New update has been pushed.
Introducing Network Monitor - the proper way.
The network monitor powered by Helios DynaTune/CSE allows risky connections to be spotted at a glance.
It works in conjunction with other modules such as Helios Web Marshall and takes into account a variety of factors for its overall score.
Some of them are displayed in a table.
The overall score is computed in real time and all connections are enriched.
For performance, the module uses aggressive caching and other optimisation tactics.
Full Intro:
Dynamically
Tuned Firewall and network monitor with memory, cloud intelligence and variable policies. That’s DynaTune.
Helios DynaTune: Your Network Has a Memory Now
Every application on your computer talks to the internet. Your browser, your email client, cloud storage, messaging apps — dozens of silent conversations happening every second. Most are perfectly normal. Some are not.
The challenge has always been telling the difference.
Traditional network monitors show you a snapshot: what’s connected right now. The moment a connection closes, it’s gone — no record, no context, no way to spot patterns over time. Helios DynaTune changes that fundamentally.
It Remembers Everything
DynaTune maintains a complete, encrypted history of every network connection your system has ever made. When you open the Network Monitor tomorrow, you don’t start from zero — you see the full picture. Connections that were active yesterday, last week, last month. Which servers your applications have contacted, when they first appeared, and when they were last active.
This history is encrypted and stored locally on your machine. Nobody else can read it — not even if they copy the file to another computer. It’s your data, on your machine, protected by Windows itself.
It Learns What’s Normal
The first time DynaTune sees Microsoft OneDrive connecting to a Microsoft server, it checks. It verifies the server’s identity, confirms the connection against cloud threat intelligence, and examines the process making the connection. Once verified, that knowledge persists. The next time OneDrive connects to the same server — even after a restart — DynaTune already knows it’s safe.
This means the system gets faster and more accurate the longer it runs. A fresh installation needs a few minutes to build its picture of your network. After a day of normal use, DynaTune knows your system’s baseline and can instantly identify anything unusual.
Deep, Multi-Layered Analysis
Every connection is evaluated from multiple angles simultaneously. DynaTune doesn’t rely on any single indicator — it builds a composite picture by examining the process, the destination, the behaviour, and the context together.
Is the process signed by a known publisher? Is the server owned by a recognised company? Does the binary show signs of being tampered with or disguised? Was it recently downloaded from the internet? Has the process been behaving consistently, or did it just appear and immediately start reaching out?
Each factor contributes to a single, easy-to-read risk score. Zero means everything checks out. Higher numbers mean more questions. The reasons are always explained in plain English — just clear statements like “Downloaded binary with active network connections” or “Process connecting to commonly abused infrastructure.”
Cloud Intelligence, Built In
DynaTune doesn’t work alone. Every address your computer contacts is checked against our cloud threat intelligence database. Known botnet command servers, phishing infrastructure, and malicious hosts are flagged immediately. Clean addresses receive a confidence boost that reduces their risk score.
This happens automatically in the background. You don’t need to configure anything, and it doesn’t slow down your connection.
It Knows Who’s Who
When a Microsoft-signed application connects to a Microsoft-owned server, DynaTune recognises the relationship. The process publisher matches the network owner — that’s expected behaviour. The risk drops accordingly.
But when a trusted process connects to an unknown server with no identifiable owner? That’s unusual. When an unsigned program connects to a hosting provider commonly associated with malicious activity? That’s flagged.
DynaTune understands the major network providers and can identify who owns the infrastructure on the other end of every connection. It knows the difference between a legitimate content delivery network and a hosting provider with a poor reputation.
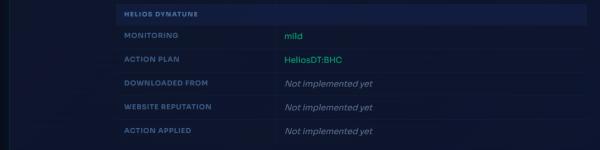
Attention Where It’s Needed
Not every process needs the same level of scrutiny. Trusted, signed applications with clean histories are monitored gently. Unsigned binaries, recently downloaded programs, or anything showing concerning behaviour receives closer attention and more frequent checks.
DynaTune assigns a monitoring level to every process — mild or aggressive — based on what it knows. This happens automatically and adjusts as the picture becomes clearer.
Action Plans, Not Just Alerts
Every process receives a DynaTune Action Plan based on its risk profile:
BHC — Block High Confidence Only. For trusted applications with clean records. Only confirmed threats would trigger a response. The lightest touch, reserved for software that has earned trust.
BMC — Block Medium Confidence. For processes with moderate risk indicators. Suspicious connections are handled individually while the process continues to operate.
BBD — Block by Default. For untrusted software showing suspicious characteristics. Network access is restricted until the application is analysed in depth.
GB — Global Block. For high-risk processes where multiple indicators align. All network access is blocked.
These plans are assigned automatically and adjust as new information becomes available.
*This is an early implementation that does not enforce policy yet. It has been released for users to get accustomed to the CSE.
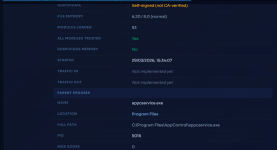
What You’ll See
When you expand any process in the Network Monitor, you see a complete intelligence briefing.
Process identity — who made it, where it’s installed, whether it’s visible on your screen. A signed application from Program Files that’s been there for months is very different from something that appeared in your Downloads folder this morning.
Binary integrity — whether the file carries proper metadata, whether it was downloaded from the internet, and whether its contents look normal or show signs of being deliberately obscured.
Runtime behaviour — whether the process contains code that shouldn’t be there, and whether all of its components come from trusted sources.
Lineage — which process launched this one, and whether the parent itself is trustworthy. A browser launched normally is expected. A networking tool launched through a chain of script interpreters is worth investigating.
Connection intelligence — when the connection was first seen, the server’s geographic location, the organisation that owns it, and what our cloud database says about it.
Your Network, Understood
Helios DynaTune transforms the Network Monitor from a simple connection list into a persistent intelligence system. It builds knowledge over time, remembers what it’s learned, investigates what it doesn’t recognise, and presents everything in a single, clear interface.
Every connection scored. Every process profiled. Every session remembered.