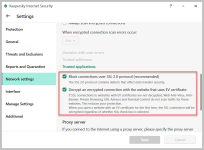
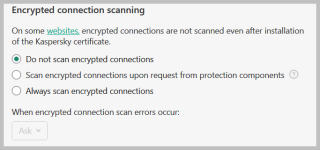
I have officially changed my stance on https scanning. I used to believe that it was necessary because ever site these days as a cert and without it the AV would be partially handicap without it. Well I've been using kaspersky on mac for maybe 3 months or so and they https injection has caused so many issues. You would think kaspersky would have this figure out by now but no. The first issue is it broke homebrew. Homebrew uses curl. By the error i got out of curl it looks like kaspersky was trying to do a tls downgrade attach (to tls1):
curl: (35) error:1400443E:SSL routines:CONNECT_CR_SRVR_HELLO:tlsv1 alert inappropriate fallback
Error: Failed to download resource "ncurses_bottle_manifest"
Download failed: https://ghcr.io/v2/homebrew/core/ncurses/manifests/6.2
Kaspersky "partially" fixed it but it was a total pain in the rear. They required me to do so much work on my side for them to fix the issue (from logs, to memory dumps, ect...). Thankfully i'm technical or it would have been impossible. You would think Kaspersky would have this figured out by now.
I do TimeMachine backups over my network. I've been fighting for months with it continuously failing after 2 or 3 backups (time machine backups happen every hour). I'd have to reboot and it would start working again until it started failing again after 2-3 hours. Well guess what it was? Kaspersky!!! After my first experience with their tech support i'm not going to do it again.
So from here on out any product that has https scanning i will immediately disable it. If it interface is kind of screaming at you that you're insecure because you disabled it then i won't use it. The hardest thing to give up will be adguard.
I was using bitdefender that doesn't have https scanning (in its mac product that is) but the issues with bitdefender from windows follows it to the mac side (it uses WAYYYY to much memory) so i bought kaspersky. At this point i'm not sure if i'm going to back to bitdefender or start trying alternatives (SHP comes to mind).
As aside my work has used websense, wsa (cisco web security appliance), and fortinet and they have all sucked. Everything will be working fine and thing just randomly break all the time. It almost requires someone looking into these issues full time. Granted i have heard with TLS 1.3 you no longer MTM TLS
curl: (35) error:1400443E:SSL routines:CONNECT_CR_SRVR_HELLO:tlsv1 alert inappropriate fallback
Error: Failed to download resource "ncurses_bottle_manifest"
Download failed: https://ghcr.io/v2/homebrew/core/ncurses/manifests/6.2
Kaspersky "partially" fixed it but it was a total pain in the rear. They required me to do so much work on my side for them to fix the issue (from logs, to memory dumps, ect...). Thankfully i'm technical or it would have been impossible. You would think Kaspersky would have this figured out by now.
I do TimeMachine backups over my network. I've been fighting for months with it continuously failing after 2 or 3 backups (time machine backups happen every hour). I'd have to reboot and it would start working again until it started failing again after 2-3 hours. Well guess what it was? Kaspersky!!! After my first experience with their tech support i'm not going to do it again.
So from here on out any product that has https scanning i will immediately disable it. If it interface is kind of screaming at you that you're insecure because you disabled it then i won't use it. The hardest thing to give up will be adguard.
I was using bitdefender that doesn't have https scanning (in its mac product that is) but the issues with bitdefender from windows follows it to the mac side (it uses WAYYYY to much memory) so i bought kaspersky. At this point i'm not sure if i'm going to back to bitdefender or start trying alternatives (SHP comes to mind).
As aside my work has used websense, wsa (cisco web security appliance), and fortinet and they have all sucked. Everything will be working fine and thing just randomly break all the time. It almost requires someone looking into these issues full time. Granted i have heard with TLS 1.3 you no longer MTM TLS