[Guide] - Windows 10 Application Guard Setup and Configuration
- Thread starter valvaris
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
F
ForgottenSeer 823865
When I click new application guard window nothing happens. Anyone got any ideas?
Security baseline (FINAL) for Windows 10 v1909 and Windows Server v1909 | Microsoft Community Hub
Announcing the release of the security baseline for Windows 10 v1909 and Windows Server v1909. Relatively minor changes since the v1903 baselines, but...
Exploit Protection
Because of reported compatibility issues with the Exploit Protection settings that we began incorporating with the Windows 10 v1709 baselines, we have elected to remove the settings from the baseline and to provide a script for removing the settings from machines that have had those settings applied. (See Remove-EPBaselineSettings.ps1 in the download package’s Scripts folder.)
Umbra i tried running that script but i get an error "Cannot invoke method. Method invocation is supported only on core types in this language mode.". i looked at the xml file its pulling and manually remove those expoit rules but I'm still having those issues. I dont get why this doesn't work. I can open windows sandbox fine if that helps.
F
ForgottenSeer 823865
Exploit Protection as many built-in security features are non-user friendly at best, or half-baked at worst. One must be really adept to figure out all intricacies.
If you have average skills and knowledge, you better go with a 3rd party tool like HMPA.
If you have average skills and knowledge, you better go with a 3rd party tool like HMPA.
Umbra i tried running that script but i get an error "Cannot invoke method. Method invocation is supported only on core types in this language mode.". i looked at the xml file its pulling and manually remove those expoit rules but I'm still having those issues. I dont get why this doesn't work. I can open windows sandbox fine if that helps.
just upgrade windows 10 to 1909 and the rules will be taken care of for you by Microsoft
It's already on 1909just upgrade windows 10 to 1909 and the rules will be taken care of for you by Microsoft
If you plan on using VMWare or VirtualBox, then you cannot simultaneously use WDAC.
None of us can figure out what Microsoft was thinking when it developed WDAC, the sandbox and core isolation when most of the IT working world uses a non-Windows virtualization product on their systems.
None of us can figure out what Microsoft was thinking when it developed WDAC, the sandbox and core isolation when most of the IT working world uses a non-Windows virtualization product on their systems.
VMware has a technical release of their hyper v base version.If you plan on using VMWare or VirtualBox, then you cannot simultaneously use WDAC.
None of us can figure out what Microsoft was thinking when it developed WDAC, the sandbox and core isolation when most of the IT working world uses a non-Windows virtualization product on their systems.
VMware has a technical release of their hyper v base version.
It should not be VMWare's responsibility to accommodate Microsoft.
Besides, most people don't want to use Hyper-V. It is notorious for not working properly on older hardware whereas VMWare and VBox work just fine.
Hello @Shiz
I have to confirm what @polishpatriot sez never mix and match Hyper-V with VMware. Those two simply hate each other under the same translation level of the OS. Both are a Type 2 Hypervisor's even Application Guard has Hyper-V at hart like that it uses a Type 2 Hypervisor.
Here a link that explains the technical part from it: What Is A Hypervisor? Types Of Hypervisors 1 & 2
--------------- Quality of Life -----------
Even for me that uses Application Guard in Managed Mode - Sometimes wants to reset the container!
But how?
I created a shortcut on my desktop with the following command in it-> wdagtool.exe cleanup <- If you use a Persistant Layer in Application Guard you can use -> wdagtool.exe cleanup RESET_PERSISTENCE_LAYER <-
Just need to have a nice Symbol and Done!
Best regards
Val.
I have to confirm what @polishpatriot sez never mix and match Hyper-V with VMware. Those two simply hate each other under the same translation level of the OS. Both are a Type 2 Hypervisor's even Application Guard has Hyper-V at hart like that it uses a Type 2 Hypervisor.
Here a link that explains the technical part from it: What Is A Hypervisor? Types Of Hypervisors 1 & 2
--------------- Quality of Life -----------
Even for me that uses Application Guard in Managed Mode - Sometimes wants to reset the container!
But how?
I created a shortcut on my desktop with the following command in it-> wdagtool.exe cleanup <- If you use a Persistant Layer in Application Guard you can use -> wdagtool.exe cleanup RESET_PERSISTENCE_LAYER <-
Just need to have a nice Symbol and Done!
Best regards
Val.
Last edited:
Hello @Shiz
I have to confirm what @polishpatriot sez never mix and match Hyper-V with VMware. Those two simply hate each other under the same translation level of the OS. Both are a Type 2 Hypervisor's even Application Guard has Hyper-V at hart like that it uses a Type 2 Hypervisor.
Here a link that explains the technical part from it: How to Implement Validation for Restful Services with Spring
--------------- Quality of Life -----------
Even for me that uses Application Guard in Managed Mode - Sometimes wants to reset the container!
But how?
I created a shortcut on my desktop with the following command in it-> wdagtool.exe cleanup <- If you use a Persistant Layer in Application Guard you can use -> wdagtool.exe cleanup RESET_PERSISTENCE_LAYER <-
Just need to have a nice Symbol and Done!
Best regards
Val.
Thank you for the confirmation.
And another instance of Microsoft releasing features with zero common sense documentation... users have to discover what is what the hard way.
Code:
as usualYesterday I helped an uncle to setup his new laptop. While waiting for the data to copy from his desktop, I played with Application Guard Window. When enabling the edge flag "Application guard Prelaunch" and the Group Policy setting to pre-load Edge, this virtualized browser loads really fast (a lot faster than sandboxie on my old laptop  )
)
I discovered that there is group policy setting (thanks to this guide ) to enable persistent data. This does not flush the sandbox, so my browser settings, bookmarks and extensions survive reboot. I could not find a way not the info on the web to create a shortcut which launches Edge in a virtualized windows (as is possible with inPrivate mode).
) to enable persistent data. This does not flush the sandbox, so my browser settings, bookmarks and extensions survive reboot. I could not find a way not the info on the web to create a shortcut which launches Edge in a virtualized windows (as is possible with inPrivate mode).
Any tips welcome to start Edge in this mode (using a shortcut or switch). Anyone knows??????
I discovered that there is group policy setting (thanks to this guide
Any tips welcome to start Edge in this mode (using a shortcut or switch). Anyone knows??????
F
ForgottenSeer 85179
From guide:Any tips welcome to start Edge in this mode (using a shortcut or switch). Anyone knows??????
[INFORMATION]
If Application Guard runs in MANAGED Mode - None of the above (manually stuff) is needed! (Tested on Microsoft Edge Chromium Stable/Dev. builds)
@Lenny_Fox I haven't tried it yet. Maybe I'll play around with it and see what I find.
So when you start Edge it runs in application guard window? Please explainFrom guide:
[INFORMATION]
If Application Guard runs in MANAGED Mode - None of the above (manually stuff) is needed! (Tested on Microsoft Edge Chromium Stable/Dev. builds)
In WDAG-mode of Edge the number keys didn't work well when I typed a number in the adress/search bar. Typing from the numberpad (numlock) was o.k.
Solution:
Go to task manager. Than go to the details tab and find "ctfmon.exe ". Change UAC virtualization to enable mode and restart explorer.
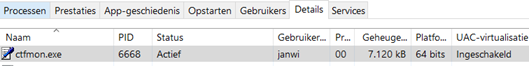
Solution:
Go to task manager. Than go to the details tab and find "ctfmon.exe ". Change UAC virtualization to enable mode and restart explorer.
Hello @Lenny_FoxSo when you start Edge it runs in application guard window? Please explain
sorry for the late reply. YES if Edge opens a site in a untrusted zone it will open in Application Guard.
Best regards
Val.
When I wrote this message, it was a coincidence that I had SpyShelter disabled (which I usually do when I update drivers). Now I know that the keystrokes encryption from SpyShelter is the real culprit in mutilation the top row numbers of the keyboard. I have added 'hvsirpcd.exe' to the excluded processes of the keystrokes encryption.In WDAG-mode of Edge the number keys didn't work well when I typed a number in the adress/search bar. Typing from the numberpad (numlock) was o.k.
Solution:
Go to task manager. Than go to the details tab and find "ctfmon.exe ". Change UAC virtualization to enable mode and restart explorer.
View attachment 244205
F
ForgottenSeer 85179
Or just don't use that program thenWhen I wrote this message, it was a coincidence that I had SpyShelter disabled (which I usually do when I update drivers). Now I know that the keystrokes encryption from SpyShelter is the real culprit in mutilation the top row numbers of the keyboard. I have added 'hvsirpcd.exe' to the excluded processes of the keystrokes encryption.
You may also like...
-
New Update Microsoft removing Defender Application Guard from Office
- Started by Parkinsond
- Replies: 1
-
Privacy News Windows 11 24H2/25H2 Flaw Keeps Task Manager Running After You Close It
- Started by Brownie2019
- Replies: 5
-
Soft Organizer Pro from Chemtable for Free - Uninstall applications
- Started by BigWrench
- Replies: 9
-
Unmaintained Microsoft to discontinue Application Guard app and browser extensions in May 2024
- Started by silversurfer
- Replies: 4
