Hey Guys!
I was wanting an app that would give me complete visibility and show me exactly what was going on with my data on the drives in real-time, especially when the hard drive light was going crazy. So I created a small app and kept adding features, and ended up building basically a lightweight, streamlined EDR for consumers and SMB’s, with a focus on ransomware.
So now we have RansomGuard EDR, which is a portable, self-contained .NET 8.0 app with all of the dependencies bundled in, so it will work even if you do not have the .NET 8.0 runtime installed. There is no uninstall, but if you do want to uninstall… simply toggle the Start with Windows to OFF, then delete the app and the C:\ProgramData\RansomGuard\ directory.
This version is more of a POC than anything, although it might offer some protection as it is. The app currently requires to be executed as administrator, but we might have an installable version with a proper Windows service if there is enough interest in this app, then it would no longer require administrator.
The best thing to do after first starting the app is to whitelist any safe but noisy processes you might have by right clicking on the process and choosing Whitelist Process. For me it is my backup software. There are already some that are hardcoded to be skipped, and if you guys send me a list of the ones that you whitelist, I can add them to the list. Just send me the list from the C:\ProgramData\RansomGuard\config.json file. Also, if you have any issues, you should be able to delete that file and it should fix the issue.
Also, if you encounter any user alert that is a false positive, please copy the contents of the user alert and either post it or email it to me. If you think it might have sensitive info, please email it to me instead of posting it.
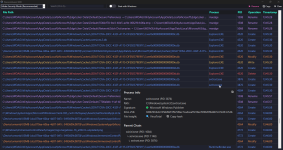
There are tons of little features within the app, for example, if you hover over the Process or PID columns, you will see information about that process. We currently do not cache processes that have exited, but we might in the future, as long as it does not significantly increase RAM utilization. BTW, the CPU utilization on my two machines is pretty much 0% most of the time and the RAM utilization is 65mb and 85mb on average. Which is not too bad considering that 35mb or so of that is due to the app being a self-contained file. Also, if you scroll up on the grid, it will pause the grid from auto scrolling, an you can scroll down fast or click the button at the top right to continue auto scrolling.
Several features are not active yet, including a lot of the actual protections and the Mode dropdown box at the top left, but now that all of the hard work is out of the way, these will be easy to finish up. I just wanted for you guys to see what we have so far, that way I can get some feedback.
We will be adding many features in the next few months, including monitoring VSS to ensure it is not tampered with, and also the ability to auto restore encrypted files from VSS. I was thinking about adding Sirius to the File insight section of the tooltip that you see when you hover over the Process and PID columns. We could even develop this into a full-fledged EDR .
.
It really is quite fascinating to see all of the drive activity and interactions in real-time. Now we can see what various software does to our system, and also see if it respects our privacy. If anyone finds anything interesting, please post it!
RansomGuard EDR POC
SHA-256: 83f9582b05596db6540729cce0dd04735e81231da86363827e93cc2679af8b74
Thank you guys!
Dan
I was wanting an app that would give me complete visibility and show me exactly what was going on with my data on the drives in real-time, especially when the hard drive light was going crazy. So I created a small app and kept adding features, and ended up building basically a lightweight, streamlined EDR for consumers and SMB’s, with a focus on ransomware.
So now we have RansomGuard EDR, which is a portable, self-contained .NET 8.0 app with all of the dependencies bundled in, so it will work even if you do not have the .NET 8.0 runtime installed. There is no uninstall, but if you do want to uninstall… simply toggle the Start with Windows to OFF, then delete the app and the C:\ProgramData\RansomGuard\ directory.
This version is more of a POC than anything, although it might offer some protection as it is. The app currently requires to be executed as administrator, but we might have an installable version with a proper Windows service if there is enough interest in this app, then it would no longer require administrator.
The best thing to do after first starting the app is to whitelist any safe but noisy processes you might have by right clicking on the process and choosing Whitelist Process. For me it is my backup software. There are already some that are hardcoded to be skipped, and if you guys send me a list of the ones that you whitelist, I can add them to the list. Just send me the list from the C:\ProgramData\RansomGuard\config.json file. Also, if you have any issues, you should be able to delete that file and it should fix the issue.
Also, if you encounter any user alert that is a false positive, please copy the contents of the user alert and either post it or email it to me. If you think it might have sensitive info, please email it to me instead of posting it.
There are tons of little features within the app, for example, if you hover over the Process or PID columns, you will see information about that process. We currently do not cache processes that have exited, but we might in the future, as long as it does not significantly increase RAM utilization. BTW, the CPU utilization on my two machines is pretty much 0% most of the time and the RAM utilization is 65mb and 85mb on average. Which is not too bad considering that 35mb or so of that is due to the app being a self-contained file. Also, if you scroll up on the grid, it will pause the grid from auto scrolling, an you can scroll down fast or click the button at the top right to continue auto scrolling.
Several features are not active yet, including a lot of the actual protections and the Mode dropdown box at the top left, but now that all of the hard work is out of the way, these will be easy to finish up. I just wanted for you guys to see what we have so far, that way I can get some feedback.
We will be adding many features in the next few months, including monitoring VSS to ensure it is not tampered with, and also the ability to auto restore encrypted files from VSS. I was thinking about adding Sirius to the File insight section of the tooltip that you see when you hover over the Process and PID columns. We could even develop this into a full-fledged EDR
It really is quite fascinating to see all of the drive activity and interactions in real-time. Now we can see what various software does to our system, and also see if it respects our privacy. If anyone finds anything interesting, please post it!
RansomGuard EDR POC
SHA-256: 83f9582b05596db6540729cce0dd04735e81231da86363827e93cc2679af8b74
Thank you guys!
Dan