One of the games i play is runescape/oldschool runescape and its quite popular game in mmorpg genre. Typical to mmorpg games is that every game tends to have their own currency like runescape has gold as currency....this gold is sold on 3rd party sites /blackmarkets for real money so the game is used as in real life money maker for some people
things i have seen in runescape to happen
- doxxing/ ddos
- botting for levels / gold
- advertising malware sites/ gold / service selling sites
+ many more illegal stuff
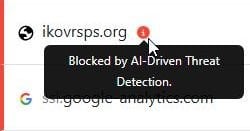
Currently there is phishing campaing going on wich noone is talking about ( i mean the runescape community)
In game there are bots advertising this runescape private server that once existed but was closed by jagex ( owns runescape)
Not many people know that the server made comeback with new name, but these phishers are using servers old name for this phishing campaing
In game bots are advertising this game like this

and when you type ikov into google

The logo, texturing and the site itselfs looks like legit private server
but if you download the client you download malware that is somekind of infostealer?
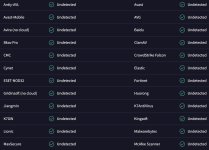
This scam has been going for 4 months wich is kinda strange, i mean there is every world in runescape being spammed by this server and still there is many antivirus vendors that wont block the site
My question is that, should the ''frontline'' page always be blocked and described as malware if the site itself contains malware but isnt malicious otherwise?
frontpage: VirusTotal
ps. reported to sophos, trend micro and mcafee and only sophos blocked the frontpage yet
things i have seen in runescape to happen
- doxxing/ ddos
- botting for levels / gold
- advertising malware sites/ gold / service selling sites
+ many more illegal stuff
Currently there is phishing campaing going on wich noone is talking about ( i mean the runescape community)
In game there are bots advertising this runescape private server that once existed but was closed by jagex ( owns runescape)
Not many people know that the server made comeback with new name, but these phishers are using servers old name for this phishing campaing
In game bots are advertising this game like this
and when you type ikov into google
The logo, texturing and the site itselfs looks like legit private server
but if you download the client you download malware that is somekind of infostealer?
This scam has been going for 4 months wich is kinda strange, i mean there is every world in runescape being spammed by this server and still there is many antivirus vendors that wont block the site
My question is that, should the ''frontline'' page always be blocked and described as malware if the site itself contains malware but isnt malicious otherwise?
frontpage: VirusTotal
ps. reported to sophos, trend micro and mcafee and only sophos blocked the frontpage yet
Last edited: