What is AdSMS ?
AdSMS is a Trojan horse for mobile phones running Android 2.1 or greater. It registers to service provider phone numbers and sends SMS to those phone numbers. Those tasks are done without consent of the victim.
The malicious package often disguises itself as a mobile phone update package.
Am I infected?
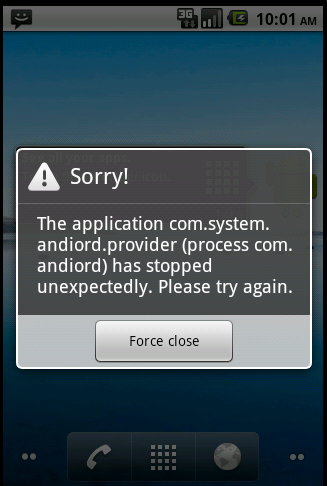
This is a screenshot of this malicious app.:
Removal Instructions
If you are still experiencing problems on your machine, please start a new thread here.
How can I prevent these infections?
The Android platform’s open nature makes it more attractive to cybercriminals than many other mobile operating systems. Even though the steps may seem obvious or overly simple, we can’t stress their importance enough.
AdSMS is a Trojan horse for mobile phones running Android 2.1 or greater. It registers to service provider phone numbers and sends SMS to those phone numbers. Those tasks are done without consent of the victim.
The malicious package often disguises itself as a mobile phone update package.
Am I infected?
This is a screenshot of this malicious app.:
Removal Instructions
- Open the Google Android Menu.
- Go to the Settings icon and select Applications.
- Next, click Manage.
- Select the application and click the Uninstall button.
If you are still experiencing problems on your machine, please start a new thread here.
How can I prevent these infections?
The Android platform’s open nature makes it more attractive to cybercriminals than many other mobile operating systems. Even though the steps may seem obvious or overly simple, we can’t stress their importance enough.
- Use your smartphone’s built-in security features - Knowing how to activate a smartphone’s security features is a step in the right direction. We strongly urge users to familiarize themselves with and take advantage of their smartphone’s built-in security features.
- Disable Wi-Fi auto-connect - To fulfill its intended final payload the Android malware needs to access several URLs to upload the stolen data. Enabling the Wi-Fi auto-connect option can help the malware do this faster. Disabling this option can delay or even prevent further infection.
- Block apps from third-party store
- Carefully review the permissions an app is asking for before allowing them.
- Verify the app’s publisher before installing it - It may serve better to carefully check details about the apps’ publishers, such as when they signed up for app developer registration, how many apps they’ve already published, and what their customers say about their apps. Users should be alarmed if they see well-known apps created by popular developers published or posted by new and unknown publishers. Knowing when the app was uploaded may also hint at its authenticity.
- Install a mobile security app - Last but not least, installing an effective mobile security app is highly recommended.
A security-conscious user should consider this attack as a test bed for more harmful cybercrimes in the future.
All major antivirus software vendors offer Mobile Security products :
Last edited: