L
LabZero
Thread author
Hello.
Devices powered by Linux are increasing day by day, and most of these devices are positioned at the entry or key points of any organization’s network. Misconfigurations and easy to exploit vulnerabilities are commonly leveraged by bad actors. Many of these attacks can be studied by configuring low-interactive Honeypots.
Low-interactive Honeypots can capture the malware scripts and binaries, however analyzing these malware samples are also important. Further, keeping such analysis openly available helps independent researchers to search information of their interest and make useful conclusions.
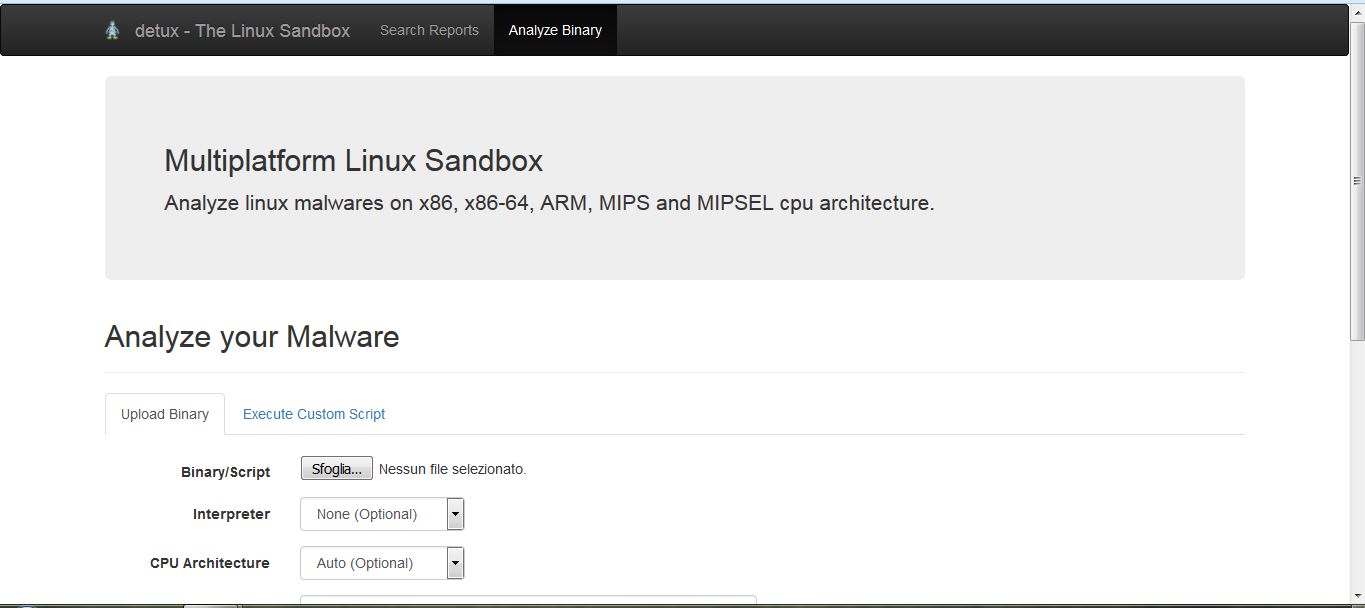
Detux aims at automating the analysis of Linux samples, by supporting multiple CPU architectures (ARM, MIPS, MIPSEL, x86 and x86-64), and making its result openly available for researchers.
detux - The Linux Sandbox
Devices powered by Linux are increasing day by day, and most of these devices are positioned at the entry or key points of any organization’s network. Misconfigurations and easy to exploit vulnerabilities are commonly leveraged by bad actors. Many of these attacks can be studied by configuring low-interactive Honeypots.
Low-interactive Honeypots can capture the malware scripts and binaries, however analyzing these malware samples are also important. Further, keeping such analysis openly available helps independent researchers to search information of their interest and make useful conclusions.
Detux aims at automating the analysis of Linux samples, by supporting multiple CPU architectures (ARM, MIPS, MIPSEL, x86 and x86-64), and making its result openly available for researchers.
detux - The Linux Sandbox