What is PrivacyClear?
PrivacyClear is a fake system software that is considered as a Rogue. Rogues are malicious programs that hackers use to trick users by displaying false threats and problems that it claims to have detected. In reality, none of the issues are real and are only used to convince the user into buying their software and stealing their personal financial information
Am I infected?
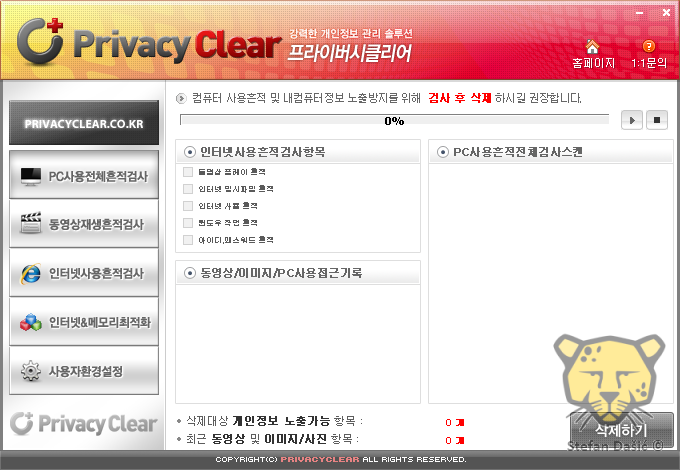
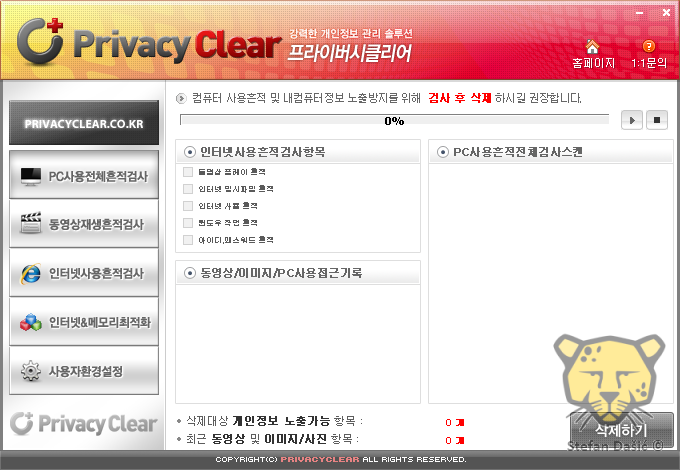
These are some screenshots of this rogue.

<h1>How to remove PrivacyClear (Removal Instructions)</h1>
If you experience any problems completing these instructions, please start a new thread here
<h2>STEP 1 : Start your computer in Safe Mode with Networking</h2>
<br>
<img title="Safe Mode with Networking screen" src="http://malwaretips.com/images/removalguide/safemode.jpg" alt="[Image: Safemode.jpg]" width="539" height="292" border="0" /></li>
</ol>
<h2> Step 2: Download and run RKill</h2>
Download mirror 1 - Download mirror 2 - Download mirror 3
<img title="RKILL LOG" src="http://malwaretips.com/images/removalguide/rkill3.png" alt="[Image: XP Defender 2013 rkill3.jpg]" width="414" height="187" border="0" /></li>
</ol><br>
<br><>WARNING: Do not reboot your computer after running RKill as the malware process will start again , preventing you from properly performing the next step.</>
<h2> Step 3: Download Malwarebytes' Anti-Malware(download link) to your desktop
 </h2>
</h2>
<h2>STEP 4: Remove any left over malicious files with HitmanPro</h2>
<ol>
<li>This step can be performed in <>Normal Mode</> ,so please <>download the latest official version of HitmanPro</>.
<a href="http://malwaretips.com/download-hitmanpro" rel="nofollow" target="_blank"> <>HITMANPRO DOWNLOAD LINK</></a> <em>(This link will open a download page in a new window from where you can download HitmanPro)</em></li>
<li><>Double click on the previously downloaded file</> to start the HitmanPro installation.
<img title="HitmanPro Installer" src="http://malwaretips.com/images/removalguide/hpro1.png" alt="[Image: hitmanpro-icon.png]" width="54" height="58" border="0" />
<>IF</> you are experiencing problems while trying to starting HitmanPro, you can use the "<em>Force Breach</em>" mode.To start this program in Force Breach mode,<> hold down the left CTRL-key when you start HitmanPro</> and all non-essential processes are terminated, including the malware process. (<a href="" target="_blank">How to start HitmanPro in Force Breach mode - Video</a>)</li>
<li>Click on <>Next </>to install HitmanPro on your system.
<img title="HitmanPro installation process" src="http://malwaretips.com/images/removalguide/hpro2.png" alt="[Image: installing-hitmanpro.png]" width="532" height="421" border="0" /></li>
<li>The setup screen is displayed, from which you can decide whether you wish to install HitmanPro on your machine or just perform a one-time scan, select a option then click on <>Next </>to start a system scan.
<img title="HitmanPro setup options" src="http://malwaretips.com/images/removalguide/hpro3.png" alt="[Image: hitmanpro-setup-options.png]" width="532" height="421" border="0" /></li>
<li>HitmanPro will start scanning your system for malicious files. Depending on the the size of your hard drive, and the performance of your computer, this step will take several minutes.
<img title="HitmanPro scanning for Win 8 Security System" src="http://malwaretips.com/images/removalguide/hpro4.png" alt="[Image: hitmanpro-scanning.png]" width="532" height="421" border="0" /></li>
<li>Once the scan is complete,a screen displaying all the malicious files that the program found will be shown as seen in the image below.After reviewing each malicious object click <>Next</>.
<img title="HitmanPro Win 8 Security System scan results" src="http://malwaretips.com/images/removalguide/hpro5.png" alt="[Image: hitmanpro-scan-results.png]" width="532" height="421" border="0" /></li>
<li>Click <>Activate free license </>to start the free 30 days trial and remove the malicious files.
<img title="Activate HitmanPro free license to remove detected infections" src="http://malwaretips.com/images/removalguide/hpro6.png" alt="[Image: hitmanpro-activation.png]" width="532" height="421" border="0" /></li>
<li>HitmanPro will now start removing the infected objects, and in some instances, may suggest a reboot in order to completely remove the malware from your system. In this scenario, always confirm the reboot action to be on the safe side.</li>
</ol>
Malwarebytes and HitmanPro should remove this infection. If you are still experiencing problems on your machine, please start a new thread here.
How was I infected?
How can I prevent these infections?
1. Keep Your System Updated
To manually update Windows,
2. Keep your Antivirus up-to-date
Make sure that you update your antivirus, firewall and anti-spyware programs regularly. If you don't have an antivirus, download any one of the following:
3. Keep other commonly exploited programs updated
PrivacyClear is a fake system software that is considered as a Rogue. Rogues are malicious programs that hackers use to trick users by displaying false threats and problems that it claims to have detected. In reality, none of the issues are real and are only used to convince the user into buying their software and stealing their personal financial information
Am I infected?
These are some screenshots of this rogue.

<h1>How to remove PrivacyClear (Removal Instructions)</h1>
If you experience any problems completing these instructions, please start a new thread here
<h2>STEP 1 : Start your computer in Safe Mode with Networking</h2>
- Remove all floppy disks, CDs, and DVDs from your computer, and then <>restart your computer</>.</li>
[*]<>Tap the "F8 key" continuously</> until you get the Advanced Boot Options screen.</li>
[*]On the Advanced Boot Options screen, use the arrow keys to <>highlight Safe Mode with Networking</> , and then <>press ENTER</>.
<br>
<img title="Safe Mode with Networking screen" src="http://malwaretips.com/images/removalguide/safemode.jpg" alt="[Image: Safemode.jpg]" width="539" height="292" border="0" /></li>
</ol>
<h2> Step 2: Download and run RKill</h2>
Download mirror 1 - Download mirror 2 - Download mirror 3
- Save it to your Desktop.
- Double click the RKill desktop icon.
- It will quickly run. If it does not run, try another download link from above.
- When Rkill has completed its task, it will <>generate a log</>. You can then <>proceed with the rest of the guide</>.
<img title="RKILL LOG" src="http://malwaretips.com/images/removalguide/rkill3.png" alt="[Image: XP Defender 2013 rkill3.jpg]" width="414" height="187" border="0" /></li>
</ol><br>
<br><>WARNING: Do not reboot your computer after running RKill as the malware process will start again , preventing you from properly performing the next step.</>
<h2> Step 3: Download Malwarebytes' Anti-Malware(download link) to your desktop

- Double-click mbam-setup.exe and follow the prompts to install the program.
- At the end, be sure a checkmark is placed next to
- Update Malwarebytes' Anti-Malware
- and Launch Malwarebytes' Anti-Malware
- then click Finish.
- Malwarebytes Anti-Malware will now start and you'll be prompted to start a trial period , please select '<>Decline</>'
<img title="Decline trial period in Malwarebytes Anti-Malware" src="http://malwaretips.com/images/removalguide/mbam3.PNG" alt="[Image: Decline Malwarebytes trial]" width="432" height="165" border="0" />
[*]If an update is found, it will download and install the latest version.

[*]Once the program has loaded, select Perform quick scan, then click Scan.
[*]When the scan is complete, click OK, then Show Results to view the results.

[*]Be sure that everything is Checked (ticked) and click on Remove Selected.
[*]Reboot your computer if prompted.
<h2>STEP 4: Remove any left over malicious files with HitmanPro</h2>
<ol>
<li>This step can be performed in <>Normal Mode</> ,so please <>download the latest official version of HitmanPro</>.
<a href="http://malwaretips.com/download-hitmanpro" rel="nofollow" target="_blank"> <>HITMANPRO DOWNLOAD LINK</></a> <em>(This link will open a download page in a new window from where you can download HitmanPro)</em></li>
<li><>Double click on the previously downloaded file</> to start the HitmanPro installation.
<img title="HitmanPro Installer" src="http://malwaretips.com/images/removalguide/hpro1.png" alt="[Image: hitmanpro-icon.png]" width="54" height="58" border="0" />
<>IF</> you are experiencing problems while trying to starting HitmanPro, you can use the "<em>Force Breach</em>" mode.To start this program in Force Breach mode,<> hold down the left CTRL-key when you start HitmanPro</> and all non-essential processes are terminated, including the malware process. (<a href="" target="_blank">How to start HitmanPro in Force Breach mode - Video</a>)</li>
<li>Click on <>Next </>to install HitmanPro on your system.
<img title="HitmanPro installation process" src="http://malwaretips.com/images/removalguide/hpro2.png" alt="[Image: installing-hitmanpro.png]" width="532" height="421" border="0" /></li>
<li>The setup screen is displayed, from which you can decide whether you wish to install HitmanPro on your machine or just perform a one-time scan, select a option then click on <>Next </>to start a system scan.
<img title="HitmanPro setup options" src="http://malwaretips.com/images/removalguide/hpro3.png" alt="[Image: hitmanpro-setup-options.png]" width="532" height="421" border="0" /></li>
<li>HitmanPro will start scanning your system for malicious files. Depending on the the size of your hard drive, and the performance of your computer, this step will take several minutes.
<img title="HitmanPro scanning for Win 8 Security System" src="http://malwaretips.com/images/removalguide/hpro4.png" alt="[Image: hitmanpro-scanning.png]" width="532" height="421" border="0" /></li>
<li>Once the scan is complete,a screen displaying all the malicious files that the program found will be shown as seen in the image below.After reviewing each malicious object click <>Next</>.
<img title="HitmanPro Win 8 Security System scan results" src="http://malwaretips.com/images/removalguide/hpro5.png" alt="[Image: hitmanpro-scan-results.png]" width="532" height="421" border="0" /></li>
<li>Click <>Activate free license </>to start the free 30 days trial and remove the malicious files.
<img title="Activate HitmanPro free license to remove detected infections" src="http://malwaretips.com/images/removalguide/hpro6.png" alt="[Image: hitmanpro-activation.png]" width="532" height="421" border="0" /></li>
<li>HitmanPro will now start removing the infected objects, and in some instances, may suggest a reboot in order to completely remove the malware from your system. In this scenario, always confirm the reboot action to be on the safe side.</li>
</ol>
Malwarebytes and HitmanPro should remove this infection. If you are still experiencing problems on your machine, please start a new thread here.
How was I infected?
- Rogues can get on to computers without the user's consent through Drive-by downloads. When a user visits a compromised or infected website, the site immediately checks for any security vulnerabilities on the machine to inject the malicious code.
- Peer-to-peer (P2P) programs utorrent, Limewire, and Kazaa are frequently used by hackers to distribute malware
- Hackers can also trick the user into downloading a file, saying it is a legitimate file needed to view a video or pictures.
How can I prevent these infections?
1. Keep Your System Updated
- Microsoft releases patches for Windows and Office products regularly to patch up Windows and Office product bugs and vulnerabilities. Please ensure you update your system regularly.
To update Windows and Office
1. Go to Start > Control Panel > Automatic Updates
2. Select Automatic (recommended) if you want the updates to be downloaded and installed without prompting you.
3. Select Download updates for me, but let me choose when to install them button if you want the updates to be downloaded automatically but to be installed at another time.
To manually update Windows,
Start Internet Explorer. Go to Tools > Windows Update
2. Keep your Antivirus up-to-date
Make sure that you update your antivirus, firewall and anti-spyware programs regularly. If you don't have an antivirus, download any one of the following:
- Avira AntiVir Personal- Free anti-virus software for Windows. Detects and removes more than 50000 viruses. Free support.
- avast! 7 Home Edition - Anti-virus program for Windows. The home edition is freeware for noncommercial users.
- Microsoft Security Essentials - Free anti-virus program for Windows.
3. Keep other commonly exploited programs updated
- Java
- Adobe Reader
- Adobe Flash Player (If you have it)
4. Avoid Peer-to-peer programs- Peer-to-peer programs are legitimate but the files shared are extremely dangerous. Hackers often use fake file names to trick users into downloading malware.
5. Switch your browser- Firefox is a more secure, faster browser than Internet Explorer. Firefox contains less vulnerabilities, reducing the risk of drive-by downloads.
- Google Chrome is another good browser that is faster and more secure than Internet Explorer.
<h2> Files Associated with PrivacyClear </h2>
Code:Files: C:\Program Files\PrivacyClear\RCEngine.dll C:\Program Files\PrivacyClear\AddScheduler.exe C:\Program Files\PrivacyClear\RepairCode.exe C:\Program Files\PrivacyClear\uninst.exe C:\Program Files\PrivacyClear\adsub.dat C:\Program Files\PrivacyClear\filter.dll C:\Program Files\PrivacyClear\PrivacyClear.exe C:\Program Files\PrivacyClear\PrivacyClearMtr.exe C:\Program Files\PrivacyClear\PrivacyClearuck.exe
Last edited by a moderator: