I'm confused about core isolation feature in Windows 11 home edition, it is recommended to enable it by windows security and in the same time it is described as "Security features available on your device that use virtualization-based security" and virtualization-based security is not available in Windows 11 home edition.
But when I run the following command in terminal
source: Enable memory integrity
So can experts explain this and if core isolation working on Windows 11 home edition and how it works and does it have full functionality like Windows 11 pro edition, or it is a limited?
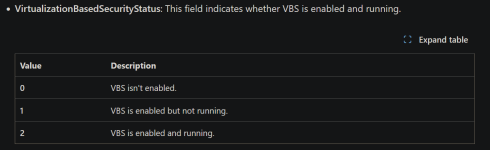
But when I run the following command in terminal
Get-CimInstance -ClassName Win32_DeviceGuard -Namespace root\Microsoft\Windows\DeviceGuard the result of "VirtualizationBasedSecurityStatus" shows "2" which means "VBS is enabled and running" based on Microsoft documentation.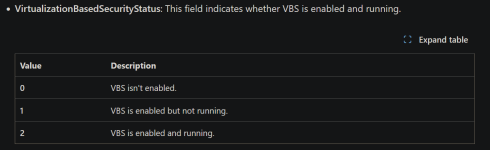
source: Enable memory integrity
So can experts explain this and if core isolation working on Windows 11 home edition and how it works and does it have full functionality like Windows 11 pro edition, or it is a limited?