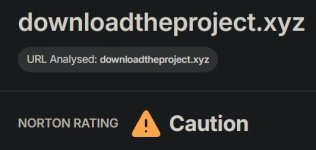
The attack starts when a victim is tricked into downloading a ZIP archive named Pumaproject.zip from the domain downloadtheproject[.]xyz.

Safeweb
Display file properties before exectuion.The archive contains a file called Document.docx.exe, designed to look like a harmless Word document.
Enable "Block use of copied or impersonated system tools" ASR rule to block the Python interpreter.When the victim runs it, the malware springs into action, extracting a Python interpreter, several Python libraries, and malicious scripts, while creating a hidden folder called “Dots” to store the remaining attack components.
Inside the “Dots” folder, the attackers store a legitimate WinRar binary renamed as picture.png, alongside an encrypted archive disguised as Shodan.pdf.
Its contents land in C:\Users\Public\WindowsSecure, and the Python interpreter is renamed to svchost.exe to pass as a trusted Windows process.
Enable "Block execution of potentially obfuscated scripts" ASR rule; it might help blocking the Python script.A heavily obfuscated Python script, disguised as images.png, is then launched with the $BOT_ID argument pointing to “Verymuchxbot.”
The script hooks into the victim’s browsers to intercept credentials and crypto wallet data during active sessions.
All stolen data is finally sent out over Telegram to attacker-controlled channels.
Outbound connections to top-level domains such as .xyz, .shop, .info, and .net should be blocked.

Hackers Use Phishing ZIP Files to Deploy PXA Stealer Against Financial Firms
PXA Stealer attacks rise, using phishing ZIP downloads to steal data, replacing Lumma and RedLine in global cybercrime campaigns.
 cybersecuritynews.com
cybersecuritynews.com