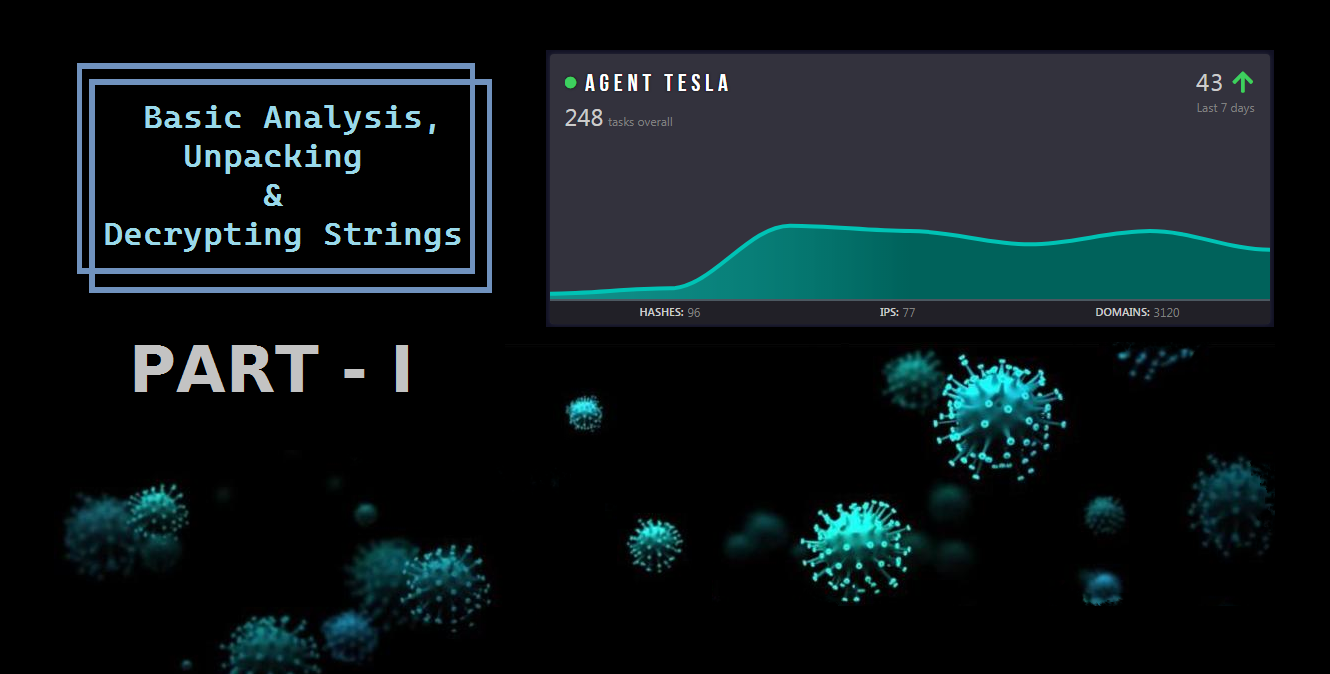
I'm having a hard time figuring out how to understand this interesting .NET malware that should be affiliated with Agent Tesla malware family.
From ANY.RUN, there are a lot of interesting behaviours and registry modification that I'd like to take a look and better understand it so I can write a final report on it.
The problem is that the main executable that should be the dropper, it seems to have 0 functionalities such as file creation, registry modification and so on.
It has no malicious code (imo) and has nothing to do with the final dropped service that it should create.
I'd appreciate any inputs that you guys can give me
MD5: 1a25e75693b99ad09e55aea29c6f2775
AnyRun: malware.exe (MD5: 1A25E75693B99AD09E55AEA29C6F2775) - Interactive analysis - ANY.RUN
From ANY.RUN, there are a lot of interesting behaviours and registry modification that I'd like to take a look and better understand it so I can write a final report on it.
The problem is that the main executable that should be the dropper, it seems to have 0 functionalities such as file creation, registry modification and so on.
It has no malicious code (imo) and has nothing to do with the final dropped service that it should create.
I'd appreciate any inputs that you guys can give me
MD5: 1a25e75693b99ad09e55aea29c6f2775
AnyRun: malware.exe (MD5: 1A25E75693B99AD09E55AEA29C6F2775) - Interactive analysis - ANY.RUN