Edge users take to social media to report their Web searches are being hijacked.
- Thread starter Tutman
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Gandalf_The_Grey
Level 85
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Forum Veteran
From that article:
There is also a fake uBlock Adblock Plus extension on the store that has not taken down while being reported by him and Nik Rolls.
I had a conversation with Raymond Hill the maker of uBlock Origin on Twitter.In a statement, Microsoft officials wrote: “We’re investigating the reported extensions listed and will take action as needed to help protect customers.” The statement follows comments in this Reddit comment in which someone identifying herself as a community manager for Microsoft Edge said the company is in the process of investigating the extensions.
“The team just updated me to let me know that anyone seeing these injections should turn off their extensions and let me know if you continue to see them at that point,” the person using the handle MSFTMissy wrote. “Once I have any news from them, I will update this thread accordingly.”
The maker of the legitimate TunnelBear software and browser extensions told me that the add-on hosted in Microsoft's official Edge store is a fake. It said there's an extension in the Chrome Web Store that's also fraudulent.
“We are taking action to have these removed from both platforms and investigating the matter with both Google and Microsoft,” a TunnelBear representative said. “It is not uncommon for popular, trusted brands like TunnelBear to be spoofed by malicious actors.”
None of the remaining four legitimate developers of the real extensions responded to a request for comment. Readers should remember, however, that legitimate developers can't be held responsible when their apps or add-ons are spoofed.
Along with Android apps, browser extensions are one of the weak links in the online security chain. The problem is that anyone can submit them, and Google, Mozilla, and now Microsoft haven’t come up with a system that adequately vets the authenticity of the people submitting them or the safety of the code.
Search engine redirections are typically part of a scheme to generate fraudulent revenue by ginning up ad clicks, and that's what's likely happening here. While reports indicate that the add-ons do nothing more than hijack legitimate searches, the privileges they require provide the possibility of doing much worse. Usage rights include things like:
Anyone who has installed any of the above-mentioned Edge add-ons should remove them immediately. And the oft-repeated advice about browser extensions still applies here: (1) install extensions only when they provide true value or benefit and even then (2) take time to read reviews and check the developer for any signs an extension is fraudulent.
- Reading and changing all your data on the websites you visit
- Managing your apps, extensions, and themes
- Changing your privacy-related settings
There is also a fake uBlock Adblock Plus extension on the store that has not taken down while being reported by him and Nik Rolls.
Gandalf_The_Grey
Level 85
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Forum Veteran
@silversurfer posted in the Edge Dev thread that those extensions are now pulled from the store 
Edge - Microsoft Edge Developers build info | MalwareTips Community
Edge - Microsoft Edge Developers build info | MalwareTips Community
Good! But I just use the chrome extension store for any add ons I use and not Microsoft's. (More offerings!) But dunno if necessarily safer! 
BTW I am verified now!? YAY!
BTW I am verified now!? YAY!
My NordVPN extension was deactivated automatically a few minutes ago, Edge say it was a security risk and deactivated automatically.
Did you get the extension from Microsoft Add-ons or Chrome Web Store? Does it de-activate if you get from Chrome Web Store?My NordVPN extension was deactivated automatically a few minutes ago, Edge say it was a security risk and deactivated automatically.
Gandalf_The_Grey
Level 85
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Forum Veteran
This story on Ghacks:
 www.ghacks.net
www.ghacks.net
Be careful when you install Microsoft Edge extensions from the Microsoft Store - gHacks Tech News
Microsoft removed malicious extensions from its Microsoft Edge extensions store, and not for the first time. You need to be careful when installing browser extensions.
Sites like Techdows published articles on the removal. According to the information, users of Edge opened support requests when they started to notice that searches were redirected when they used the Microsoft Edge browser.
It turned out that rogue extensions were responsible for that. All of these extensions were hosted on the official Microsoft Store; they used names of popular services and programs, e.g. NordVPN, Adguard VPN or The Great Suspender to lure users into installing the extensions.
Microsoft pulled the fake extensions from its web store and users who installed these in Edge will have them disabled on the next start of the browser automatically.
Raymone Hill, maker of the popular content blocker uBlock Origin, discovered another fake extension in the store that was based on an earlier version of uBlock Origin and manipulated website content to inject content on websites the user visited.
The two incidents suggest that users need to be very careful when installing extensions from the Microsoft Edge extensions store as Microsoft's protections are as weak as Google's protections on the Chrome Web Store.
In other words: there is always the chance that an extension is malicious in nature because of an insufficient vetting process. This leads to the following question: what can you do to protect yourself?
One of the best options is to analyze the code of the extension, but that is hardly something that all Edge users can do. Reviews and ratings help only so much, as they can be faked and sometimes, may not be available. You could look for reviews on trusted sites, or make sure that the company that supposedly created the extension has indeed created it by verifying that on the company site.
Now You: do you vet extensions before you install them?
Opera and Brave users don't see this problem with rogue ad-blockers.
conclusion: for now the safest and most reliable is Brave.
Gandalf_The_Grey
Level 85
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Forum Veteran
Opera and Brave users don't see this problem with rogue ad-blockers.
Unfortunately, that is not completely true because Brave gets its extensions from the Chrome Store.conclusion: for now the safest and most reliable is Brave.
That leaves Opera as probably the safest one for extensions, but they are often a version behind.
I'm not sure how Opera handles the vetting of extensions and when they have removed for example Nano adblocker.
You can also install extensions from Chrome in Opera and then they are as vulnerable as all the other browsers.
Gandalf_The_Grey
Level 85
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Forum Veteran
'The Great Suspender' extension is now flagged as malware, but Microsoft Edge has a built-in replacement:
Microsoft removes Scummy Extension ‘UBlock Adblock Plus’ from Edge Add-ons Store:
'The Great Suspender' extension is now flagged as malware, but Microsoft Edge has a built-in replacement | Windows CentralWhat you need to know
- Microsoft Edge now warns that "The Great Suspender" extension contains malware.
- The Great Suspender was recently sold to a new owner.
- Microsoft Edge has a similar feature that can be enabled through edge://flags.
Microsoft removes Scummy Extension ‘UBlock Adblock Plus’ from Edge Add-ons Store:
Microsoft removes Scummy Extension 'UBlock Adblock Plus' from Edge Add-ons Store (techdows.com)A few days back, Microsoft has removed some extensions from the Edge Add-ons store that hijacked the Search results. Yet another extension was gone. This time, it’s an adblocker named “UBlock Adblock Plus”. According to the UBlock Origin developer, the extension is based on an old version of UBO and it starts injecting iframe into all visited web pages after blocking 999 network requests.
Nop, from the NordVpn hit was install with the application. I believe it's a false positive, I never had problems with that extension.Did you get the extension from Microsoft Add-ons or Chrome Web Store? Does it de-activate if you get from Chrome Web Store?
- Aug 17, 2014
- 13,110
- 125,778
- 8,399

Microsoft removes 18 malicious Edge extensions for injecting ads into web pages
Some extensions mimicked official apps while others copied popular Chrome extensions.
 www.zdnet.com
www.zdnet.com
According to a list shared by a Microsoft community manager, the 18 extensions can be grouped into two categories. The first one is for extensions that tried to pass as the official versions of various apps, even if those apps didn't have official versions for Edge. This included:
- NordVPN
- Adguard VPN
- TunnelBear VPN
- Ublock Adblock Plus
- Greasemonkey
- Wayback Machine
The second list contained extensions that were copied from authentic Chrome extensions, ported to Edge, and then had malicious code inserted. This included:
- The Great Suspender
- Floating Player - Picture-in-Picture Mode
- Go Back With Backspace
- friGate CDN - smooth access to websites
- Full Page Screenshot
- One Click URL Shortener
- Guru Cleaner – cache and history cleaner
- Grammar and Spelling Checker
- Enable Right Click
- FNAF
- Night Shift Redux
- Old Layout for Facebook
Gandalf_The_Grey
Level 85
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Forum Veteran
Another one to add to the list:
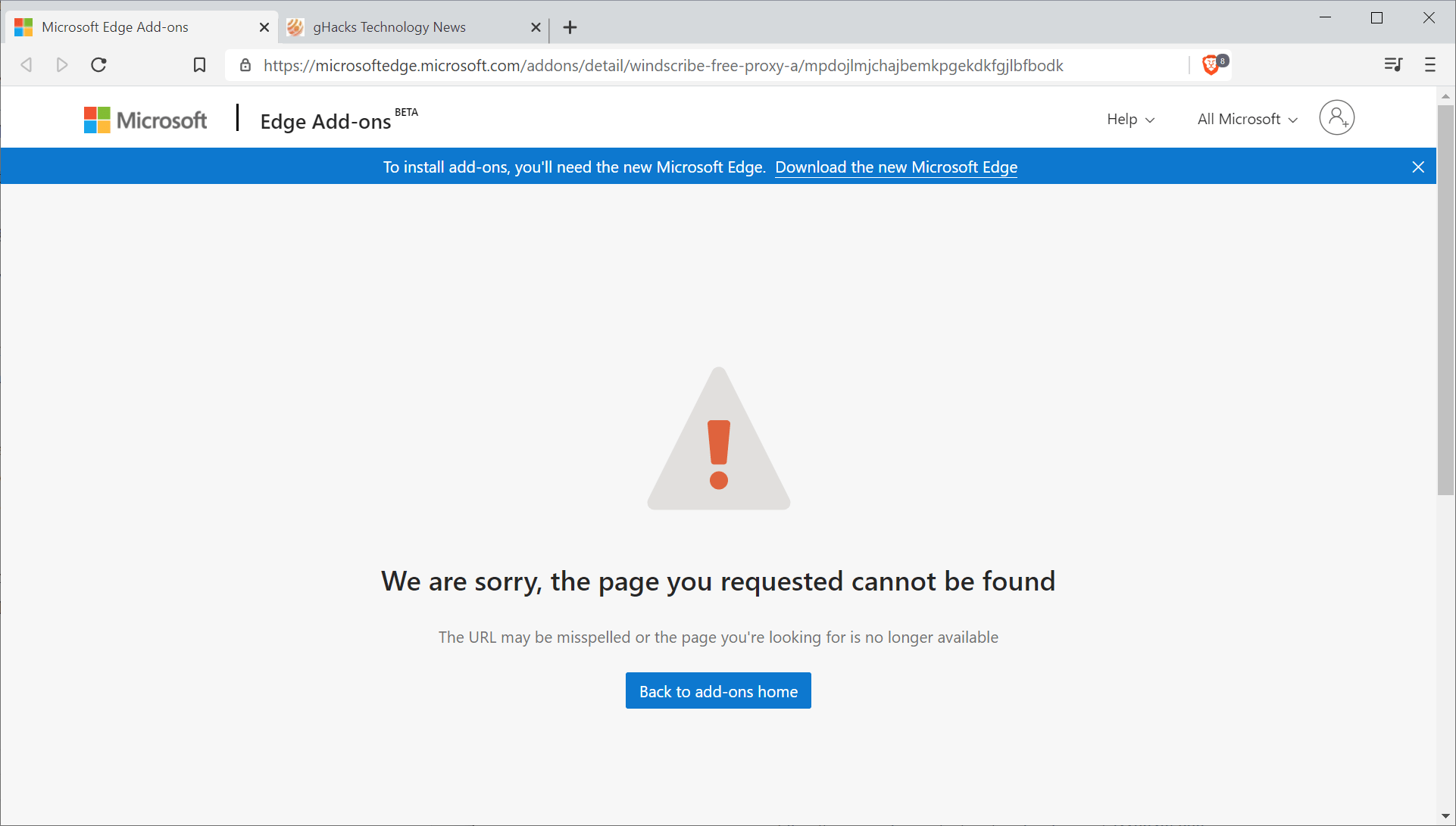
 www.ghacks.net
www.ghacks.net
The makers of Windscribe, a popular free and paid VPN providers, revealed yesterday that they have been a target as well. A fake Windscribe extension was uploaded to the Microsoft Store, and like all the others, accepted by Microsoft.
That was not our extensions, because MS review process is useless. Someone uploaded a modified version of the extension, and MS just approved it. We looked at it, it didn't seem to contain any actual malware at first glance, however we encourage you to change your Windscribe password.
Microsoft did flag the fake extension as malicious in the meantime. The extension is no longer available as a consequence, and users who have it installed should see it being disabled automatically in the browser. The real Windscribe extension that is created by the makers of the service is still in Microsoft's review queue. Affected users should consider changing passwords to the service, and maybe also to other services that they signed-in while using the extension.
Microsoft's review process did not catch the fake extensions that were released to the store in the past two weeks. It is not the first time that malicious extensions were made available in the store. If Microsoft does not change the review process, it is likely that it won't be the last time that users will install fake extensions from the official Edge extensions store.
It is recommended that users check with the maker of the product to see if a browser extension for Microsoft Edge is available before installing any extension from the Microsoft Store.
Microsoft has a fake extensions problem in its Microsoft Edge Store - gHacks Tech News
Microsoft has a serious problem with fake extensions for its Microsoft Edge web browser that are hosted on the company's own store for the web browser.Â
You may also like...
-
DarkSpectre Browser Extension Campaigns Exposed After Impacting 8.8 Million Users Worldwide
- Started by Gandalf_The_Grey
- Replies: 2
-
Massive browser hijacking campaign infects 2.3M Chrome, Edge users
- Started by HarborFront
- Replies: 3
-
F
-
Google's 7-year slog to improve Chrome extensions still hasn't satisfied developers
- Started by oldschool
- Replies: 9
-

