- Apr 28, 2015
- 9,098
ESET IS - April 2021 Report
C: Clean / P: Protected / P - NC: Protected - Not Clean / I: Infected / E: Encrypted
* Dynamic BB Bonus Test (Resident Protection Disabled)
* Partially Blocked
BSR: Before System Reboot
ASR: After System Reboot
H: Blocked by HIPS rules.
__Due to the small number of samples used in this tests, you should take results with a grain of salt. We encourage you to compare these results with others and take informed decisions on what security products to use.
C: Clean / P: Protected / P - NC: Protected - Not Clean / I: Infected / E: Encrypted
* Dynamic BB Bonus Test (Resident Protection Disabled)
* Partially Blocked
BSR: Before System Reboot
ASR: After System Reboot
H: Blocked by HIPS rules.
April 2021 | Samples Pack | Static Detection | Dynamic Detection | Total Detection | System Files Encrypted | 2nd Opinion Scanners | System Final Status | Thread Link |
|---|---|---|---|---|---|---|---|---|
01/04/2021 | 5 | 2 / 5 | 1* + 2 / 3 | 1* + 4 / 5 | No | C: HMP I: WV NPE | BSR: P - NC ASR: P - NC | |
02/04/2021 | 5 | 4 / 5 | 0 / 1 | 4 / 5 | No | C | P | |
03/04/2021 | 1 | 0 / 1 | 0 / 1 | 0 / 1 | No | I | BSR: I ASR: I | |
04/04/2021 | 5 | 3 / 5 | 0 / 2 | 3 / 5 | No | C: WV NPE I: NPE | BSR: I ASR: I | |
06/04/2021 | 15 | 9 / 15 | 1 + 1* / 6 | 10 + 1* / 15 | Files Wiped | N/A | I Files Wiped | |
06/04/2021 | 4 | 4 / 4 | N/A | 4 / 4 | No | C | C | |
07/04/2021 | 3 | 0 / 3 | 1 / 3 | 1 / 3 | No | C: WV HMP I: NPE | BSR: I ASR: I | |
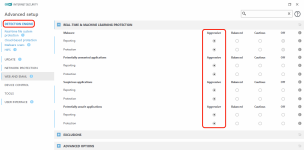
| AGGRESSIVE | SETTINGS | IN | REAL-TIME | MODULES | SEE | | |
08/04/2021 | 1 | 1 / 1 | N/A | 1 / 1 | No | C | C | |
09/04/2021 | 8 | 4 / 8 | 1* / 4 | 4 + 1* / 8 | No | C: HMP I: WV NPE | BSR: I ASR: I | |
15/04/2021 | 3 | 1 / 3 | 2* / 2 | 1 + 2* / 3 | No | C: WV NPE I: NPE | P - NC | |
17/04/2021 | 5 | 2 / 3 | 0 / 3 | 2 / 5 | No | C: WV NPE I: NPE | BSR: I ASR: I | |
18/04/2021 | 2 | 1 / 2 | 0 / 1 | 1 / 2 | No | C: WV HMP I: NPE | BSR: I ASR: I | |
19/04/2021 | 2 | 0 / 2 | 1* / 2 | 1* / 2 | No | C: HMP I: WV NPE | BSR: I ASR: I | |
20/04/2021 | 7 | 6 / 7 | 1 / 1 | 7 / 7 | No | C | P | |
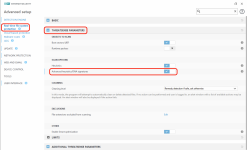
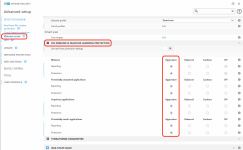
| HIPS | + | FIREWALL | TWEAKED RULES | AGAINST | RANSOMWARE | | |
23/04/2021 | 10 | 7 / 10 | 0 / 3 | 7 / 10 | No | C: WV NPE I: WV HMP | BSR: I P - NC | |
25/04/2021 | 10 | 8 / 10 | 2 (H) / 2 | 8 + 2 (H) / 10 | No | C | P | |
28/04/2021 | 6 | 3 / 6 | 3 (H) / 3 | 3 + 3 (H) / 6 | No | C | P | |
29/04/2021 | 2 | 1 / 2 | 1 / 1 | 2 / 2 | No | C | P |
Last edited: