malware, Predictive Machine Learning logs an event when it detects malware. (See About Deep Security event logging.) You can also create an exception for any false positives. (See Create anti-malware exceptions.)
Predictive Machine Learning
Trend Micro Predictive Machine Learning uses advanced machine learning technology to correlate threat information and perform in-depth file analysis to detect emerging unknown security risks through digital DNA fingerprinting, API mapping, and other file features. Predictive Machine Learning also performs a behavioral analysis on unknown or low-prevalence processes to determine if an emerging or unknown threat is attempting to infect your network.
Predictive Machine Learning is a powerful tool that helps protect your environment from unidentified threats and zero-day attacks.
After detecting an unknown or low-prevalence file, Deep Discovery Web Inspector scans the file using the Advanced Threat Scan Engine (ATSE) to extract file features and sends the report to the Predictive Machine Learning engine, hosted on the Trend Micro Smart Protection Network. Through use of malware modeling, Predictive Machine Learning compares the sample to the malware model, assigns a probability score, and determines the probable malware type that the file contains.
Depending on how you configure your policies, Deep Discovery Web Inspector can block the object to prevent the threat from continuing to spread across your network. Alternatively, you can configure the policy to monitor and log information about the object without blocking it.
https://docs.trendmicro.com/all/ent/ddwi/2.5/en-us/ddwi_2.5_olh/Predictive-Machine-L.html
P.S. We need a few more TM tests, any users willing to participate, apart from @Shadowra who can retest at one point?
The components - these are updated on when-needed basis, independent of the programme version
| Component | Distributed To | Description |
|---|---|---|
| Virus Scan Engine 32/64-bit | OfficeScan agents | At the heart of all Trend Micro products lies the scan engine, which was originally developed in response to early file-based viruses. The scan engine today is exceptionally sophisticated and capable of detecting different types of viruses and malware. The scan engine also detects controlled viruses that are developed and used for research. Rather than scanning every byte of every file, the engine and pattern file work together to identify the following:
|
| Smart Scan Pattern | Not distributed to OfficeScan agents. This pattern stays in theOfficeScan serverand is used when responding to scan queries received from OfficeScan agents. | When in smart scan mode, OfficeScan agents use two lightweight patterns that work together to provide the same protection provided by conventional anti-malware and anti-spyware patterns. The Smart Scan Pattern contains majority of the pattern definitions. The Smart Scan Agent Pattern contains all the other pattern definitions not found on the Smart Scan Pattern. The OfficeScan agent scans for security threats using the Smart Scan Agent Pattern. OfficeScan agents that cannot determine the risk of the file during the scan verify the risk by sending a scan query to the Scan Server, a service hosted on the OfficeScan server. The Scan Server verifies the risk using the Smart Scan Pattern. The OfficeScan agent "caches" the scan query result provided by the Scan Server to improve the scan performance. |
| Smart Scan Agent Pattern | OfficeScan agentsusing smart scan | |
| Virus Pattern | OfficeScan agentsusing conventional scan | The Virus Pattern contains information that helps OfficeScan agents identify the latest virus/malware and mixed threat attacks. Trend Micro creates and releases new versions of the Virus Pattern several times a week, and any time after the discovery of a particularly damaging virus/malware. |
| IntelliTrap Exception Pattern | OfficeScan agents | The IntelliTrap Exception Pattern contains a list of "approved" compression files. |
| IntelliTrap Pattern | OfficeScan agents | The IntelliTrap Pattern detects real-time compression files packed as executable files. For details, see IntelliTrap. |
| Memory Inspection Pattern | OfficeScan agents | This technology provides enhanced virus scanning for polymorphic and mutation viruses, and augments virus-pattern-based scans by emulating file execution. The results are then analyzed in a controlled environment for evidence of malicious intent with little impact on system performance. |
| Early Launch Anti-Malware Pattern 32/64-bit | OfficeScan agents | OfficeScan supports the Early Launch Anti-Malware (ELAM) feature as part of the Secure Boot standard to provide boot time protection on endpoints. This feature enables OfficeScan agents to detect malware during the operating system boot process. |
| Contextual Intelligence Engine 32/64-bit | OfficeScan agents | The Contextual Intelligence Engine monitors processes executed by low prevalence files and extracts behavioral features that the Contextual Intelligence Query Handler sends to the Predictive Machine Learning engine for analysis. |
| Contextual Intelligence Pattern | OfficeScan agents | The Contextual Intelligence Pattern contains a list of "approved" behaviors that are not relevant to any known threats. |
| Contextual Intelligence Query Handler 32/64-bit | OfficeScan agents | The Contextual Intelligence Query Handler processes the behaviors identified by the Contextual Intelligence Engine and sends the report to the Predictive Machine Learning engine. |
| Advanced Threat Scan Engine 32/64-bit | OfficeScan agents | The Advanced Threat Scan Engine extracts file features from low prevalence files and sends the the information to the Predictive Machine Learning engine. |
| Advanced Threat Correlation Pattern | OfficeScan agents | The Advanced Threat Correlation Pattern contains a list of file features that are not relevant to any known threats. |
Anti-spyware
| Component | Distributed To | Description |
|---|---|---|
| Spyware/Grayware Scan Engine 32/64-bit | OfficeScan agents | The Spyware/Grayware Scan Engine scans for and performs the appropriate scan action on spyware/grayware. |
| Spyware/Grayware Pattern | OfficeScan agents | The Spyware/Grayware Pattern identifies spyware/grayware in files and programs, modules in memory, Windows registry and URL shortcuts. |
| Spyware Active-monitoring Pattern | OfficeScan agentsusing conventional scan | The Spyware Active-monitoring Pattern is used for real-time spyware/grayware scanning. Only conventional scan agentsuse this pattern. |
Damage Cleanup Services
| Component | Distributed To | Description |
|---|---|---|
| Damage Cleanup Engine 32/64-bit | OfficeScan agents | The Damage Cleanup Engine scans for and removes Trojans and Trojan processes. |
| Damage Cleanup Template | OfficeScan agents | The Damage Cleanup Template is used by the Damage Cleanup Engine to identify Trojan files and processes so the engine can eliminate them. |
| Early Boot Cleanup Driver 32/64-bit | OfficeScan agents | The Trend Micro Early Boot Cleanup Driver loads before the operating system drivers which enables the detection and blocking of boot-type rootkits. After the OfficeScan agent loads, Trend Micro Early Boot Cleanup Driver calls Damage Cleanup Services to clean the rootkit. |
Web Reputation
| Component | Distributed To | Description |
|---|---|---|
| URL Filtering Engine | OfficeScan agents | The URL Filtering Engine facilitates communication between OfficeScan and the Trend Micro URL Filtering Service. The URL Filtering Service is a system that rates URLs and provides rating information to OfficeScan. |
Firewall
| Component | Distributed To | Description |
|---|---|---|
| Common Firewall Driver 32/64-bit | OfficeScan agents | The Common Firewall Driver is used with the Common Firewall Pattern to scan agentendpoints for network viruses. This driver supports 32-bit and 64-bit platforms. |
| Common Firewall Pattern | OfficeScan agents | Like the Virus Pattern, the Common Firewall Pattern helps agents identify virus signatures, unique patterns of bits and bytes that signal the presence of a network virus. |
Behavior Monitoring and Device Control
| Component | Distributed To | Description |
|---|---|---|
| Behavior Monitoring Detection Pattern 32/64-bit | OfficeScan agents | This pattern contains the rules for detecting suspicious threat behavior. |
| Behavior Monitoring Core Driver 32/64-bit | OfficeScan agents | This kernel mode driver monitors system events and passes them to the Behavior Monitoring Core Service for policy enforcement. |
| Behavior Monitoring Core Service 32/64-bit | OfficeScan agents | This user mode service has the following functions:
|
| Behavior Monitoring Configuration Pattern | OfficeScan agents | The Behavior Monitoring Driver uses this pattern to identify normal system events and exclude them from policy enforcement. |
| Policy Enforcement Pattern | OfficeScan agents | The Behavior Monitoring Core Service checks system events against the policies in this pattern. |
| Digital Signature Pattern | OfficeScan agents | This pattern contains a list of valid digital signatures that are used by the Behavior Monitoring Core Service to determine whether a program responsible for a system event is safe. |
| Memory Scan Trigger Pattern (32/64-bit) | OfficeScan agents | The Memory Scan Trigger service executes other scan engines when it detects the process in memory is unpacked. |
| Program Inspection Monitoring Pattern | OfficeScan agents | The Program Inspection Monitoring Pattern monitors and stores inspection points that are used for Behavior Monitoring. |
| Damage Recovery Pattern | OfficeScan agents | The Damage Recovery Pattern contains policies that are used for monitoring suspicious threat behavior. |
Browser Exploits
| Component | Distributed To | Description |
|---|---|---|
| Browser Exploit Prevention Pattern | OfficeScan agents | This pattern identifies the latest web browser exploits and prevents the exploits from being used to compromise the web browser. |
| Script Analyzer Unified Pattern | OfficeScan agents | This pattern analyzes script in web |
The model:
It uses minimalistic pattern file (40 MB) and is more similar to the signature-less products.
The local pattern determines files which are confirmed safe and suspicious (which will be subjected to check using the full malware pattern available on TM servers).
My guess is that these pattern files contain hashes/fuzzy hashes and heuristics, similarly to what Panda Cloud Antivirus uses for local protection.
The Trend Micro Pattern Files and Scan Engine
All Trend Micro products, including CPM, can be configured to automatically check the Trend Micro ActiveUpdate (TMAU) server, then download and install updates when found. This process is typically ...
help.hcltechsw.com
This makes it look like the pattern only contains damaging (active) malware.
Conventional Scan The Virus Pattern contains information that helps Core Protection Module identify the latest virus/malware and mixed threat attacks. Trend Micro creates and releases new versions of the Virus Pattern several times a week, and any time after the discovery of a particularly damaging virus/malware.
Trend Micro recommends scheduling automatic updates at least hourly, which is the default setting for all shipped products.
According to the modules description above and what I will post below, Trend Micro reserves patterns (definitions) only for malware that actively causes damage. Once it no longer causes damage, it will be removed from the local pattern file as it has to stay small. This is one of the reasons that may be causing the high number of undetected samples on the AVC malware protection test, yet TM nails the real world protection. Files no longer causing damage will only be detected by Predictive Machine Learning once it’s been retained with these samples, behavioural blocking (eventually) and not by anything else (they will be a miss). Such files will most probably be bots, RATs and infostealers with dead C&Cs (ransomware can always cause damage).
Trend Micro frequently drops a lot of detections, for example the latest update drops 285.
Adware.Win32.MULTIPLUG.USBLCF24
Backdoor.Linux.MIRAI.USBLCG24
Backdoor.MSIL.ASYNCRAT.USBLCF24
Backdoor.MSIL.BLADABINDI.USBLCF24
Backdoor.Win32.CERBER.USBLCE24
Backdoor.Win32.DOINA.USBLCF24
Backdoor.Win32.GEPYS.USBLCL24
Backdoor.Win32.HAVOC.USBLCI24
Backdoor.Win32.IRCBOT.USBLCE24
Backdoor.Win32.KRYPTIK.USBLCL24
Backdoor.Win32.PINCAV.USBLCE24
Backdoor.Win32.QUKART.USBLCF24
Backdoor.Win32.RAMMSTN.USBLCE24
Backdoor.Win32.SCAR.USBLCF24
Backdoor.Win32.SHIZ.USBLCF24
Backdoor.Win32.SNOJAN.USBLCE24
Backdoor.Win32.SWRORT.YXECPZ
Backdoor.Win32.TINY.USBLCF24
Backdoor.Win32.WARZONE.YXECPZ
Backdoor.Win32.XWORM.YXECPZ
Backdoor.Win64.ASYNCRAT.YXECPZ
Backdoor.Win64.BLADABINDI.USBLCH24
Backdoor.Win64.COBEACON.YXECOZ
Backdoor.Win64.SILVER.YXECOZ
Ransom.Win32.BARYS.USBLCE24
Ransom.Win32.JUICYPOTATO.USBLCE24
Ransom.Win32.QQPASS.USBLCF24
Ransom.Win32.SELFMOD.USBLCF24
Ransom.Win32.STAPCORE.USBLCM24
Ransom_Blocker.R06CC0CCL24
Ransom_Blocker.R06CC0DCF24
Ransom_Cerber.R002C0DCE24
Ransom_Cobra.R002C0DCE24
Ransom_ContiCrypt.R002C0CCE24
Ransom_ContiCrypt.R002C0CCF24
Ransom_ContiCrypt.R002C0DCE24
Ransom_CryFile.R002C0DCF24
Ransom_Cryptodef.R002C0DCF24
Ransom_Cryptodef.R03BC0DCM24
Ransom_Crysis.R002C0DCE24
Ransom_Fasem.R06CC0OCE24
Ransom_Foreign.R002C0GCE24
Ransom_GandCrab.R002C0DCF24
Ransom_Gen.R002C0XCK24
Ransom_Gen.R03BC0XCK24
Ransom_GenericCryptor.R002C0CCF24
Ransom_GenericCryptor.R002C0CCL24
Ransom_GenericCryptor.R002C0DCM24
Ransom_GenericCryptor.R023C0CCE24
Ransom_Petya.R002C0DCE24
Ransom_Phny.R002C0DCE24
Ransom_PolyRansom.R023C0GCE24
Ransom_PolyRansom.R023C0XCE24
Ransom_PornoAsset.R002C0CCF24
Ransom_PornoAsset.R002C0DCF24
Ransom_PornoAsset.R03BC0DCM24
Ransom_PornoAsset.R049C0DCE24
Ransom_Rakhni.R002C0PCE24
Ransom_Rantest.R06CC0CCE24
Ransom_Samas.R06CC0DCE24
Ransom_StopCrypt.R002C0DCL24
TROJ_GEN.R011C0CCF24
TROJ_GEN.R011C0GCF24
TROJ_GEN.R011C0WCK24
TROJ_GEN.R011H0CKG23
TROJ_GEN.R023C0OCL24
TROJ_GEN.R023C0WCL24
TROJ_GEN.R03BC0GCL24
TROJ_GEN.R03BC0WCV24
TROJ_GEN.R03FC0CCM24
TROJ_GEN.R049C0CCE24
TROJ_GEN.R049C0DCK24
TROJ_GEN.R049C0DCL24
TROJ_GEN.R049C0OCE24
TROJ_GEN.R049C0RCE24
TROJ_GEN.R049C0WCE24
TROJ_GEN.R053C0OCM24
TROJ_GEN.R06BC0XCL24
TROJ_GEN.R06CC0GCE24
TROJ_GEN.R06CC0WCL24
TROJ_GEN.R06FC0DCF24
Trojan.HTML.XWORM.YXECNZ
Trojan.JS.ASYNCRAT.YXECOZ
Trojan.JS.SOCGHOLISH.YXECOZ
Trojan.Linux.CVE.USBLCG24
Trojan.MSIL.BLADABINDI.USBLCF24
Trojan.MSIL.DCRAT.USBLCF24
Trojan.MSIL.DNOPER.USBLCE24
Trojan.MSIL.DNOPER.USBLCF24
Trojan.MSIL.INJECTOR.USBLCF24
Trojan.MSIL.KRYPTIK.USBLCE24
Trojan.MSIL.MSILKRYPT.USBLCF24
Trojan.MSIL.POWERSHELL.USBLCE24
Trojan.MSIL.REDLINE.USBLCK24
Trojan.MSIL.REDLINE.USBLCO24
Trojan.MSIL.REDLINE.USBLCU24
Trojan.MSIL.ROZENA.USBLCE24
Trojan.MSIL.ROZENA.USBLCG24
Trojan.MSIL.SONBOKLI.USBLCG24
Trojan.MSIL.XMRIG.USBLCM24
Trojan.MSIL.XMRIG.USBLCN24
Trojan.MSIL.ZEGOST.USBLCJ24
Trojan.MSIL.ZNYONM.USBLCE24
Trojan.VBS.DARKGATE.YXECOZ
Trojan.W97M.CVE.USBLCE24
Trojan.W97M.OBFUS.USBLCE24
Trojan.Win32.AGENTSMALL.USBLCE24
Trojan.Win32.AGENTSMALL.USBLCF24
Trojan.Win32.ANDROM.USBLCL24
Trojan.Win32.AUTOIT.USBLCE24
Trojan.Win32.AUTOITGENOME.USBLCE24
Trojan.Win32.AUTOITINJECT.USBLCE24
Trojan.Win32.AUTORUN.USBLCE24
Trojan.Win32.AUTORUN.USBLCJ24
Trojan.Win32.AZORULT.USBLCP24
Trojan.Win32.BANLOAD.USBLCM24
Trojan.Win32.BARYS.USBLCM24
Trojan.Win32.BLACKMOON.USBLCF24
Trojan.Win32.BLACKMOON.USBLCL24
Trojan.Win32.BLIHAN.USBLCF24
Trojan.Win32.BLOCKER.USBLCF24
Trojan.Win32.CAYNAMER.USBLCF24
Trojan.Win32.CERBER.USBLCM24
Trojan.Win32.CODBOT.USBLCF24
Trojan.Win32.COMETER.USBLCE24
Trojan.Win32.CONVAGENT.USBLCI24
Trojan.Win32.COREWARRIOR.USBLCF24
Trojan.Win32.COREWARRIOR.USBLCL24
Trojan.Win32.CRYPT.USBLCJ24
Trojan.Win32.CYNS.USBLCF24
Trojan.Win32.DACIC.USBLCL24
Trojan.Win32.DANABOT.YXECOZ
Trojan.Win32.DAWS.USBLCF24
Trojan.Win32.DELF.USBLCF24
Trojan.Win32.DIBIK.USBLCE24
Trojan.Win32.DINWOD.USBLCL24
Trojan.Win32.DISCO.USBLCF24
Trojan.Win32.DISIN.USBLCF24
Trojan.Win32.DISIN.USBLCG24
Trojan.Win32.DISKWRITER.USBLCF24
Trojan.Win32.DISS.USBLCE24
Trojan.Win32.DORIFEL.USBLCF24
Trojan.Win32.DROLNUX.USBLCE24
Trojan.Win32.DROPPER.USBLCF24
Trojan.Win32.EKSTAK.USBLCK24
Trojan.Win32.EMDUP.USBLCM24
Trojan.Win32.ESTIWIR.USBLCE24
Trojan.Win32.FAKEALERT.USBLCE24
Trojan.Win32.FAKEALERT.USBLCF24
Trojan.Win32.FARFLI.USBLCF24
Trojan.Win32.FERO.USBLCF24
Trojan.Win32.FILEINFECTOR.USBLCL24
Trojan.Win32.FLYSTUD.USBLCE24
Trojan.Win32.FORMBOOK.YXECOZ
Trojan.Win32.GAMARUE.USBLCF24
Trojan.Win32.GAMUP.USBLCF24
Trojan.Win32.GANELP.USBLCF24
Trojan.Win32.GCLEANER.USBLCG24
Trojan.Win32.GCLEANER.YXECOZ
Trojan.Win32.GENERICKD.USBLCE24
Trojan.Win32.GENKRYPTIK.USBLCF24
Trojan.Win32.GUPBOOT.USBLCF24
Trojan.Win32.HUPIGON.USBLCF24
Trojan.Win32.INJECT.USBLCF24
Trojan.Win32.INJECTS.USBLCE24
Trojan.Win32.INJECTS.USBLCF24
Trojan.Win32.IPAMOR.USBLCF24
Trojan.Win32.IRCBRUTE.USBLCE24
Trojan.Win32.IRCFLOOD.USBLCF24
Trojan.Win32.IYECLORE.USBLCF24
Trojan.Win32.JAIK.USBLCF24
Trojan.Win32.JUCHED.USBLCE24
Trojan.Win32.KHALESI.USBLCF24
Trojan.Win32.KOCEG.USBLCF24
Trojan.Win32.KRAP.USBLCF24
Trojan.Win32.LAMER.USBLCF24
Trojan.Win32.LDPINCH.USBLCE24
Trojan.Win32.LDPINCH.USBLCF24
Trojan.Win32.LINEAGE.USBLCE24
Trojan.Win32.LOAN.USBLCF24
Trojan.Win32.LOAN.USBLCL24
Trojan.Win32.LUNA.USBLCF24
Trojan.Win32.MAGANIA.USBLCF24
Trojan.Win32.MANSABO.USBLCE24
Trojan.Win32.MEKOTIO.USBLCI24
Trojan.Win32.METASPLOIT.USBLCF24
Trojan.Win32.MIRA.USBLCL24
Trojan.Win32.MULDROP.USBLCM24
Trojan.Win32.MULTIPLUG.USBLCF24
Trojan.Win32.MYDOOM.USBLCF24
Trojan.Win32.NEMUCOD.USBLCF24
Trojan.Win32.NEMUCOD.USBLCM24
Trojan.Win32.NESHTA.USBLCE24
Trojan.Win32.NEVEREG.USBLCF24
Trojan.Win32.NEWDOTNET.USBLCG24
Trojan.Win32.NITOL.USBLCM24
Trojan.Win32.NOOBYPROTECT.USBLCK24
Trojan.Win32.OBFUS.USBLCF24
Trojan.Win32.OPERALOADER.YXECOZ
Trojan.Win32.PARIHAM.USBLCF24
Trojan.Win32.PCCLIENT.USBLCF24
Trojan.Win32.PIKABOT.YXECRZ
Trojan.Win32.PIKABOT.YXECZZ
Trojan.Win32.PISTOLAR.USBLCF24
Trojan.Win32.PLITE.USBLCL24
Trojan.Win32.POWERSHELL.USBLCF24
Trojan.Win32.PROTUX.USBLCF24
Trojan.Win32.PURORA.USBLCE24
Trojan.Win32.PYTR.USBLCE24
Trojan.Win32.QQPASS.USBLCF24
Trojan.Win32.QUKART.USBLCM24
Trojan.Win32.RACCOON.USBLCF24
Trojan.Win32.REMCOS.USBLCF24
Trojan.Win32.REMHEAD.USBLCF24
Trojan.Win32.REVERSESHELL.USBLCG24
Trojan.Win32.SAKUREL.USBLCF24
Trojan.Win32.SCAR.USBLCG24
Trojan.Win32.SFONE.USBLCF24
Trojan.Win32.SILENTCRYPTOMINER.USBLCE24
Trojan.Win32.SMOKELOADER.USBLCE24
Trojan.Win32.SOUL.USBLCE24
Trojan.Win32.STAPCORE.USBLCG24
Trojan.Win32.STAPCORE.USBLCI24
Trojan.Win32.STEALC.USBLCK24
Trojan.Win32.SYSTEMBC.USBLCF24
Trojan.Win32.TINBA.USBLCF24
Trojan.Win32.TINY.USBLCF24
Trojan.Win32.TRICKBOT.USBLCG24
Trojan.Win32.UNRUY.USBLCF24
Trojan.Win32.UPATRE.USBLCM24
Trojan.Win32.URELAS.USBLCI24
Trojan.Win32.VILSEL.USBLCF24
Trojan.Win32.VMPROTECT.USBLCO24
Trojan.Win32.VUNDO.USBLCF24
Trojan.Win32.WAJAM.USBLCF24
Trojan.Win32.XPACK.USBLCF24
Trojan.Win32.ZAPCHAST.USBLCE24
Trojan.Win32.ZLOAD.USBLCE24
Trojan.Win32.ZLOADER.USBLCE24
Trojan.Win32.ZLOB.USBLCL24
Trojan.Win32.ZOMBIE.USBLCM24
Trojan.Win64.BUMBLELOADER.YXECOZ
Trojan.Win64.DCRAT.USBLCF24
Trojan.Win64.GENKRYPTIK.USBLCF24
Trojan.Win64.INJEXA.USBLCF24
Trojan.Win64.LAZY.USBLCF24
Trojan.Win64.LUNA.USBLCF24
Trojan.Win64.LUNA.USBLCH24
Trojan.Win64.LUNALOGGER.USBLCK24
Trojan.Win64.OPERALOADER.YXECOZ
Trojan.Win64.ROZENA.USBLCE24
Trojan.Win64.SPYLOADER.USBLCK24
Trojan.Win64.STEALER.USBLCF24
Trojan.Win64.STEALER.USBLCG24
Trojan.Win64.STEALER.USBLCH24
Trojan.Win64.STEALER.USBLCI24
Trojan.Win64.STEALER.USBLCO24
Trojan.Win64.STRELA.USBLCE24
Trojan.Win64.STRELA.USBLCF24
Trojan.Win64.STRELA.USBLCH24
Trojan.Win64.STRELA.USBLCI24
Trojan.Win64.STRELASTEALER.USBLCJ24
Trojan.Win64.STRELASTEALER.USBLCK24
Trojan.X97M.CVE.USBLCE24
Trojan.X97M.CVE.USBLCF24
TrojanSpy.MSIL.KRYPTIK.USBLCE24
TrojanSpy.MSIL.STEALERC.USBLCE24
TrojanSpy.Win32.CARDSPY.USBLCF24
TrojanSpy.Win32.FASONG.USBLCG24
TrojanSpy.Win32.QUKART.USBLCF24
TrojanSpy.Win32.REDLINE.USBLCF24
TrojanSpy.Win32.SNOJAN.USBLCE24
TrojanSpy.Win32.STEALC.USBLCM24
TrojanSpy.Win32.URSNIF.YXECOZ
TrojanSpy.Win32.ZPEVDO.USBLCF24
TrojanSpy.Win64.EXPIRO.USBLCE24
TrojanSpy.Win64.REDLINE.YXECOZ
TrojanSpy.Win64.STEALER.USBLCG24
TrojanSpy.Win64.STEALER.USBLCI24
Worm.Win32.DELF.USBLCF24
Worm.Win32.KOCEG.USBLCF24
Worm.Win32.LUDBARUMA.USBLCF24
Worm.Win32.RAMNIT.USBLCG24
Worm.Win32.SILENTALL.USBLCE24
Worm.Win32.VMPROTECT.USBLCG24
Backdoor.Linux.MIRAI.USBLCG24
Backdoor.MSIL.ASYNCRAT.USBLCF24
Backdoor.MSIL.BLADABINDI.USBLCF24
Backdoor.Win32.CERBER.USBLCE24
Backdoor.Win32.DOINA.USBLCF24
Backdoor.Win32.GEPYS.USBLCL24
Backdoor.Win32.HAVOC.USBLCI24
Backdoor.Win32.IRCBOT.USBLCE24
Backdoor.Win32.KRYPTIK.USBLCL24
Backdoor.Win32.PINCAV.USBLCE24
Backdoor.Win32.QUKART.USBLCF24
Backdoor.Win32.RAMMSTN.USBLCE24
Backdoor.Win32.SCAR.USBLCF24
Backdoor.Win32.SHIZ.USBLCF24
Backdoor.Win32.SNOJAN.USBLCE24
Backdoor.Win32.SWRORT.YXECPZ
Backdoor.Win32.TINY.USBLCF24
Backdoor.Win32.WARZONE.YXECPZ
Backdoor.Win32.XWORM.YXECPZ
Backdoor.Win64.ASYNCRAT.YXECPZ
Backdoor.Win64.BLADABINDI.USBLCH24
Backdoor.Win64.COBEACON.YXECOZ
Backdoor.Win64.SILVER.YXECOZ
Ransom.Win32.BARYS.USBLCE24
Ransom.Win32.JUICYPOTATO.USBLCE24
Ransom.Win32.QQPASS.USBLCF24
Ransom.Win32.SELFMOD.USBLCF24
Ransom.Win32.STAPCORE.USBLCM24
Ransom_Blocker.R06CC0CCL24
Ransom_Blocker.R06CC0DCF24
Ransom_Cerber.R002C0DCE24
Ransom_Cobra.R002C0DCE24
Ransom_ContiCrypt.R002C0CCE24
Ransom_ContiCrypt.R002C0CCF24
Ransom_ContiCrypt.R002C0DCE24
Ransom_CryFile.R002C0DCF24
Ransom_Cryptodef.R002C0DCF24
Ransom_Cryptodef.R03BC0DCM24
Ransom_Crysis.R002C0DCE24
Ransom_Fasem.R06CC0OCE24
Ransom_Foreign.R002C0GCE24
Ransom_GandCrab.R002C0DCF24
Ransom_Gen.R002C0XCK24
Ransom_Gen.R03BC0XCK24
Ransom_GenericCryptor.R002C0CCF24
Ransom_GenericCryptor.R002C0CCL24
Ransom_GenericCryptor.R002C0DCM24
Ransom_GenericCryptor.R023C0CCE24
Ransom_Petya.R002C0DCE24
Ransom_Phny.R002C0DCE24
Ransom_PolyRansom.R023C0GCE24
Ransom_PolyRansom.R023C0XCE24
Ransom_PornoAsset.R002C0CCF24
Ransom_PornoAsset.R002C0DCF24
Ransom_PornoAsset.R03BC0DCM24
Ransom_PornoAsset.R049C0DCE24
Ransom_Rakhni.R002C0PCE24
Ransom_Rantest.R06CC0CCE24
Ransom_Samas.R06CC0DCE24
Ransom_StopCrypt.R002C0DCL24
TROJ_GEN.R011C0CCF24
TROJ_GEN.R011C0GCF24
TROJ_GEN.R011C0WCK24
TROJ_GEN.R011H0CKG23
TROJ_GEN.R023C0OCL24
TROJ_GEN.R023C0WCL24
TROJ_GEN.R03BC0GCL24
TROJ_GEN.R03BC0WCV24
TROJ_GEN.R03FC0CCM24
TROJ_GEN.R049C0CCE24
TROJ_GEN.R049C0DCK24
TROJ_GEN.R049C0DCL24
TROJ_GEN.R049C0OCE24
TROJ_GEN.R049C0RCE24
TROJ_GEN.R049C0WCE24
TROJ_GEN.R053C0OCM24
TROJ_GEN.R06BC0XCL24
TROJ_GEN.R06CC0GCE24
TROJ_GEN.R06CC0WCL24
TROJ_GEN.R06FC0DCF24
Trojan.HTML.XWORM.YXECNZ
Trojan.JS.ASYNCRAT.YXECOZ
Trojan.JS.SOCGHOLISH.YXECOZ
Trojan.Linux.CVE.USBLCG24
Trojan.MSIL.BLADABINDI.USBLCF24
Trojan.MSIL.DCRAT.USBLCF24
Trojan.MSIL.DNOPER.USBLCE24
Trojan.MSIL.DNOPER.USBLCF24
Trojan.MSIL.INJECTOR.USBLCF24
Trojan.MSIL.KRYPTIK.USBLCE24
Trojan.MSIL.MSILKRYPT.USBLCF24
Trojan.MSIL.POWERSHELL.USBLCE24
Trojan.MSIL.REDLINE.USBLCK24
Trojan.MSIL.REDLINE.USBLCO24
Trojan.MSIL.REDLINE.USBLCU24
Trojan.MSIL.ROZENA.USBLCE24
Trojan.MSIL.ROZENA.USBLCG24
Trojan.MSIL.SONBOKLI.USBLCG24
Trojan.MSIL.XMRIG.USBLCM24
Trojan.MSIL.XMRIG.USBLCN24
Trojan.MSIL.ZEGOST.USBLCJ24
Trojan.MSIL.ZNYONM.USBLCE24
Trojan.VBS.DARKGATE.YXECOZ
Trojan.W97M.CVE.USBLCE24
Trojan.W97M.OBFUS.USBLCE24
Trojan.Win32.AGENTSMALL.USBLCE24
Trojan.Win32.AGENTSMALL.USBLCF24
Trojan.Win32.ANDROM.USBLCL24
Trojan.Win32.AUTOIT.USBLCE24
Trojan.Win32.AUTOITGENOME.USBLCE24
Trojan.Win32.AUTOITINJECT.USBLCE24
Trojan.Win32.AUTORUN.USBLCE24
Trojan.Win32.AUTORUN.USBLCJ24
Trojan.Win32.AZORULT.USBLCP24
Trojan.Win32.BANLOAD.USBLCM24
Trojan.Win32.BARYS.USBLCM24
Trojan.Win32.BLACKMOON.USBLCF24
Trojan.Win32.BLACKMOON.USBLCL24
Trojan.Win32.BLIHAN.USBLCF24
Trojan.Win32.BLOCKER.USBLCF24
Trojan.Win32.CAYNAMER.USBLCF24
Trojan.Win32.CERBER.USBLCM24
Trojan.Win32.CODBOT.USBLCF24
Trojan.Win32.COMETER.USBLCE24
Trojan.Win32.CONVAGENT.USBLCI24
Trojan.Win32.COREWARRIOR.USBLCF24
Trojan.Win32.COREWARRIOR.USBLCL24
Trojan.Win32.CRYPT.USBLCJ24
Trojan.Win32.CYNS.USBLCF24
Trojan.Win32.DACIC.USBLCL24
Trojan.Win32.DANABOT.YXECOZ
Trojan.Win32.DAWS.USBLCF24
Trojan.Win32.DELF.USBLCF24
Trojan.Win32.DIBIK.USBLCE24
Trojan.Win32.DINWOD.USBLCL24
Trojan.Win32.DISCO.USBLCF24
Trojan.Win32.DISIN.USBLCF24
Trojan.Win32.DISIN.USBLCG24
Trojan.Win32.DISKWRITER.USBLCF24
Trojan.Win32.DISS.USBLCE24
Trojan.Win32.DORIFEL.USBLCF24
Trojan.Win32.DROLNUX.USBLCE24
Trojan.Win32.DROPPER.USBLCF24
Trojan.Win32.EKSTAK.USBLCK24
Trojan.Win32.EMDUP.USBLCM24
Trojan.Win32.ESTIWIR.USBLCE24
Trojan.Win32.FAKEALERT.USBLCE24
Trojan.Win32.FAKEALERT.USBLCF24
Trojan.Win32.FARFLI.USBLCF24
Trojan.Win32.FERO.USBLCF24
Trojan.Win32.FILEINFECTOR.USBLCL24
Trojan.Win32.FLYSTUD.USBLCE24
Trojan.Win32.FORMBOOK.YXECOZ
Trojan.Win32.GAMARUE.USBLCF24
Trojan.Win32.GAMUP.USBLCF24
Trojan.Win32.GANELP.USBLCF24
Trojan.Win32.GCLEANER.USBLCG24
Trojan.Win32.GCLEANER.YXECOZ
Trojan.Win32.GENERICKD.USBLCE24
Trojan.Win32.GENKRYPTIK.USBLCF24
Trojan.Win32.GUPBOOT.USBLCF24
Trojan.Win32.HUPIGON.USBLCF24
Trojan.Win32.INJECT.USBLCF24
Trojan.Win32.INJECTS.USBLCE24
Trojan.Win32.INJECTS.USBLCF24
Trojan.Win32.IPAMOR.USBLCF24
Trojan.Win32.IRCBRUTE.USBLCE24
Trojan.Win32.IRCFLOOD.USBLCF24
Trojan.Win32.IYECLORE.USBLCF24
Trojan.Win32.JAIK.USBLCF24
Trojan.Win32.JUCHED.USBLCE24
Trojan.Win32.KHALESI.USBLCF24
Trojan.Win32.KOCEG.USBLCF24
Trojan.Win32.KRAP.USBLCF24
Trojan.Win32.LAMER.USBLCF24
Trojan.Win32.LDPINCH.USBLCE24
Trojan.Win32.LDPINCH.USBLCF24
Trojan.Win32.LINEAGE.USBLCE24
Trojan.Win32.LOAN.USBLCF24
Trojan.Win32.LOAN.USBLCL24
Trojan.Win32.LUNA.USBLCF24
Trojan.Win32.MAGANIA.USBLCF24
Trojan.Win32.MANSABO.USBLCE24
Trojan.Win32.MEKOTIO.USBLCI24
Trojan.Win32.METASPLOIT.USBLCF24
Trojan.Win32.MIRA.USBLCL24
Trojan.Win32.MULDROP.USBLCM24
Trojan.Win32.MULTIPLUG.USBLCF24
Trojan.Win32.MYDOOM.USBLCF24
Trojan.Win32.NEMUCOD.USBLCF24
Trojan.Win32.NEMUCOD.USBLCM24
Trojan.Win32.NESHTA.USBLCE24
Trojan.Win32.NEVEREG.USBLCF24
Trojan.Win32.NEWDOTNET.USBLCG24
Trojan.Win32.NITOL.USBLCM24
Trojan.Win32.NOOBYPROTECT.USBLCK24
Trojan.Win32.OBFUS.USBLCF24
Trojan.Win32.OPERALOADER.YXECOZ
Trojan.Win32.PARIHAM.USBLCF24
Trojan.Win32.PCCLIENT.USBLCF24
Trojan.Win32.PIKABOT.YXECRZ
Trojan.Win32.PIKABOT.YXECZZ
Trojan.Win32.PISTOLAR.USBLCF24
Trojan.Win32.PLITE.USBLCL24
Trojan.Win32.POWERSHELL.USBLCF24
Trojan.Win32.PROTUX.USBLCF24
Trojan.Win32.PURORA.USBLCE24
Trojan.Win32.PYTR.USBLCE24
Trojan.Win32.QQPASS.USBLCF24
Trojan.Win32.QUKART.USBLCM24
Trojan.Win32.RACCOON.USBLCF24
Trojan.Win32.REMCOS.USBLCF24
Trojan.Win32.REMHEAD.USBLCF24
Trojan.Win32.REVERSESHELL.USBLCG24
Trojan.Win32.SAKUREL.USBLCF24
Trojan.Win32.SCAR.USBLCG24
Trojan.Win32.SFONE.USBLCF24
Trojan.Win32.SILENTCRYPTOMINER.USBLCE24
Trojan.Win32.SMOKELOADER.USBLCE24
Trojan.Win32.SOUL.USBLCE24
Trojan.Win32.STAPCORE.USBLCG24
Trojan.Win32.STAPCORE.USBLCI24
Trojan.Win32.STEALC.USBLCK24
Trojan.Win32.SYSTEMBC.USBLCF24
Trojan.Win32.TINBA.USBLCF24
Trojan.Win32.TINY.USBLCF24
Trojan.Win32.TRICKBOT.USBLCG24
Trojan.Win32.UNRUY.USBLCF24
Trojan.Win32.UPATRE.USBLCM24
Trojan.Win32.URELAS.USBLCI24
Trojan.Win32.VILSEL.USBLCF24
Trojan.Win32.VMPROTECT.USBLCO24
Trojan.Win32.VUNDO.USBLCF24
Trojan.Win32.WAJAM.USBLCF24
Trojan.Win32.XPACK.USBLCF24
Trojan.Win32.ZAPCHAST.USBLCE24
Trojan.Win32.ZLOAD.USBLCE24
Trojan.Win32.ZLOADER.USBLCE24
Trojan.Win32.ZLOB.USBLCL24
Trojan.Win32.ZOMBIE.USBLCM24
Trojan.Win64.BUMBLELOADER.YXECOZ
Trojan.Win64.DCRAT.USBLCF24
Trojan.Win64.GENKRYPTIK.USBLCF24
Trojan.Win64.INJEXA.USBLCF24
Trojan.Win64.LAZY.USBLCF24
Trojan.Win64.LUNA.USBLCF24
Trojan.Win64.LUNA.USBLCH24
Trojan.Win64.LUNALOGGER.USBLCK24
Trojan.Win64.OPERALOADER.YXECOZ
Trojan.Win64.ROZENA.USBLCE24
Trojan.Win64.SPYLOADER.USBLCK24
Trojan.Win64.STEALER.USBLCF24
Trojan.Win64.STEALER.USBLCG24
Trojan.Win64.STEALER.USBLCH24
Trojan.Win64.STEALER.USBLCI24
Trojan.Win64.STEALER.USBLCO24
Trojan.Win64.STRELA.USBLCE24
Trojan.Win64.STRELA.USBLCF24
Trojan.Win64.STRELA.USBLCH24
Trojan.Win64.STRELA.USBLCI24
Trojan.Win64.STRELASTEALER.USBLCJ24
Trojan.Win64.STRELASTEALER.USBLCK24
Trojan.X97M.CVE.USBLCE24
Trojan.X97M.CVE.USBLCF24
TrojanSpy.MSIL.KRYPTIK.USBLCE24
TrojanSpy.MSIL.STEALERC.USBLCE24
TrojanSpy.Win32.CARDSPY.USBLCF24
TrojanSpy.Win32.FASONG.USBLCG24
TrojanSpy.Win32.QUKART.USBLCF24
TrojanSpy.Win32.REDLINE.USBLCF24
TrojanSpy.Win32.SNOJAN.USBLCE24
TrojanSpy.Win32.STEALC.USBLCM24
TrojanSpy.Win32.URSNIF.YXECOZ
TrojanSpy.Win32.ZPEVDO.USBLCF24
TrojanSpy.Win64.EXPIRO.USBLCE24
TrojanSpy.Win64.REDLINE.YXECOZ
TrojanSpy.Win64.STEALER.USBLCG24
TrojanSpy.Win64.STEALER.USBLCI24
Worm.Win32.DELF.USBLCF24
Worm.Win32.KOCEG.USBLCF24
Worm.Win32.LUDBARUMA.USBLCF24
Worm.Win32.RAMNIT.USBLCG24
Worm.Win32.SILENTALL.USBLCE24
Worm.Win32.VMPROTECT.USBLCG24
Trend Micro uses Advanced Threat Scan Engine which is fully cloud-based to scan files without a good reputation.
