- Mar 29, 2018
- 7,136
Our experience in detecting and blocking threats on millions of endpoints tells us that attackers will stop at nothing to circumvent protections. Even one gap in security can be disastrous to an organization.
At Microsoft, we don’t stop finding new ways to fill in gaps in security. We go beyond strengthening existing defenses by introducing new and innovative layers of protection. While our industry-leading endpoint protection platform stops threats before they can even run, we continue improving protections for instances where sophisticated adversarial attacks manage to slip through.
Multiple layers of protection mean multiple hurdles that attackers need to overcome to perpetrate attacks. We continuously innovate threat and malware prevention engines on the client and in the cloud to add more protection layers that detect and block sophisticated and evasive threats before they can even run.
In recent months, we introduced two machine learning protection features within the behavioral blocking and containment capabilities in Microsoft Defender Advanced Threat Protection. In keeping with the defense in depth strategy, coupled with the “assume breach” mindset, these new protection engines specialize in detecting threats by analyzing behavior, and adding new layers of protection after an attack has successfully started running on a machine:
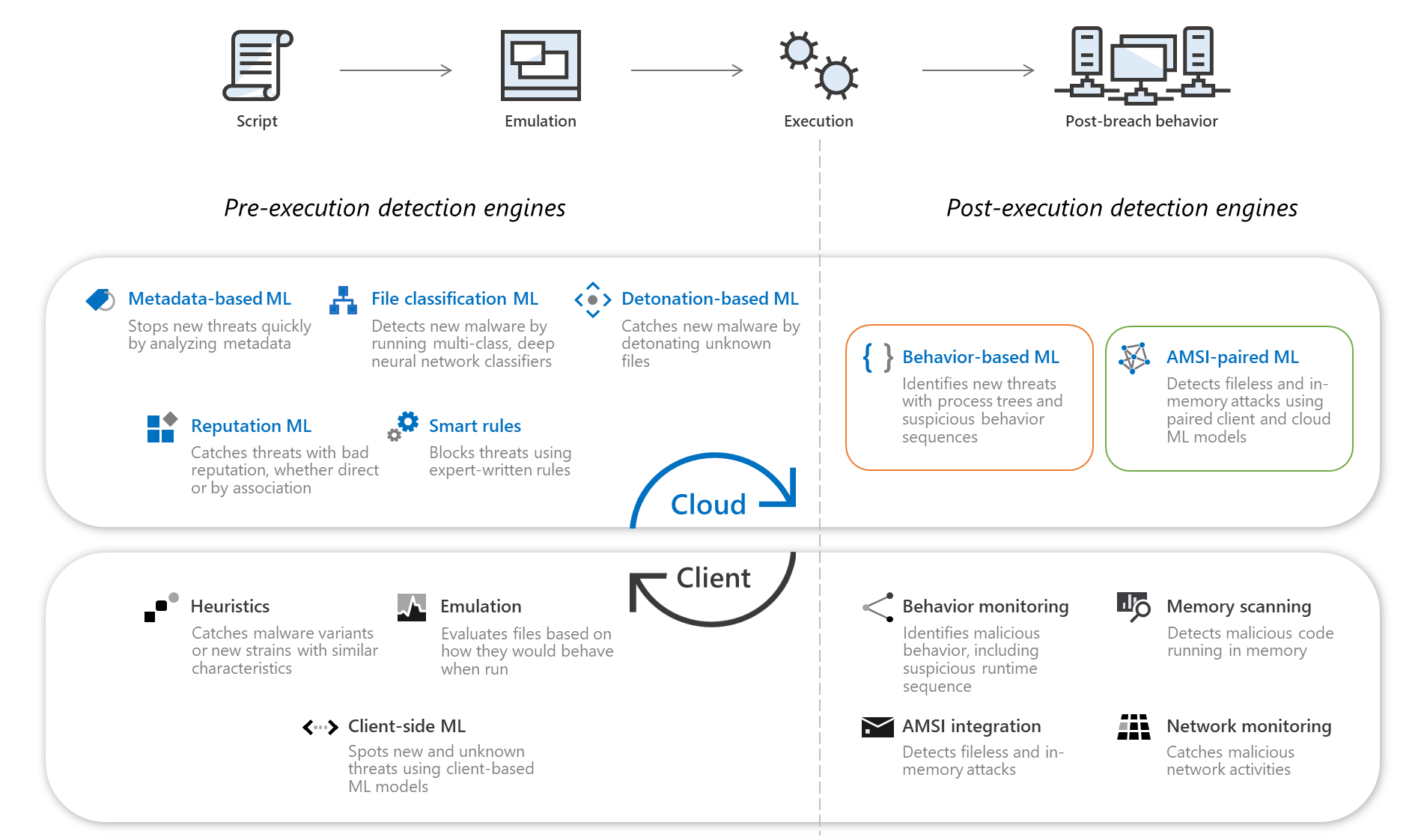
Figure 1. Pre and post-execution detection engines in Microsoft Defender ATP’s antivirus capabilities
The pre-execution and post-execution detection engines make up two important components of comprehensive threat and malware prevention. They reflect the defense in depth principle, which entails multiple layers of protection for thorough, wide-range defense.
In detecting post-execution behavior, using machine learning is critical. Many attack techniques are also used by legitimate applications. For example, a very common, documented method used by both clean applications and malware is creating a service for persistence.
To distinguish between malicious and clean applications when an attack technique is observed, Windows Defender Antivirus monitors and sends suspicious behaviors and process trees to the cloud protection service for real-time classification by machine learning. Cloud-based post-execution detection engines isolate known good behaviors from malicious intent to stop attacks in real time.
Within milliseconds of an attack technique or suspicious script execution being observed, machine learning classifiers return a verdict and the client blocks the threat. The pre-execution models then learn from these malicious blocks afterwards to protect Microsoft Defender ATP customers before attacks can begin executing new cycles of infection.
... continue reading here In hot pursuit of elusive threats: AI-driven behavior-based blocking stops attacks in their tracks - Microsoft Security
At Microsoft, we don’t stop finding new ways to fill in gaps in security. We go beyond strengthening existing defenses by introducing new and innovative layers of protection. While our industry-leading endpoint protection platform stops threats before they can even run, we continue improving protections for instances where sophisticated adversarial attacks manage to slip through.
Multiple layers of protection mean multiple hurdles that attackers need to overcome to perpetrate attacks. We continuously innovate threat and malware prevention engines on the client and in the cloud to add more protection layers that detect and block sophisticated and evasive threats before they can even run.
In recent months, we introduced two machine learning protection features within the behavioral blocking and containment capabilities in Microsoft Defender Advanced Threat Protection. In keeping with the defense in depth strategy, coupled with the “assume breach” mindset, these new protection engines specialize in detecting threats by analyzing behavior, and adding new layers of protection after an attack has successfully started running on a machine:
- Behavior-based machine learning identifies suspicious process behavior sequences and advanced attack techniques observed on the client, which are used as triggers to analyze the process tree behavior using real-time machine learning models in the cloud
- AMSI-paired machine learning uses pairs of client-side and cloud-side models that integrate with Antimalware Scan Interface (AMSI) to perform advanced analysis of scripting behavior pre- and post-execution to catch advanced threats like fileless and in-memory attacks
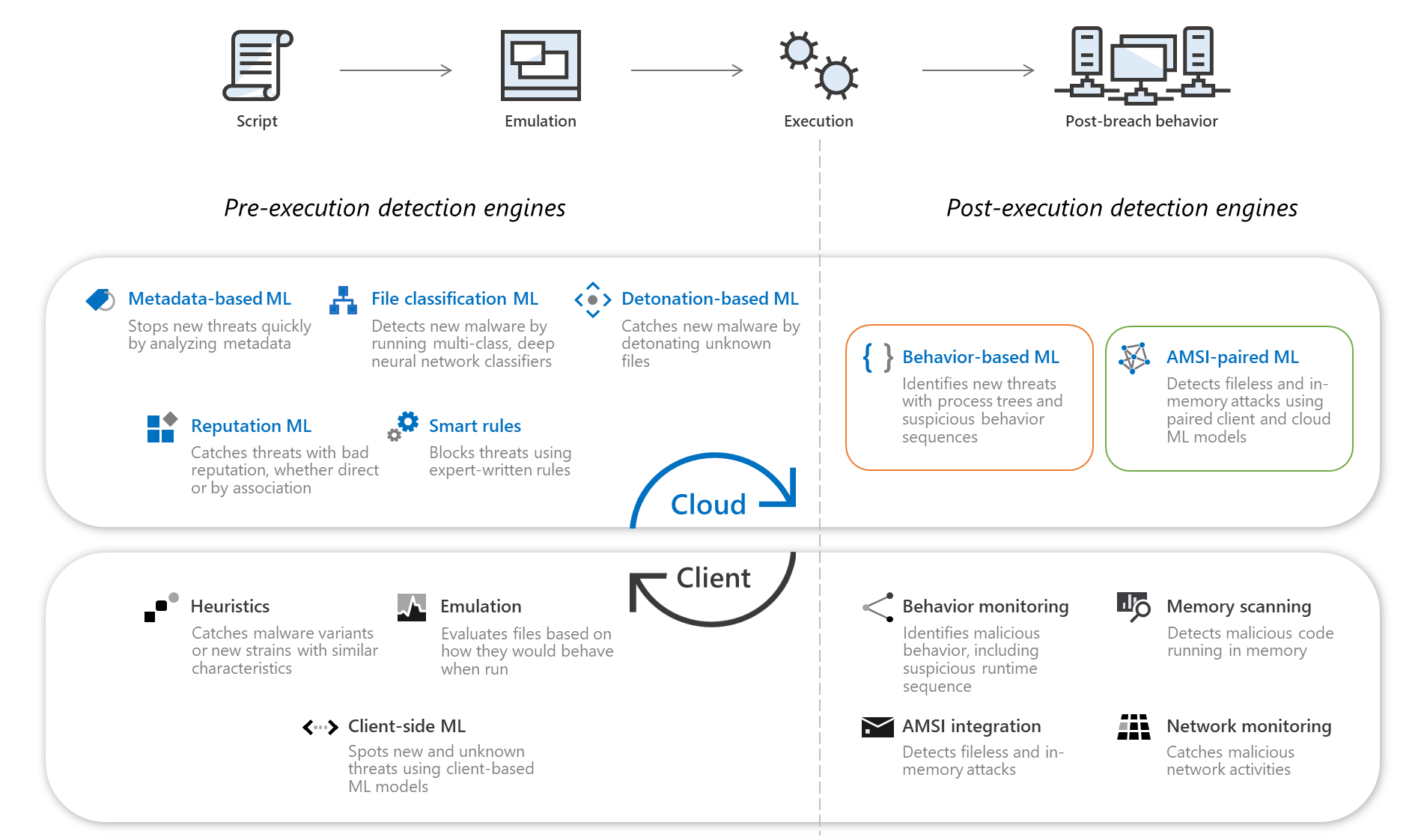
Figure 1. Pre and post-execution detection engines in Microsoft Defender ATP’s antivirus capabilities
The pre-execution and post-execution detection engines make up two important components of comprehensive threat and malware prevention. They reflect the defense in depth principle, which entails multiple layers of protection for thorough, wide-range defense.
In detecting post-execution behavior, using machine learning is critical. Many attack techniques are also used by legitimate applications. For example, a very common, documented method used by both clean applications and malware is creating a service for persistence.
To distinguish between malicious and clean applications when an attack technique is observed, Windows Defender Antivirus monitors and sends suspicious behaviors and process trees to the cloud protection service for real-time classification by machine learning. Cloud-based post-execution detection engines isolate known good behaviors from malicious intent to stop attacks in real time.
Within milliseconds of an attack technique or suspicious script execution being observed, machine learning classifiers return a verdict and the client blocks the threat. The pre-execution models then learn from these malicious blocks afterwards to protect Microsoft Defender ATP customers before attacks can begin executing new cycles of infection.
... continue reading here In hot pursuit of elusive threats: AI-driven behavior-based blocking stops attacks in their tracks - Microsoft Security

