- Dec 29, 2014
- 1,717
But keep in mind, for true zero days, a Windows patch simply does not exist, and as we all witnessed in the EB/DP attack, there is no guaranty that an anti-exploit can mitigate this attack either.
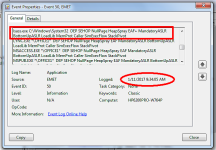
Must know if this is a reference to the video which was intended to show a test of EMET's capabilities for potentially mitigating such an attack. VS blocked the payload in the video I have seen, but EMET in the same video was 100% not enabled to protect against an attack against LSASS.exe. That application is an IT tool meant to be configured and deployed by a professional according to specific standard requirements. where more serious protection is required. At its defaults it covers very few processes, including these:
Recommended Software.xml: Enables mitigations for Microsoft Internet Explorer, WordPad, applications that are part of the Microsoft Office suite, Adobe Acrobat, Adobe Reader, and Oracle Java.
Popular Software.xml: Enables mitigations for other common applications.
I have a doubt whether EMET 5.5 set to cover lsass.exe would block EB/DP at the memory level, but the original video is not proof that it would not. If there has since been a test where lsass.exe was added to the list of protected processes, OK, the point is valid, and EMET doesn't necessarily at least block EB/DP. Otherwise, the test should be rerun correctly and recorded or claims that point to the notion that EMET could not block EB/DP should stop. JMO.