ATSE can block malware and identify the malware family (which can make it look like it’s definitions-based).
Detect emerging threats using Predictive Machine Learning
Use Predictive Machine Learning to detect unknown or low-prevalence malware. (For more information, see Predictive Machine Learning.)Predictive Machine Learning uses the Advanced Threat Scan Engine (ATSE) to extract file features and sends the report to the Predictive Machine Learning engine on the Trend Micro Smart Protection Network. To enable Predictive Machine Learning, perform the following:
As with all detected malware, Predictive Machine Learning logs an event when it detects malware. (See About Deep Security event logging.) You can also create an exception for any false positives. (See Create anti-malware exceptions.)
Ensure Internet connectivity
Predictive Machine Learning requires access to the Global Census Service, Good File Reputation Service, and Predictive Machine Learning Service. These services are hosted in the Trend Micro Smart Protection Network. If your Deep Security Agents or Virtual Appliance cannot access the Internet directly, see Configure agents that have no internet access for workarounds.Detect emerging threats using Predictive Machine Learning | Deep Security
Predictive Machine Learning 
Trend Micro Predictive Machine Learning uses advanced machine learning technology to correlate threat information and perform in-depth file analysis to detect emerging unknown security risks through digital DNA fingerprinting, API mapping, and other file features. Predictive Machine Learning also performs a behavioral analysis on unknown or low-prevalence processes to determine if an emerging or unknown threat is attempting to infect your network.Predictive Machine Learning is a powerful tool that helps protect your environment from unidentified threats and zero-day attacks.
After detecting an unknown or low-prevalence file, Deep Discovery Web Inspector scans the file using the Advanced Threat Scan Engine (ATSE) to extract file features and sends the report to the Predictive Machine Learning engine, hosted on the Trend Micro Smart Protection Network. Through use of malware modeling, Predictive Machine Learning compares the sample to the malware model, assigns a probability score, and determines the probable malware type that the file contains.
Depending on how you configure your policies, Deep Discovery Web Inspector can block the object to prevent the threat from continuing to spread across your network. Alternatively, you can configure the policy to monitor and log information about the object without blocking it.
https://docs.trendmicro.com/all/ent/ddwi/2.5/en-us/ddwi_2.5_olh/Predictive-Machine-L.html
Smart Protection Network integration is available for your computers and workloads through Anti-Malware and Web Reputation modules. Smart Feedback, which is set at the system level, allows you to provide continuous feedback to the Smart Protection Network.
For more about Trend Micro's Smart Protection Network, see Smart Protection Network.
If you are operating in a FedRAMP (Federal Risk and Authorization Management Program) environment, you cannot use Smart Feedback. If you have already enabled Smart Feedback, you must disable it.
In this topic:
Without Smart Scan enabled, your relay agents must download the full malware pattern from a Smart Protection Server to be used locally on the agent. The pattern is only updated as scheduled security updates are processed. The pattern is typically updated once per day for your agents to download and is around 120 MB.
Verify that the computer can reliably connect to the global Trend Micro Smart Protection Network URLs (see Port numbers for a list of URLs). If connectivity is blocked by a firewall, proxy, or AWS security group or if the connection is unreliable, it reduces Anti-Malware performance.
Client scanning can be performed in two methods:
For more about Trend Micro's Smart Protection Network, see Smart Protection Network.
If you are operating in a FedRAMP (Federal Risk and Authorization Management Program) environment, you cannot use Smart Feedback. If you have already enabled Smart Feedback, you must disable it.
In this topic:
- Anti-Malware and Smart Protection
- Web Reputation and Smart Protection
- Smart Feedback
- Disable Smart Feedback
Anti-Malware and Smart Protection
Benefits of Smart Scan
Smart Scan provides the following features and benefits:- Provides fast, real-time security status lookup capabilities in the cloud.
- Reduces the overall time it takes to deliver protection against emerging threats.
- Reduces network bandwidth consumed during pattern updates. The bulk of pattern definition updates only needs to be delivered to the cloud, not to many endpoints.
- Reduces the cost and overhead associated with corporate-wide pattern deployments.
Enable Smart Scan
Smart Scan is available in the Anti-Malware module. It leverages Trend Micro's Smart Protection Network to allow local pattern files to be small and reduces the size and number of updates required by agents and Appliances. When Smart Scan is enabled, the agent downloads a small version of the much larger full malware pattern from a Smart Protection Server. This smaller pattern can quickly identify files as either confirmed safe or possibly dangerous. Possibly dangerous files are compared against the larger complete pattern files stored on Trend Micro Smart Protection Servers to determine with certainty whether they pose a danger or not.Without Smart Scan enabled, your relay agents must download the full malware pattern from a Smart Protection Server to be used locally on the agent. The pattern is only updated as scheduled security updates are processed. The pattern is typically updated once per day for your agents to download and is around 120 MB.
Verify that the computer can reliably connect to the global Trend Micro Smart Protection Network URLs (see Port numbers for a list of URLs). If connectivity is blocked by a firewall, proxy, or AWS security group or if the connection is unreliable, it reduces Anti-Malware performance.
Detect emerging threats using Predictive Machine Learning | Deep Security
Client scanning can be performed in two methods:
- Conventional Scan
A scan method used in all earlier WFBS versions. A Conventional Scan client stores all Security Agent components on the client computer and scans all files locally. - Smart Scan
Smart Scan leverages threat signatures that are stored in the cloud. When in Smart Scan mode, the WFBS agent first scans for security risks locally. If the client cannot determine the risk of the file during the scan, the client connects to the local Smart Scan Server. If the clients cannot connect to it, they will attempt to connect to the Trend Micro Global Smart Scan Server.
Smart Scan provides the following features and benefits:- Provides fast, real-time security status lookup capabilities in the cloud.
- Reduces the overall time it takes to deliver protection against emerging threats.
- Reduces network bandwidth consumed during pattern updates. The bulk of pattern definition updates only needs to be delivered to the cloud and not to many endpoints.
- Reduces the cost and overhead associated with corporate-wide pattern deployments.
- Lowers kernel memory consumption on endpoints. Consumption increases minimally over time.
- Recent statistics shows that the Smart Scan Agent pattern (OTH, which is stored locally on the actual agent that uses Smart Scanning) covers 80% of the total threats, and that the Smart Scan pattern (TBL, stored on the Scan Server) covers the other 20%.
- Aside from Smart Scan Agent pattern (icrc$oth.xxx), a local cache is used to reduce about 80% of outgoing queries. CRC cache works as a partial Smart Scan Pattern replica so that previously obtained CRC can be reused later.
The release notes for the scan engine are here (only in Japanese):
VSAPI 22.610 / ATSE 22.610~23.570 Release date 2023.08.23
■New features of VSAPI 22.610 / ATSE 22.610~23.570
VSAPI 22.610 / ATSE 22.610~23.570 Release date 2023.08.23
■New features of VSAPI 22.610 / ATSE 22.610~23.570
- Added search function using machine learning
- (This is a local model type search function that is included inside the search engine.)
- Added and improved detection functions for new threats
- Supports identification of Lzip file types
- Improved identification function for MP3 file types
- Fixes for various bugs
Whilst I do not have evidence that the Trend Micro approach is in any way insufficient, there are few key issues which I see here and worth considering:
- Machine learning (ATSE) and behavioural blocking heavily focused on files/processes with low prevalence (read above). Trusted files and processes can be abused (Trend Micro may have found a way to handle this).
- Very cloud-based, offline protection poor (which shouldn't be that big of a deal)
- Business-focused, many programmes could have unfavourable reputation as they are not used on business environments and Trend Micro does not have sheer number of home users
- Dropping detections on malware that is not damaging anymore may be great for performance but I am unsure why hashes are not kept on the cloud; leaves a rather sour taste.
- Not enough information what files Predictive Machine Learning handles (apart from executables and documents) and what files are subjected to reputation checks.
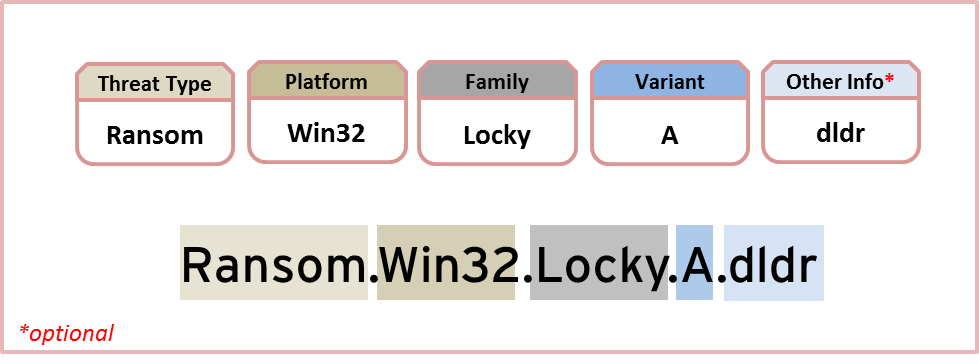
Starting July 2018, Trend Micro will apply a new Threat Detection Naming Scheme in order to align more closely with the rest of the industries in regards to the naming convention for threats and other malicious files.
Moving forward, Trend Micro will start to name malware and other threat detection patterns in alignment with the Computer Antivirus Research Organization (CARO) Malware Naming Scheme, follows the format as described below:
<Threat Type>.<Platform>.<Malware Family>.<Variant>.<Other info*>
*Optional
Below is a more detailed breakdown of the new format:
Trend Micro plans to implement this new detection naming scheme in a phased approach. The initial focus will be on customer submitted samples and noteworthy threats, and eventually will encompass all channels including bulk submissions and other sourcing methods.
We believe that aligning more closely with the CARO standards is beneficial for customers, especially those who use a mixed-vendor security environment and require cross-checking of threats.
We apologize in advance for any inconvenience this may cause, and encourage customers to contact their authorized Trend Micro support representative for any questions or concerns with the new naming scheme.
Moving forward, Trend Micro will start to name malware and other threat detection patterns in alignment with the Computer Antivirus Research Organization (CARO) Malware Naming Scheme, follows the format as described below:
<Threat Type>.<Platform>.<Malware Family>.<Variant>.<Other info*>
*Optional
Below is a more detailed breakdown of the new format:
Threat Type
The Threat Type represents the main threat category that describes what the main behavior of the threat is.- For malware: Trojan, Worm, Virus, Ransomware, Coinminer and Backdoor are the most common threat types that we use.
- For grayware: Adware, Spyware, and PUA are the most common threat types.
Platform
Platform refers to the environment in which the threat is designed to execute and covers both software and hardware. This would include Operating Systems: Windows (Win32, Win64), Mac OS, Linux, and Android, as well as programming languages (scripting language) and file formats (Microsoft Word/Excel/PowerPoint).Family
Threats with similar behavior are grouped together and referred to as a family. Each family is named based on the behavior it manifests.Variant
To identify different strains of malware under one family, letters are used in a sequential manner and referred to as the Variant.Other Information (Optional)
Information deemed useful in providing further insight for some complex threats can make use of this optional section of the naming scheme. For example, dldr means downloader. Therefore, the detection name Ransom.Win32.Locky.A.dldr provides information that this threat is a downloader for the Locky Ransomware.Trend Micro plans to implement this new detection naming scheme in a phased approach. The initial focus will be on customer submitted samples and noteworthy threats, and eventually will encompass all channels including bulk submissions and other sourcing methods.
We believe that aligning more closely with the CARO standards is beneficial for customers, especially those who use a mixed-vendor security environment and require cross-checking of threats.
We apologize in advance for any inconvenience this may cause, and encourage customers to contact their authorized Trend Micro support representative for any questions or concerns with the new naming scheme.
P.S. We need a few more TM tests, any users willing to participate, apart from @Shadowra who can retest at one point?
Last edited:

