Hey MalwareTips community,
With ISPs logging everything, DoH/DoT now default in Windows 11/Edge/Chrome/Firefox, and encrypted DNS queries jumping 380% this year alone (Cloudflare Radar), the DNS wars are hotter than ever.
Your router or PC’s DNS choice is now one of the biggest privacy/security wins (or losses) you can make in 5 minutes.
Where are we in late 2025?
Drop your exact setup below!DoH or DoT? Encrypted Client Hello too?And the big one: did you finally ditch 1.1.1.1 for something with real custom filtering, or is raw speed still undefeated?
Let the DNS holy war begin!
With ISPs logging everything, DoH/DoT now default in Windows 11/Edge/Chrome/Firefox, and encrypted DNS queries jumping 380% this year alone (Cloudflare Radar), the DNS wars are hotter than ever.
Your router or PC’s DNS choice is now one of the biggest privacy/security wins (or losses) you can make in 5 minutes.
Where are we in late 2025?
- Cloudflare 1.1.1.1 – still fastest globally, added malicious-domain blocking (1.1.1.2) and family filter (1.1.1.3)
- Quad9 9.9.9.9 – strongest malware + phishing blocking out of the box, ECS support
- Google 8.8.8.8 – fastest for some regions but zero privacy
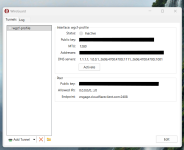
- NextDNS – custom blocklists, logs, analytics, per-device profiles, now with built-in AdGuard-style blocking and threat intel
- Control D – insane granularity (block TikTok on kid profile only, bypass geo for Netflix, etc.),
- AdGuard DNS – aggressive ad/tracker blocking + parental
- Mullvad DNS – zero logs, blocks trackers/malware (part of their $5/mo subscription or free)
- RethinkDNS – open-source Android/Windows app with firewall + DNS
Drop your exact setup below!DoH or DoT? Encrypted Client Hello too?And the big one: did you finally ditch 1.1.1.1 for something with real custom filtering, or is raw speed still undefeated?
Let the DNS holy war begin!
Last edited by a moderator: